- Free Edition
- What's New?
- Quick Links
- Log Management
- Application Log Management
- Application log monitoring
- IIS log analyzer
- IIS web log analyzer
- IIS FTP log analyzer
- IIS log parser
- VMware log analyzer
- Hyper V event log auditing
- SQL database auditing
- SQL server auditing
- MySQL log analyzer
- Apache log analyzer
- DHCP server auditing
- Database activity monitoring
- Database auditing
- Oracle database auditing More..
- IT Compliance Auditing
- IT Compliance Auditing
- SOX Compliance Audit
- GDPR Compliance Audit
- ISO 27001 Compliance Audit
- HIPAA Compliance Audit
- PCI Compliance Audit
- FISMA Compliance Audit
- GLBA Compliance Audit
- GPG Compliance Audit
- ISLP Compliance Audit
- FERPA Compliance Audit
- CCPA Compliance Reports
- CCPA Compliance Software
- NERC Compliance Audit Reports
- Cyber Essentials Compliance Reports
- Reports for New Regulatory Compliance
- Customizing Compliance Reports
- PDPA compliance audit reports
- CMMC Compliance Audit More..
- SIEM
- Security Information and Event Management (SIEM)
- Threat Intelligence
- STIX/TAXII feed processor
- Server Log Management
- Event Log Monitoring
- File Integrity Monitoring
- Linux File Integrity Monitoring
- Threat Whitelisting
- Advanced Threat Analytics
- Security Log Management
- Log Forensics
- Incident Management System
- Application log management
- Real-Time Event Correlation
- Detecting Threats in Windows
- External Threat Mitigation
- Malwarebytes Threat Reports
- FireEye Threat Intelligence
- Linux Log Analyzer More..
- Network Device Monitoring
- Network Device Monitoring
- Router Log Auditing
- Cisco Logs Analyzer
- VPN log analyzer
- IDS/IPS log monitoring
- Solaris Device Auditing
- Monitoring user activity in routers
- Monitoring Router Traffic
- Switch Log Monitoring
- Arista Switch Log Monitoring
- Firewall Log Analyzer
- Firewall Traffic Monitoring
- Windows Firewall Auditing
- SonicWall Log Analyzer
- H3C Firewall Auditing
- Barracuda Device Auditing
- Palo Alto Networks Firewall Auditing
- Juniper Device Auditing
- Fortinet Device Auditing
- pfSense Firewall Log Analyzer
- NetScreen Log Analysis
- WatchGuard Traffic Monitoring
- Check Point Device Auditing
- Sophos Log Monitoring
- Huawei Device Monitoring
- HP Log Analysis
- F5 Logs Monitoring
- Fortinet log analyzer More..
- Endpoint Log Management
- System and User Monitoring Reports
- More Features
- Resources
- Product Info
- Related Products
- Log360 (On-Premise | Cloud) Comprehensive SIEM and UEBA
- ADManager Plus Active Directory Management & Reporting
- ADAudit Plus Real-time Active Directory Auditing and UBA
- ADSelfService Plus Identity security with MFA, SSO, and SSPR
- DataSecurity Plus File server auditing & data discovery
- Exchange Reporter Plus Exchange Server Auditing & Reporting
- M365 Manager Plus Microsoft 365 Management & Reporting Tool
- RecoveryManager Plus Enterprise backup and recovery tool
- SharePoint Manager Plus SharePoint Reporting and Auditing
- AD360 Integrated Identity & Access Management
- AD Free Tools Active Directory FREE Tools
Public-facing systems, such as web servers, are often targeted by attackers. If these business critical resources are not secured properly, it might lead to security attacks that result in huge financial ramifications and loss of a favorable reputation among customers.
ManageEngine EventLog Analyzer, a comprehensive log management software, helps collect, audit, correlate, and search web server logs to detect anomalies. The solution helps uncover potential vulnerabilities and ensures overall web server security.
Here's how EventLog Analyzer helps you secure your web server
Monitor web server log
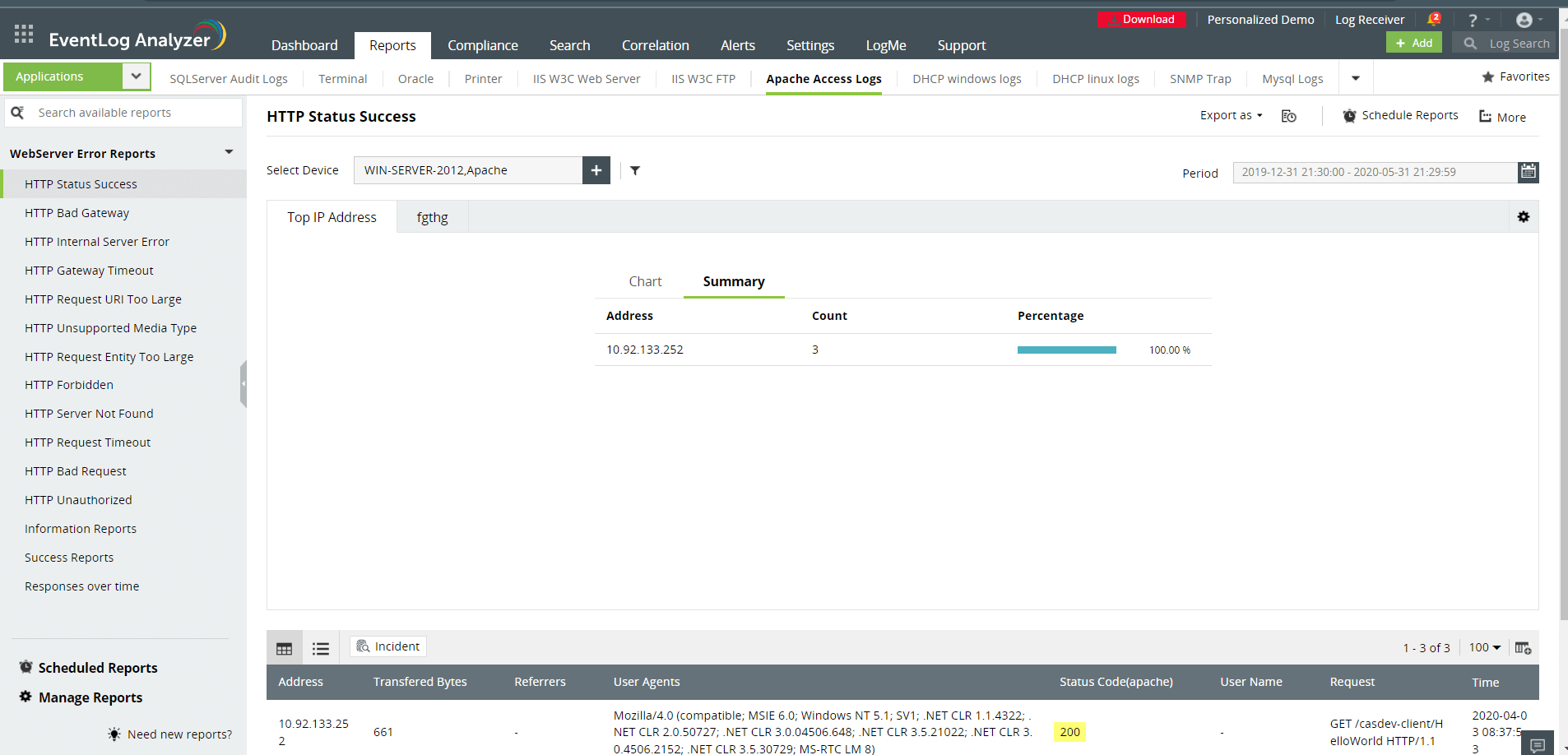
Auditing web server logs helps you receive detailed information for every webpage requested, including date, time, and type of browser used. EventLog Analyzer's web server monitoring capability helps you identify insider threats, account compromise, and data exfiltration attempts. It helps ensure the confidentiality and integrity of your web server. The solution also provides actionable key insights and intuitive reports of anomalous user activities.
Auditing web server errors and usage
Auditing web server helps identify configuration errors, and performance issues for the end users. Also, EventLog Analyzer ensures web servers like Microsoft's Internet Information Services (IIS), Apache, and Nginx are up and running smoothly without causing any downtime. EventLog Analyzer provides detailed predefined reports on web server errors, such as HTTP 502 bad gateway, HTTP forbidden, HTTP unauthorized and more, to help you quickly troubleshoot the issues.
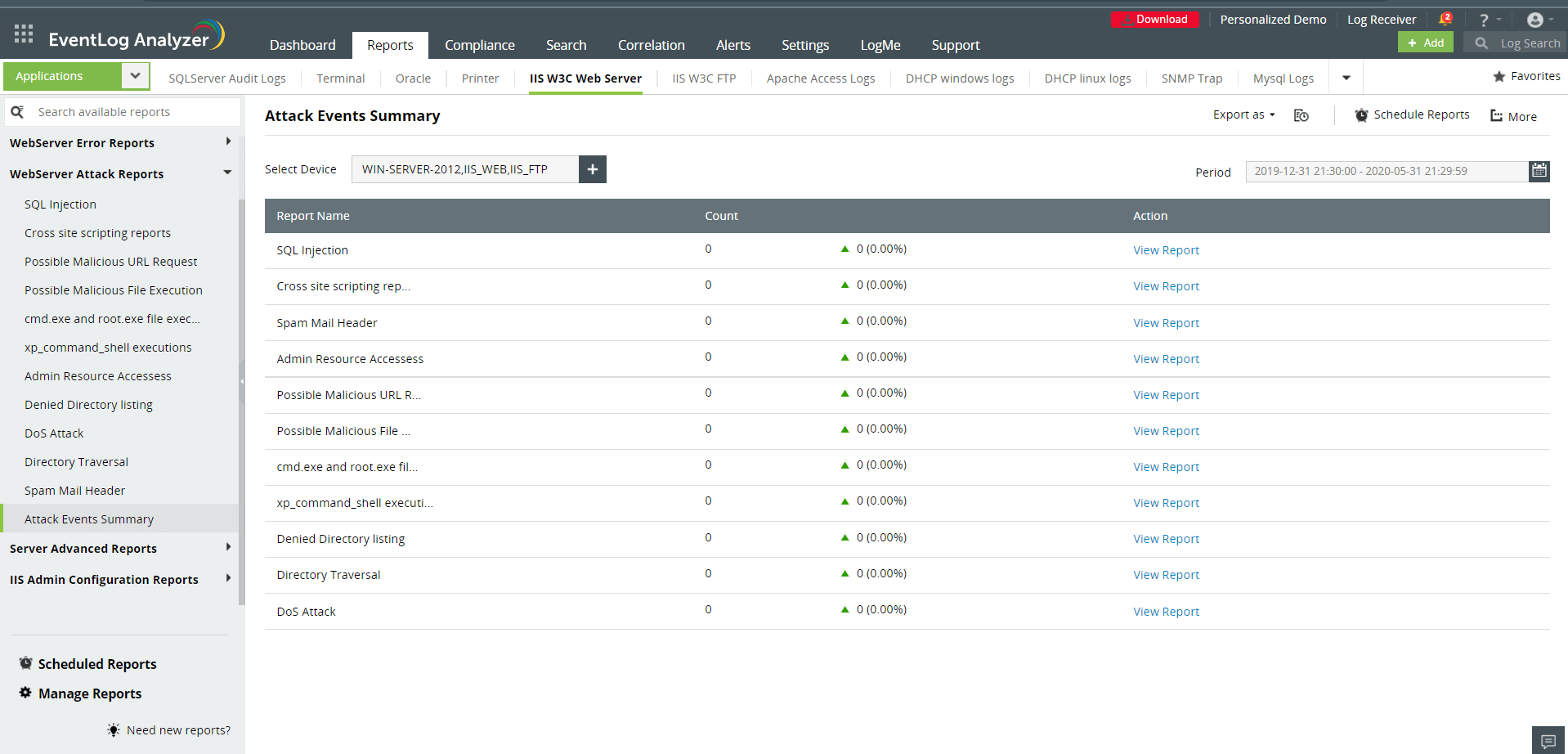
Detect web server security threats
EventLog Analyzer, a comprehensive log management software helps detect and prevent CSS-based sniffing attacks, cache-based attacks, DNS-based attacks, and protocol vulnerabilities like URL parsing, and ensures the security of your web server. The solution's advanced threat analytics helps you detect and immediately stop traffic from malicious sources. In addition, the solution enables you to customize the list of admissible entities or sources, and whitelist IP addresses, URLs, and domains.
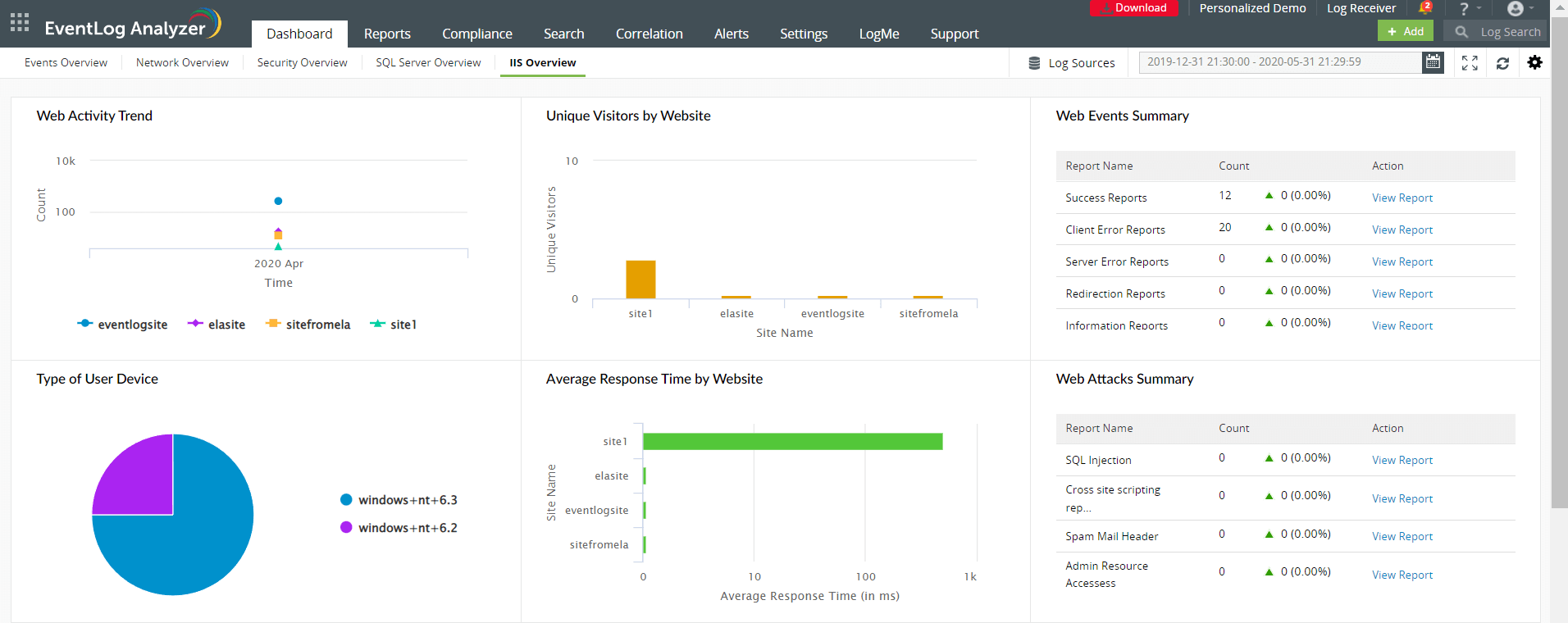
Visualize web server security events using analytics
EventLog Analyzer's security analytics dashboard helps you visualize and receive actionable insights from your web server activities. This web server security solution provides trend graphs on web server activity that helps you to spot any anomalies. Additionally, the solution gives information on unique visitors to your websites and traffic distribution. It also facilitates quicker analysis to spot denial of services attacks. Further, it helps you reduce the average response time of your web server and optimize the web server performance.
The solution presents a summary of all web events, FTP events, and web attacks in a single console to help you achieve end-to-end web server security visibility. Furthermore, you can use the advanced search option to search for more specific logs to spot the malicious source accurately.
Trace web server attacks using forensic investigation
EventLog Analyzer's powerful log search engine helps drill down into web server logs to quickly pinpoint the suspicious log entry, exact time, location, and who initiated that security event to help you backtrack the incidents. The solution helps perform log forensic analysis to track unauthorized access and traffic stats in the event of a data breach. Get notified about real-time web server access and modifications.
Other solutions offered by EventLog Analyzer
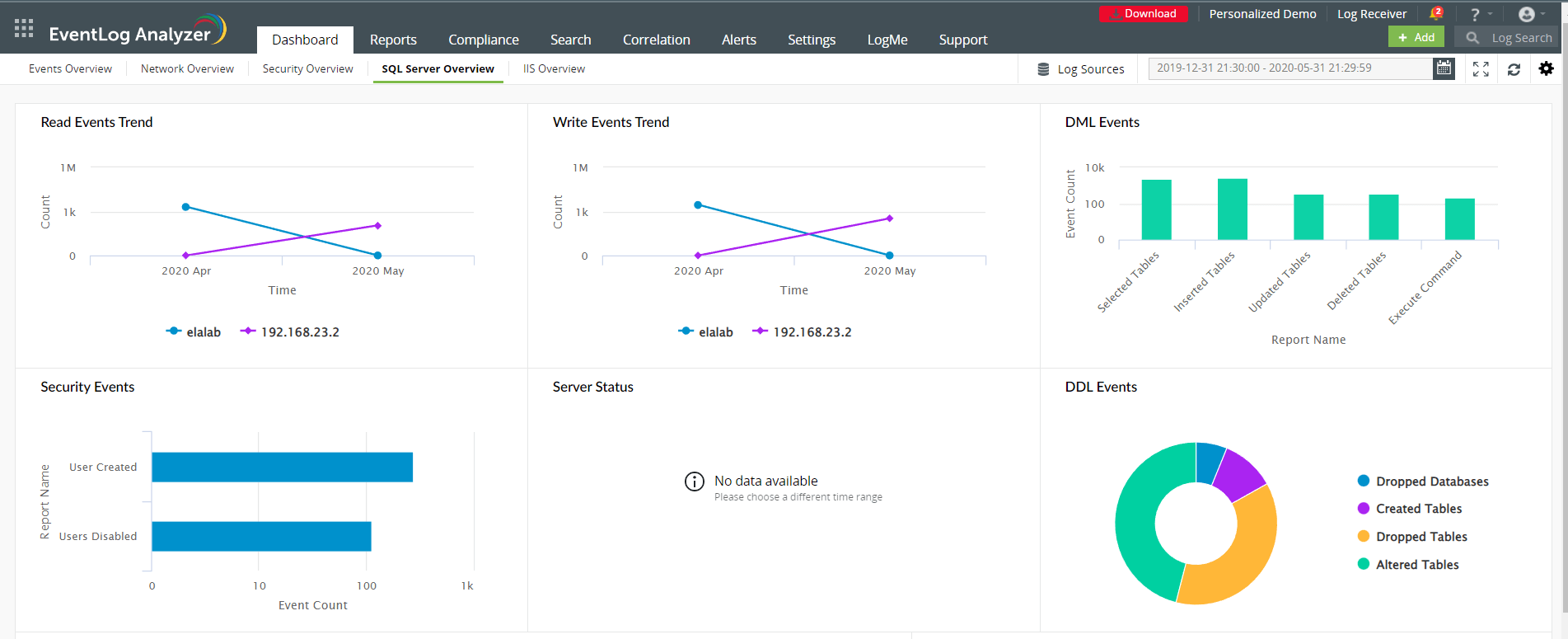
Database auditing
EventLog Analyzer has predefined reports for MS SQL server, Oracle database server, and sends real-time alerts to help track Data Definition Language, Data Manipulation Language activity changes, server activity changes, account changes, and security attacks.
Network device monitoring
Monitor network perimeter devices like firewalls, IDS/IPS, routers, and switches with EventLog Analyzer's in-depth reports and 200 predefined alert profiles to identify network device anomalies.
User session monitoring
EventLog Analyzer's real-time user audit monitoring helps monitor and analyze the session activity of a user to ascertain whether an attack has been carried out by the internal user or external attacker.
VPN monitoring
EventLog Analyzer automatically collects and monitors VPN logs to ensure only authorized users has access to your network. The solution provides out-of-the-box reports and alerts for Cisco, SonicWall, Fortinet, Huawei, Sophos, and Meraki devices.
5 reasons to choose EventLog Analyzer as your web server auditing tool
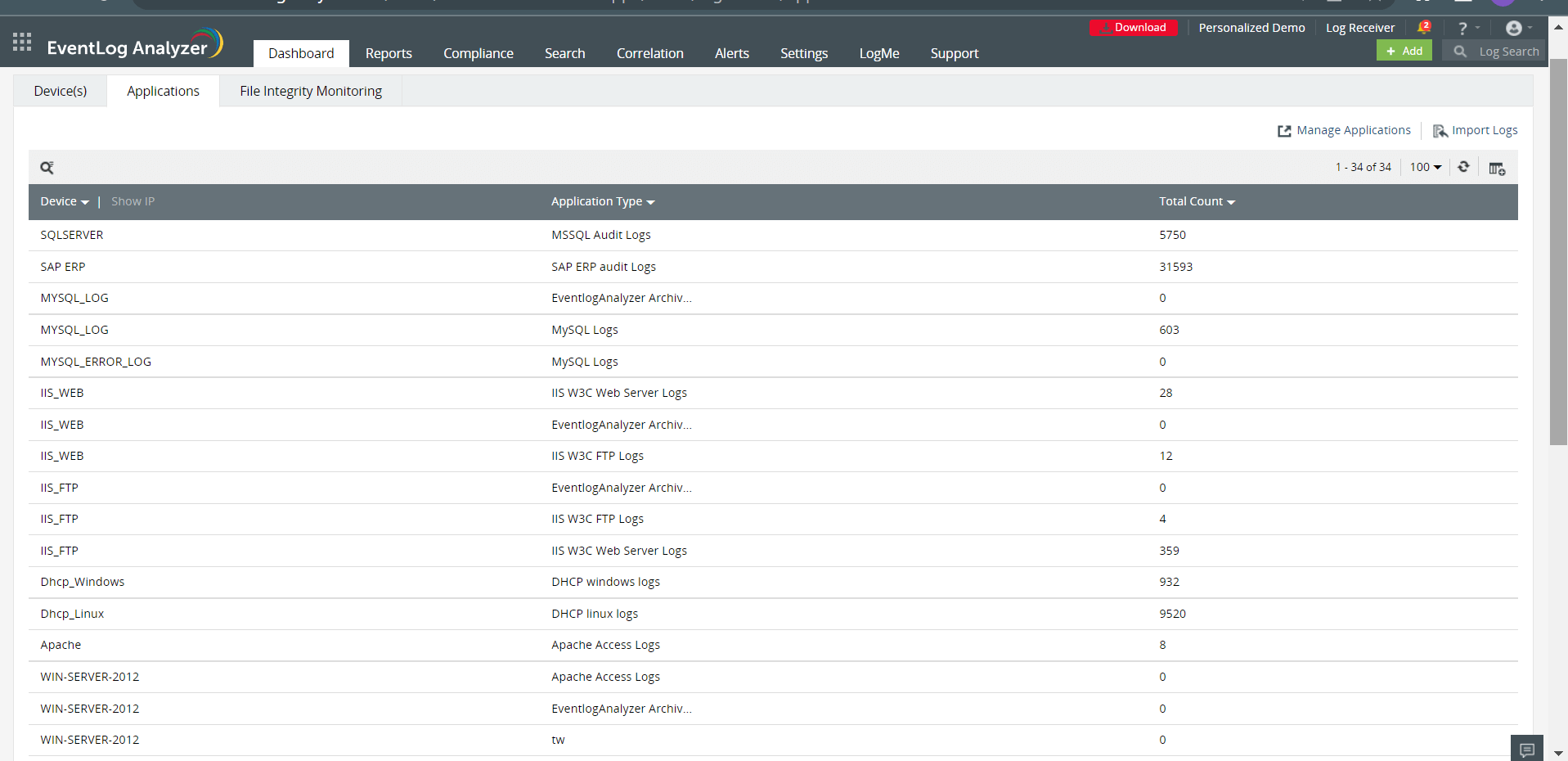
1. Application log monitoring
Audit web server applications such as IIS, Apache, Nginx, and database server applications like Microsoft SQL Server, Oracle, and DHCP.
2. Real-time event correlation
Discover attack patterns by correlating events from the firewall, routers, web servers, applications, and workstations to spot malicious traffic attacking your web server.
3. Augmented threat intelligence
EventLog Analyzer's threat intelligence solution identifies malicious IP sources, and URLs that try to access your web server and blocks them instantly.
4. Automated incident response
The solution enables you to gain deep insights into security incidents, improve investigations, achieve faster incident resolutions, and help keep the attackers at bay.
5. IT compliance mandates
EventLog Analyzer simplifies web server auditing and helps you generate audit-ready compliance reports for HIPAA, PCI DSS, the GDPR, and more.
Frequently asked questions
When someone wants to access your website, the web servers (like Apache server, IIS server, or Nginx server) connected to the internet receive the incoming web request and send the requested webpage to the end user. Web server auditing entails routinely checking the web server to see if a potential vulnerability exists or not, and to ensure that the server is working properly and is highly available for the end user.
This solution collects log data from the web server and helps spot hidden malicious threats. With EventLog Analyzer, you can easily monitor web server performance, availability, and response time, user activity, and troubleshoot performance issues faster. You'll gain complete visibility into your web server with the help of the solution's advanced event log correlation engine.
Hackers are constantly preying on your organization's network to exploit the vulnerabilities in your web server. Because web servers acts as a threshold to the Internet, they are prone to web server vulnerabilities like a DDOS attack, SQL injection, XSS (cross-site scripting), and more. To secure your web server from intruders, periodically monitor the server's health to spot issues in the web server's disk capacity, CPU load, memory usage, latency, failure, and accuracy.













