Here are the step-by-step instructions for deploying Identity360's IDSecurity Agent for Windows using Group Policy Object (GPO).
Note: The document is written for an IT admin with a basic understanding of the Windows operating system, Active Directory (AD), and enterprise software deployment.
The IDSecurity Agent is an extension of the standard credential provider from Microsoft. When installed, it can enable MFA for local Windows logins, RDP logins, and UAC actions to protect machines from credential-based attacks.
The platforms supported by the IDSecurity Agent are listed below.
| Windows Server versions | Windows clients |
|---|---|
| Windows Server 2022 | Windows 11 |
| Windows Server 2019 | Windows 10 |
| Windows Server 2016 | Windows 8.1 |
| Windows Server 2012 R2 | Windows 8 |
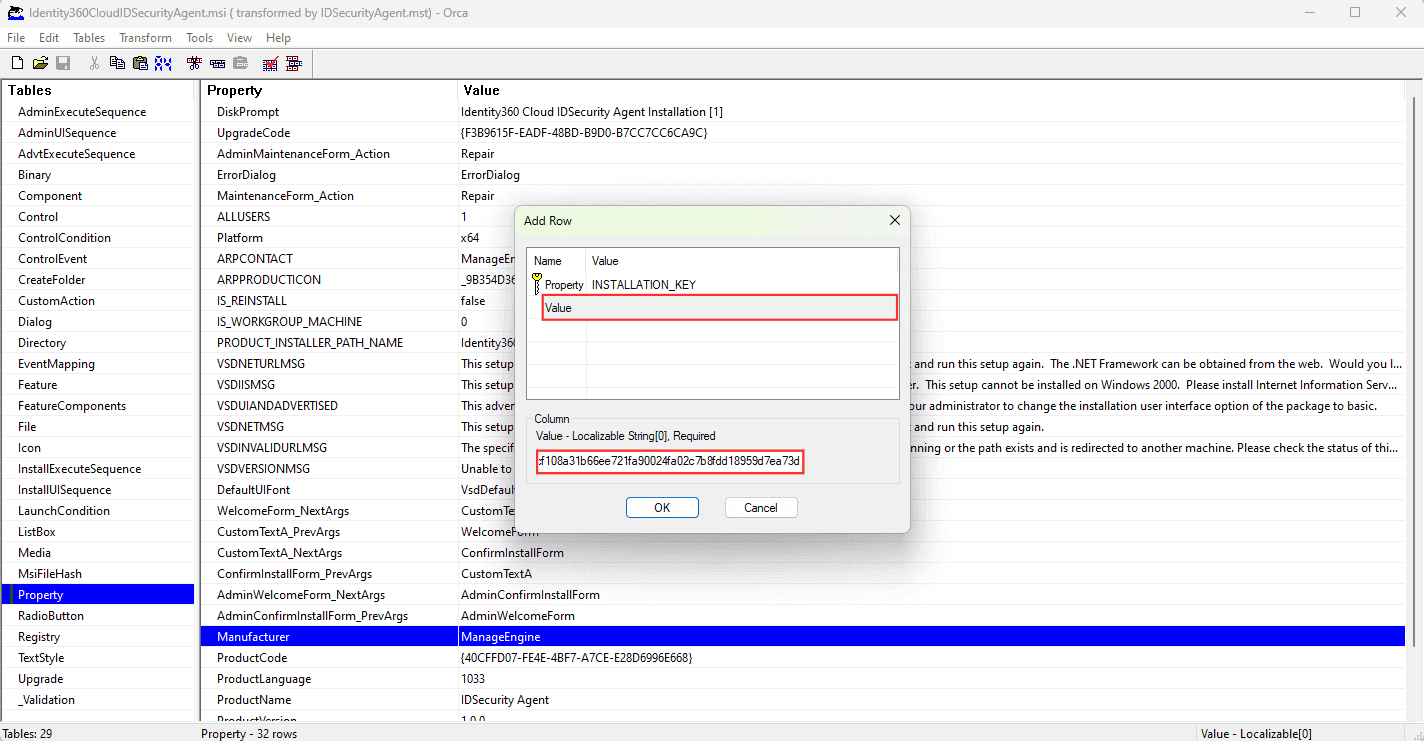
| Property | Value |
|---|---|
| INSTALLATION_KEY | Replace |
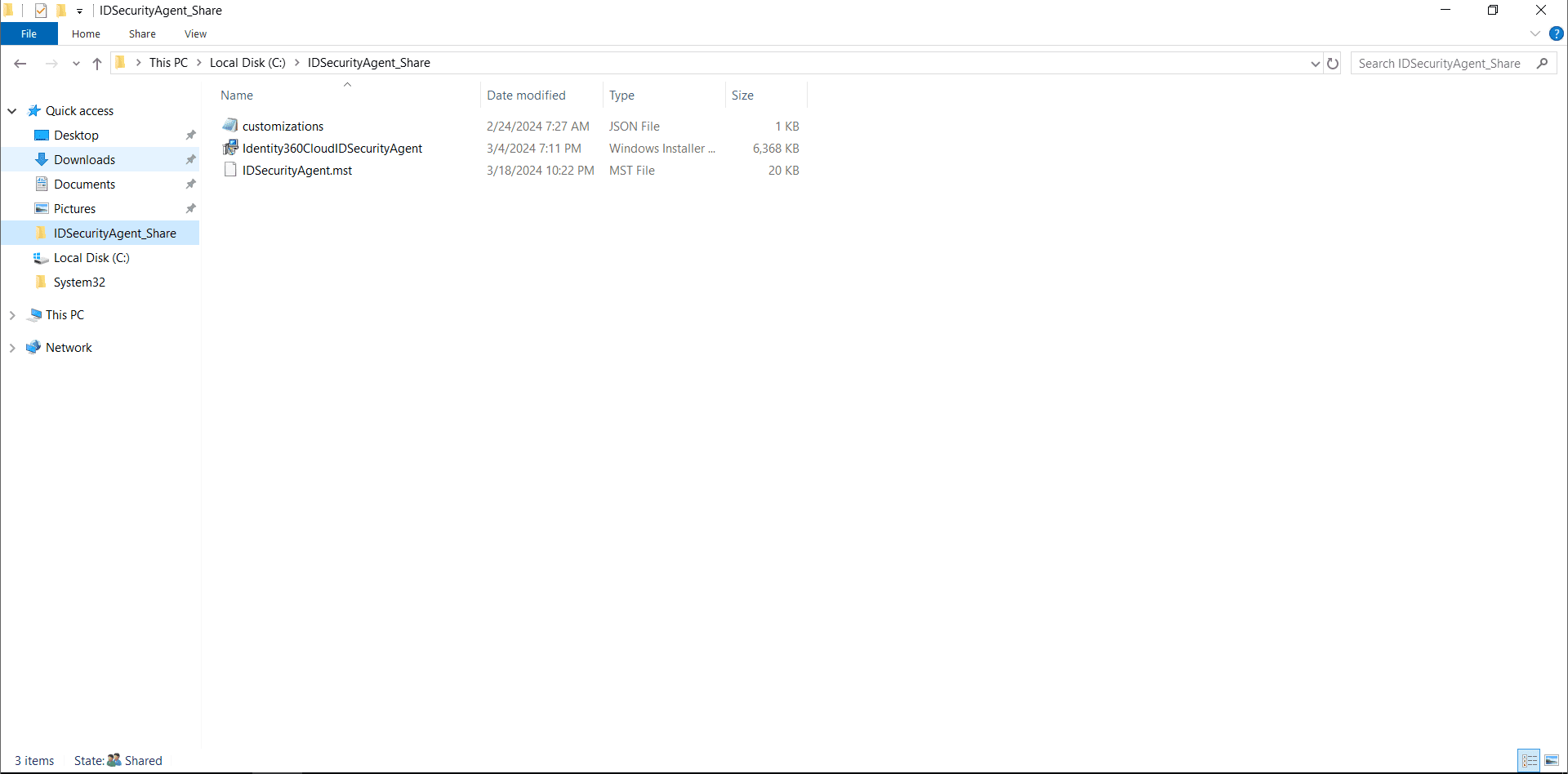
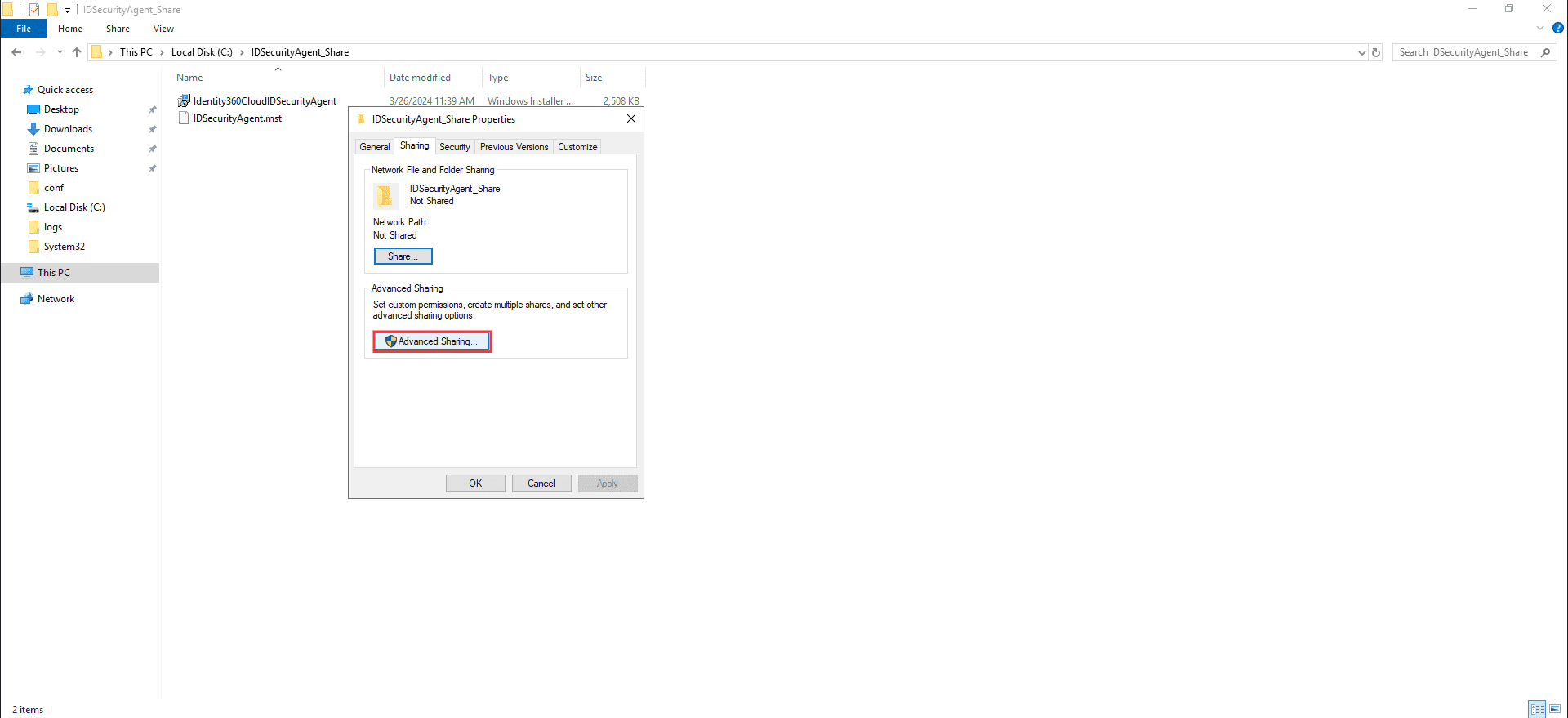
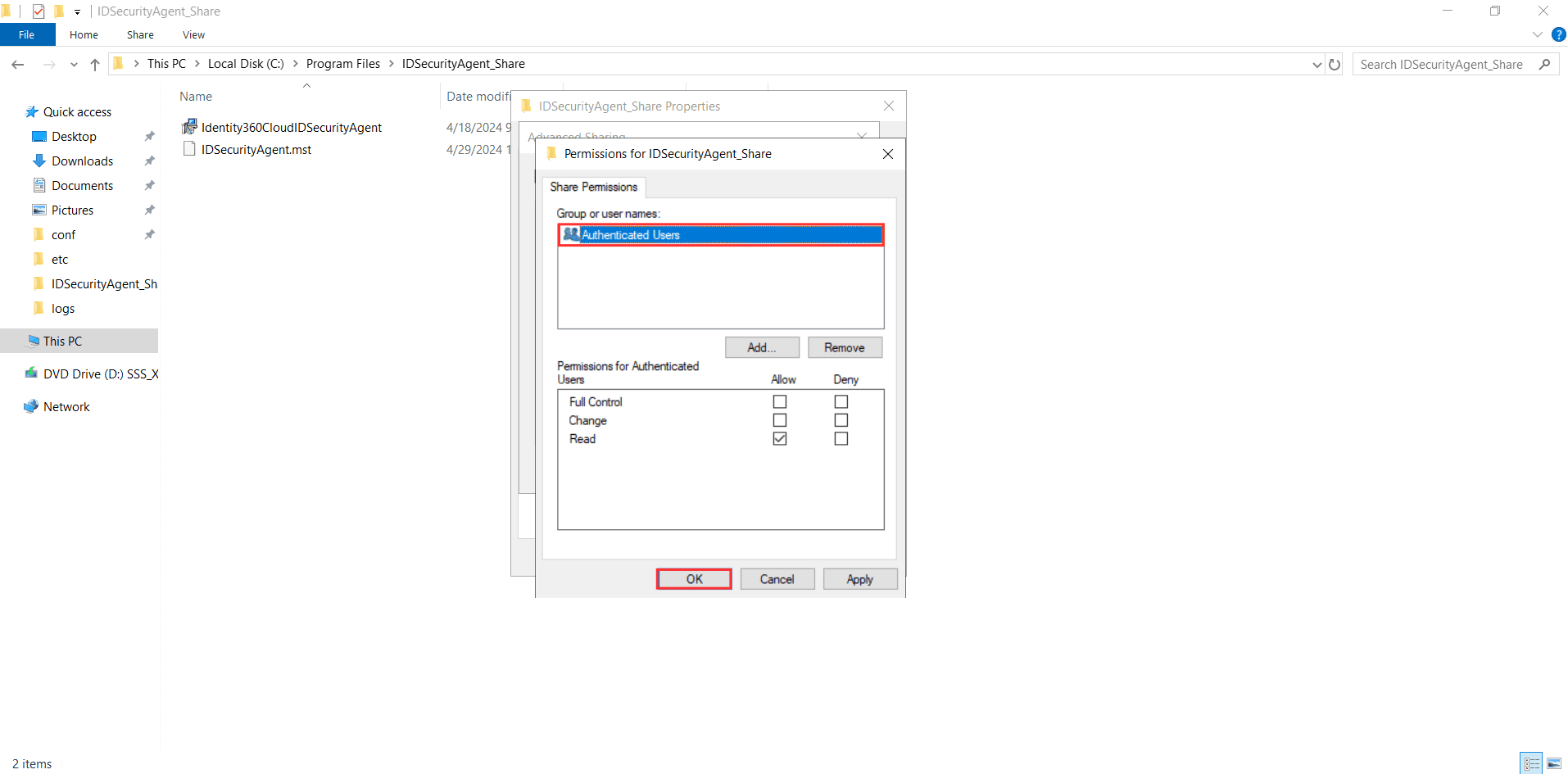
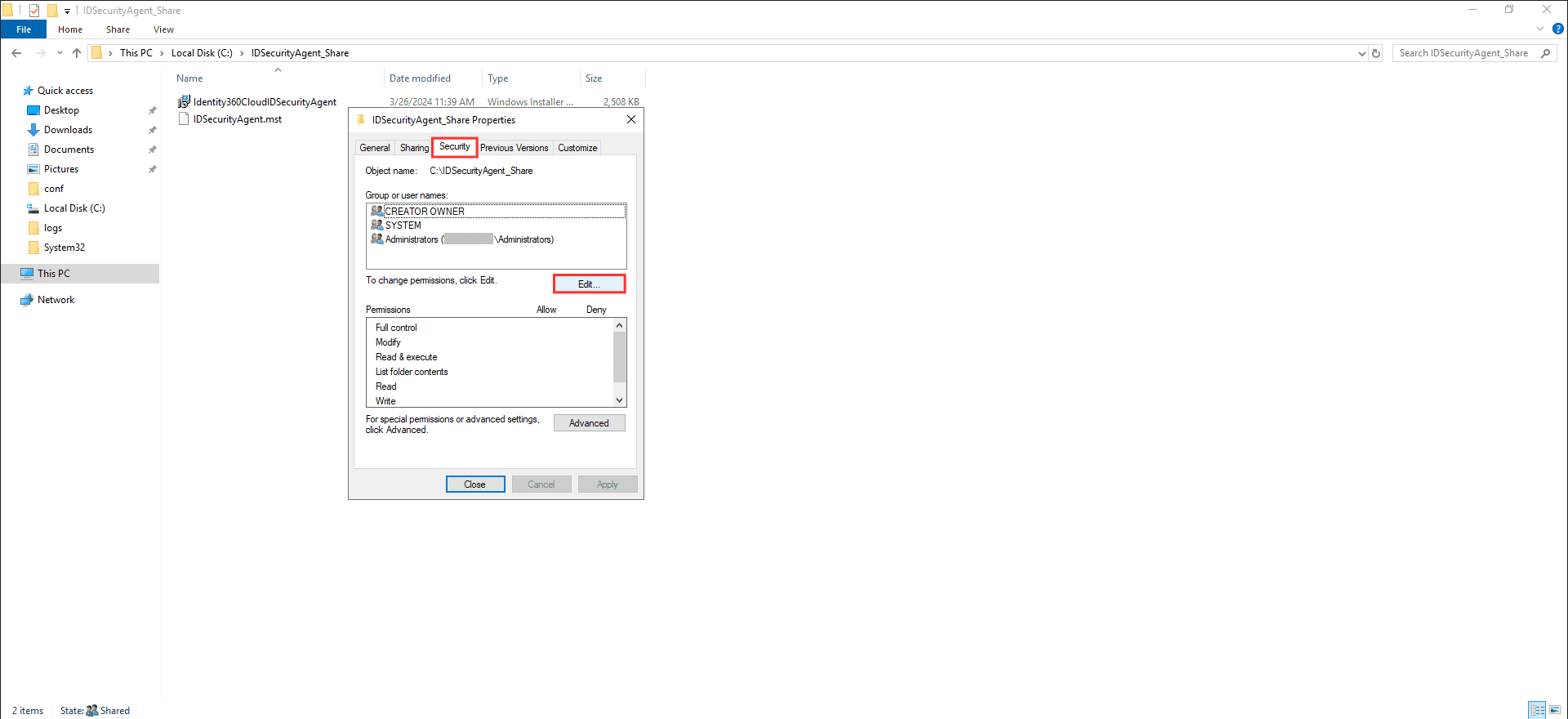
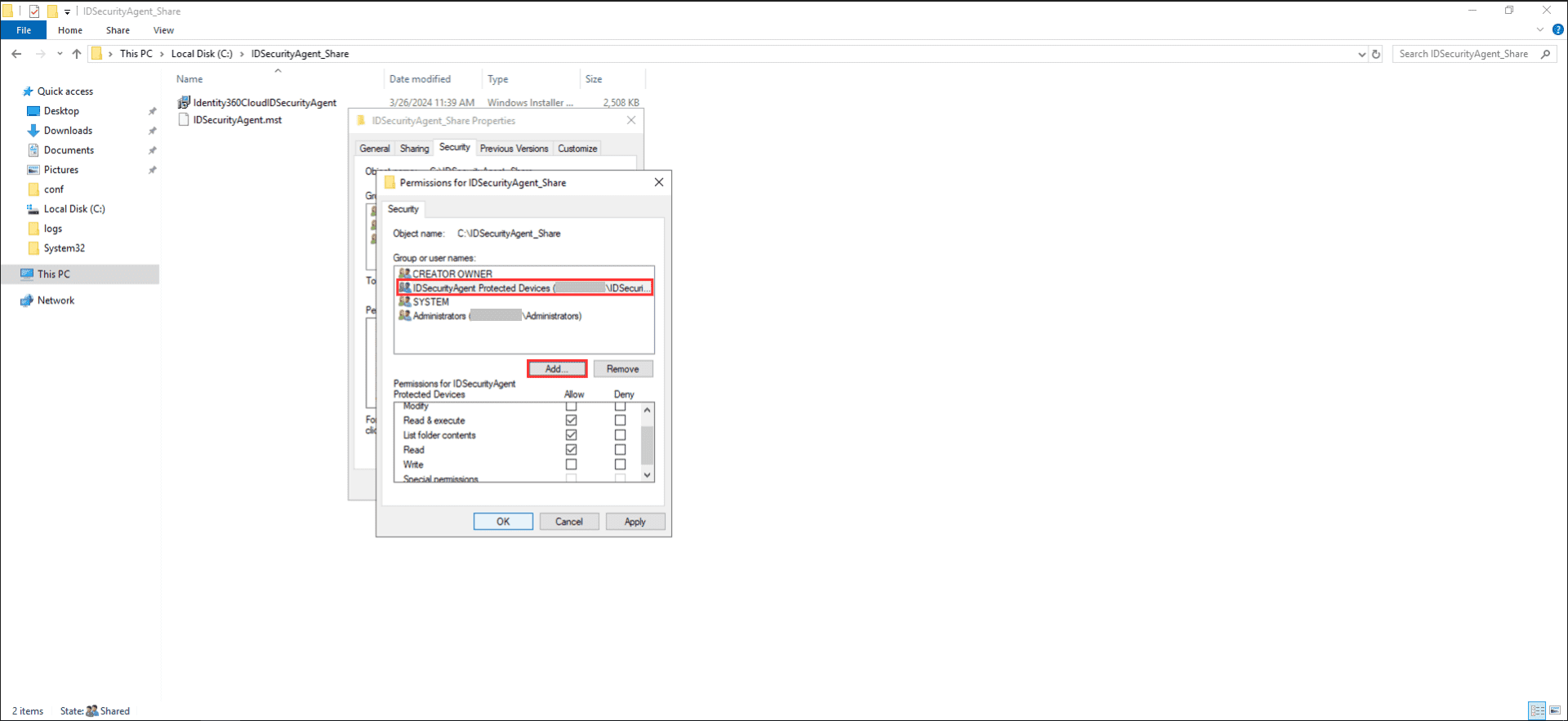
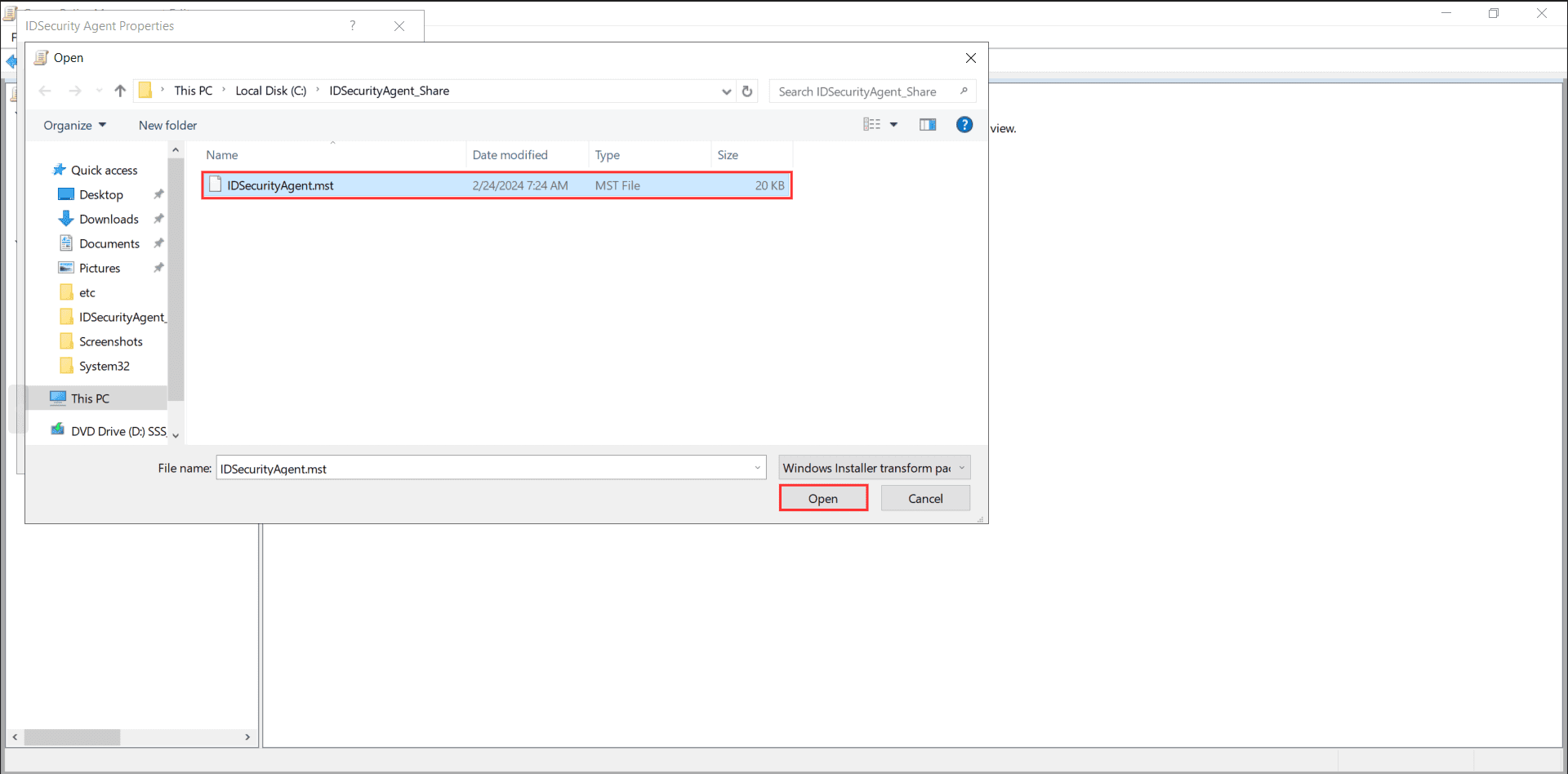
Important note: Ensure that no unauthorized user accounts have access to the network-shared folder, and transform file (MST). Refer to the steps mentioned below to provide appropriate access permissions.
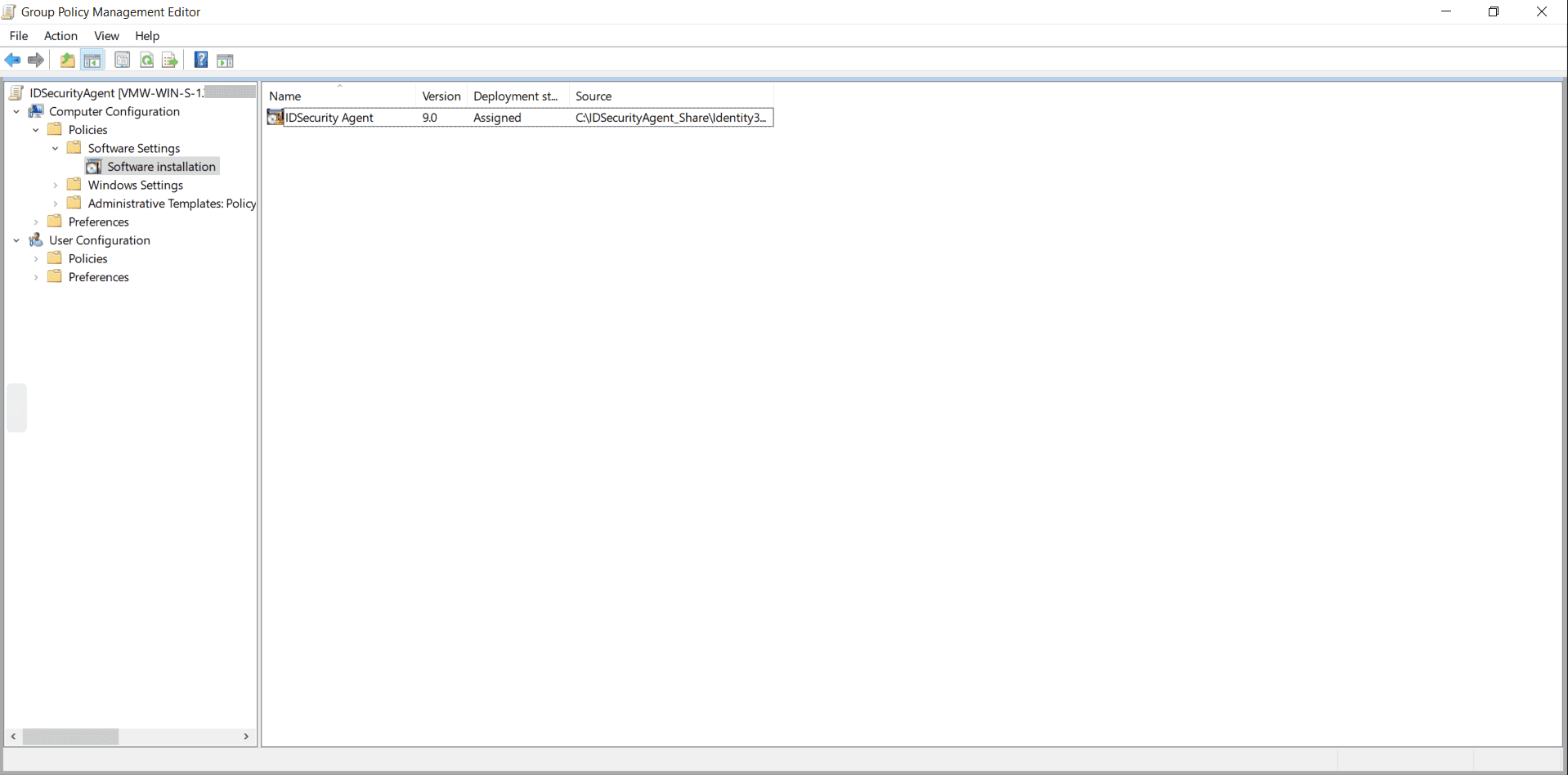
Verify whether all the computers in the custom computer group have the software installed. The software installation will take effect only after rebooting the client machines. To test whether the installation was successful:
The customizations.json file is used to customize the IDSecurity Agent's default parameters. Before proceeding with the installation, ensure you prepare a customizations.json file similar to the provided sample below. This file should contain the necessary parameters that require modification. Place this file in the same network path created in Step 2: Create a network share.
Note: If customization is not required, the MSI will automatically utilize the default parameters.
If you have not customized the file as mentioned in the previous step, you can still make adjustments later by editing the file located at C:\Program Files\ManageEngine\Identity360 Cloud IDSecurity Agent\conf\customizations.json
Note: Please refrain from making any modifications to any files aside from customizations.json found in the installation folder, as these files are integral to the functioning of the IDSecurity Agent. Any changes to these files may disrupt functionality of both the agent and the system.
{
"LogPath": "C:\\Program Files\\ManageEngine\\Identity360 Cloud IDSecurity Agent\\logs",
"LogLevel": "NORMAL",
"LogRotationMaxSize": "50",
"LogArchivePath": "C:\\Program Files\\ManageEngine\\Identity360 Cloud IDSecurity Agent\\logs\\archive",
"Title": "IDSecurity Agent",
"WebclientFaviconPath": "C:\\Program Files\\ManageEngine\\Identity360 Cloud IDSecurity Agent\\resources\\favicon.ico"
}
The table below contains the list of default values and descriptions for all parameters.
| Parameter Name | Default Value | Description |
|---|---|---|
| LogPath | C:\Program Files\ManageEngine\Identity360 Cloud IDSecurity Agent\logs |
The log file is stored here. Caution: Modifying the value is advised only if there is a valid reason to do so. If the value is altered, ensure that the folder permissions include write permissions for the Users group and the SYSTEM account. |
| LogLevel | NORMAL | The default value is set to NORMAL, providing comprehensive information essential for regular operation. If the value is changed to DEBUG, the log will incorporate detailed troubleshooting information crucial for the support team. Exercise caution, as setting the value to DEBUG will generate extra log entries, potentially causing a rapid increase in the log file's size. |
| LogRotationMaxSize | 50 | This parameter determines the maximum size of the log file. Upon reaching the specified limit, with a minimum of 10MB and a maximum of 50MB, a new log file is generated, and the previous log file is archived to the path specified in LogArchivePath. |
| LogArchivePath | C:\Program Files\ManageEngine\Identity360 Cloud IDSecurity Agent\logs\archive | This refers to the file path where log files are archived once they reach the specified LogRotationMaxSize limit. |
| Title | IDSecurity Agent | Title of the MFA prompt. |
| WebclientFaviconPath | C:\Program Files\ManageEngine\Identity360 Cloud IDSecurity Agent\resources\favicon.ico | Icon of the MFA prompt. |
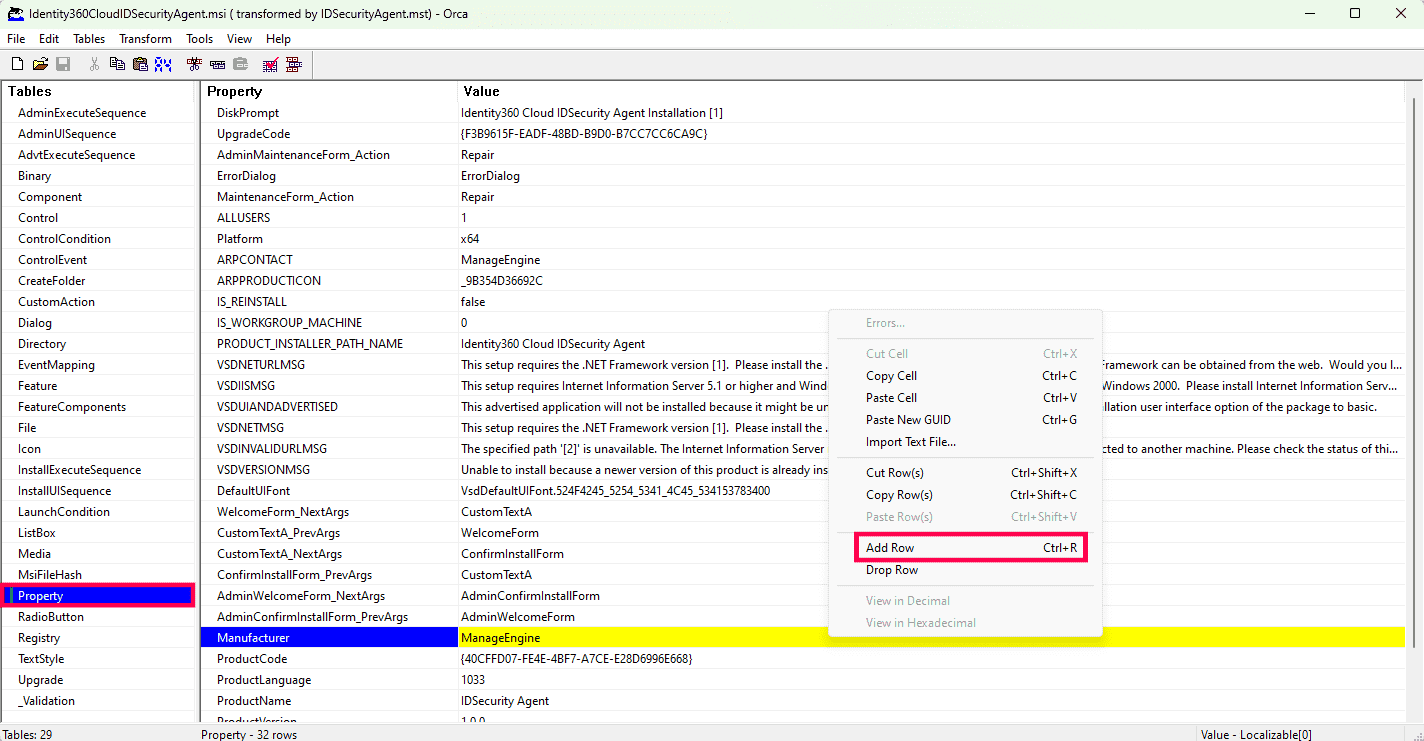
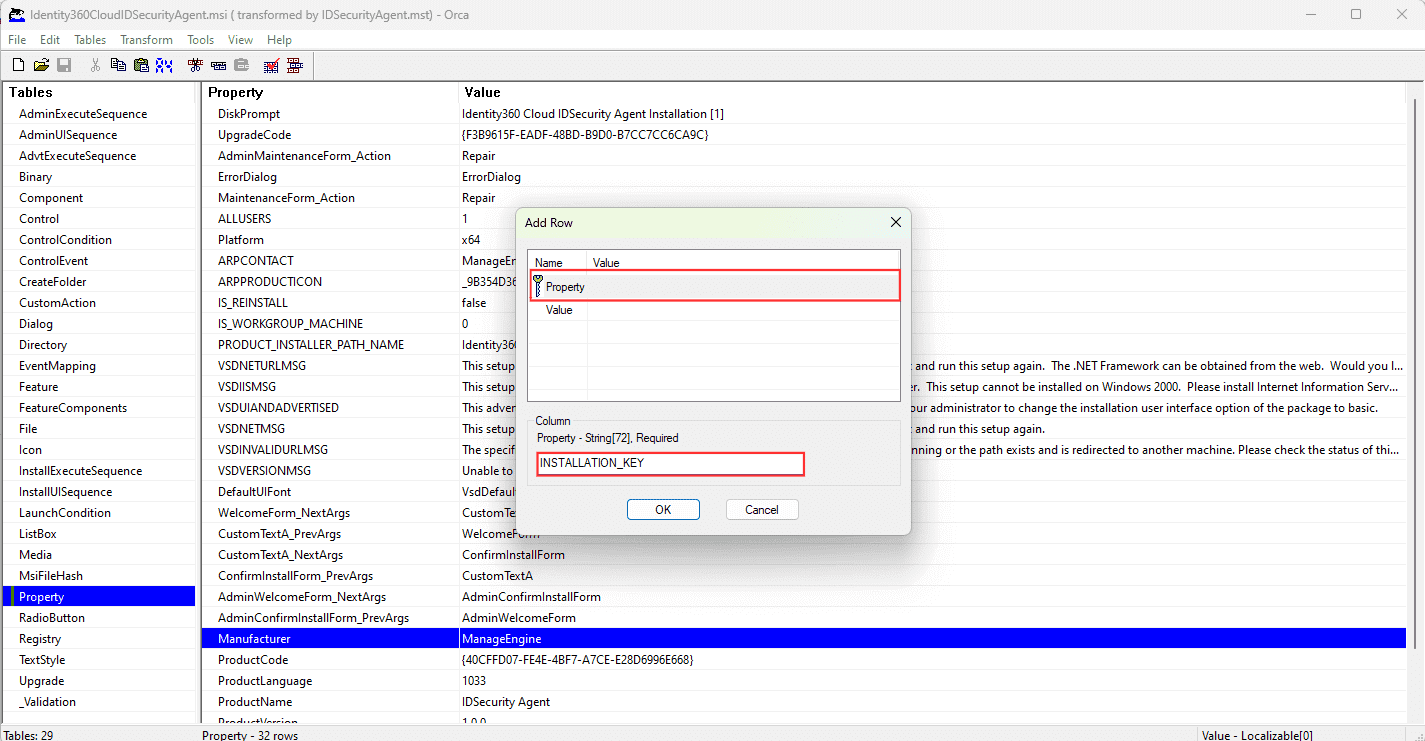
In case the current installation of the IDSecurity Agent is compromised, regenerate a new Installation Key from the Identity360 admin portal by navigating to Applications > Multi-factor Authentication > Install IDSecurity Agent > Step 2 > Regenerate. Copy the command along with the newly generated key and follow these steps to update the Installation Key.
Copyright © 2025, ZOHO Corp. All Rights Reserved.