Stop unauthorized applications from running on endpoints.
Create rules to allow trusted applications and block risky or unapproved software.
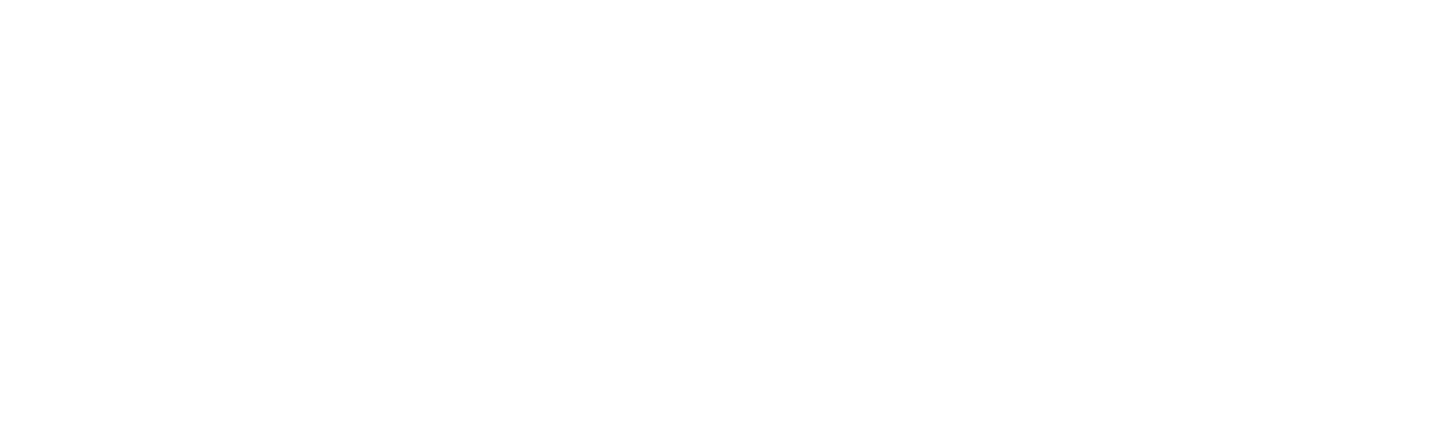
Audit unauthorized applications and block events
See what would be blocked before enforcement. Track unmanaged executions and block attempts.
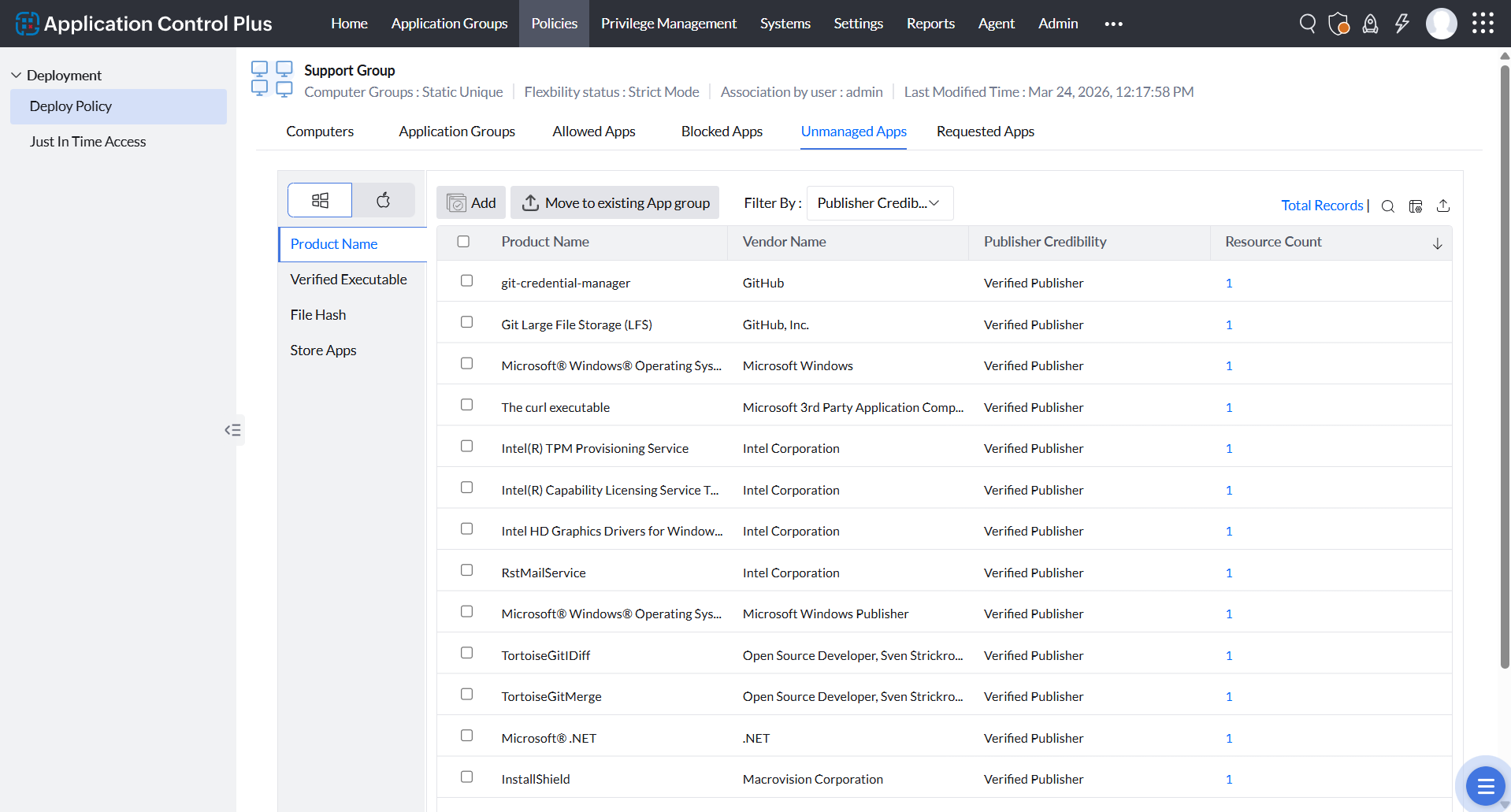
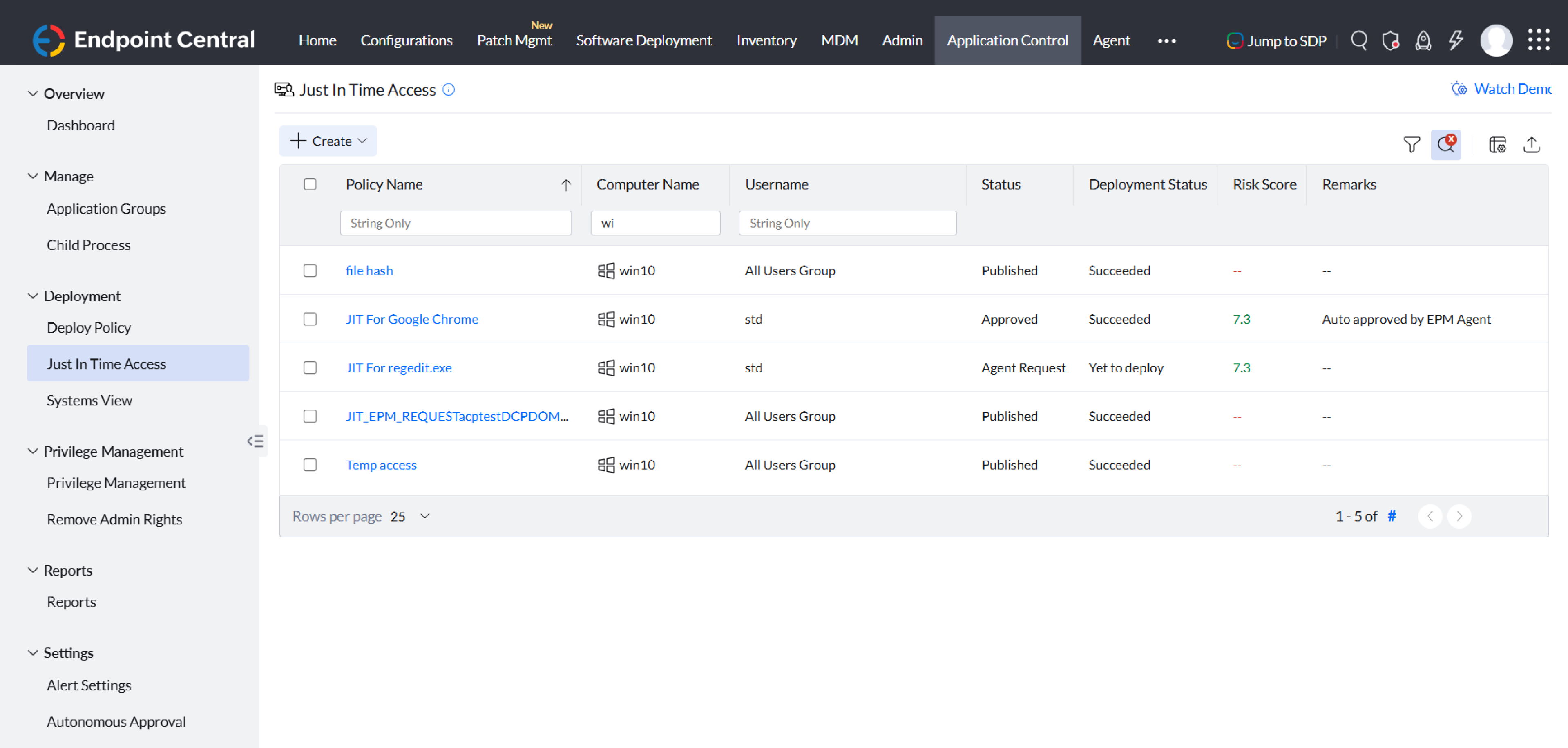
Just-in-time application access
Temporarily allow specific apps when needed and revoke access automatically.