Data rules are created by following the steps explained below
Step 1
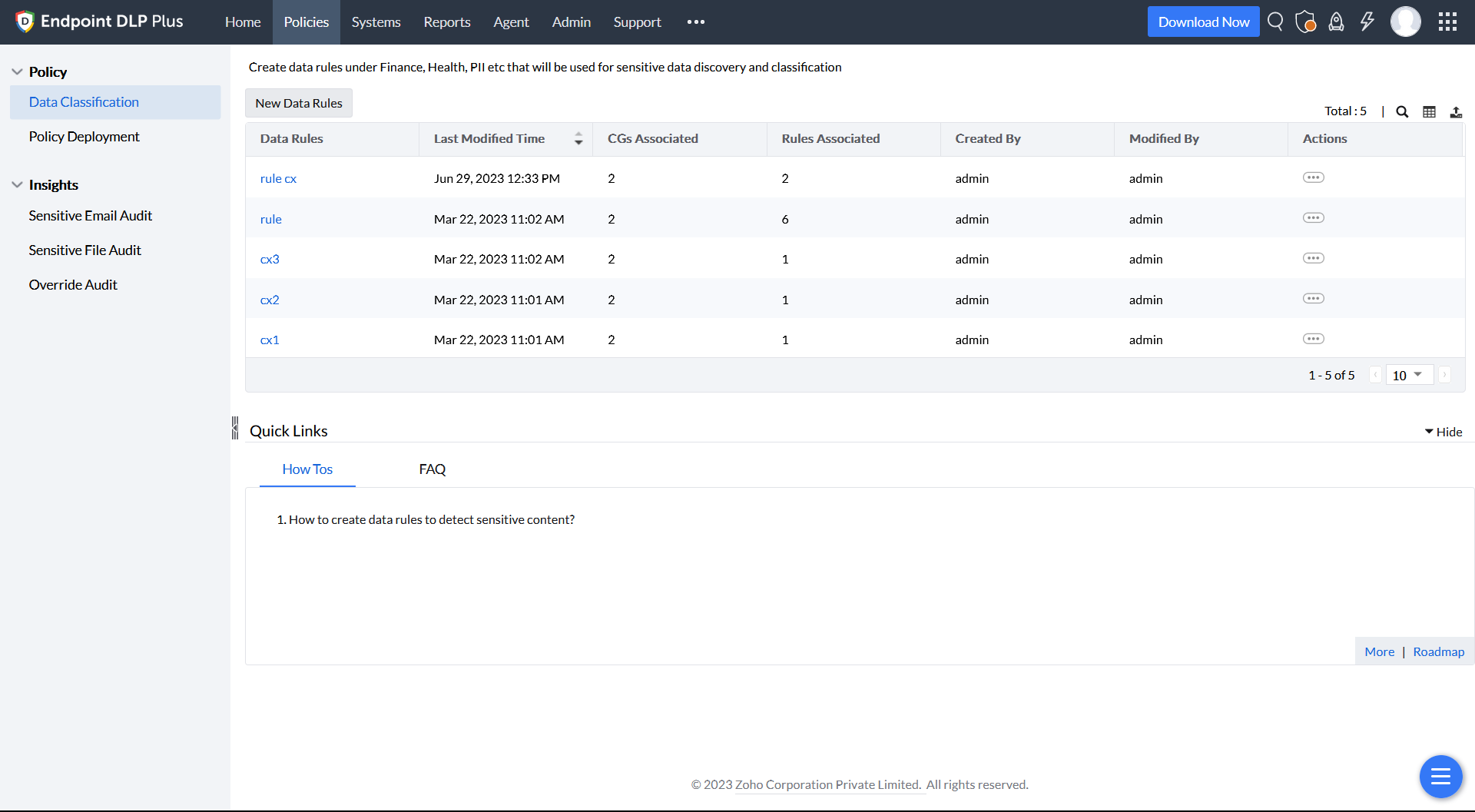
On the product console, navigate to the Data Classification section in the Policy tab and select New Data Rules.
Step 2
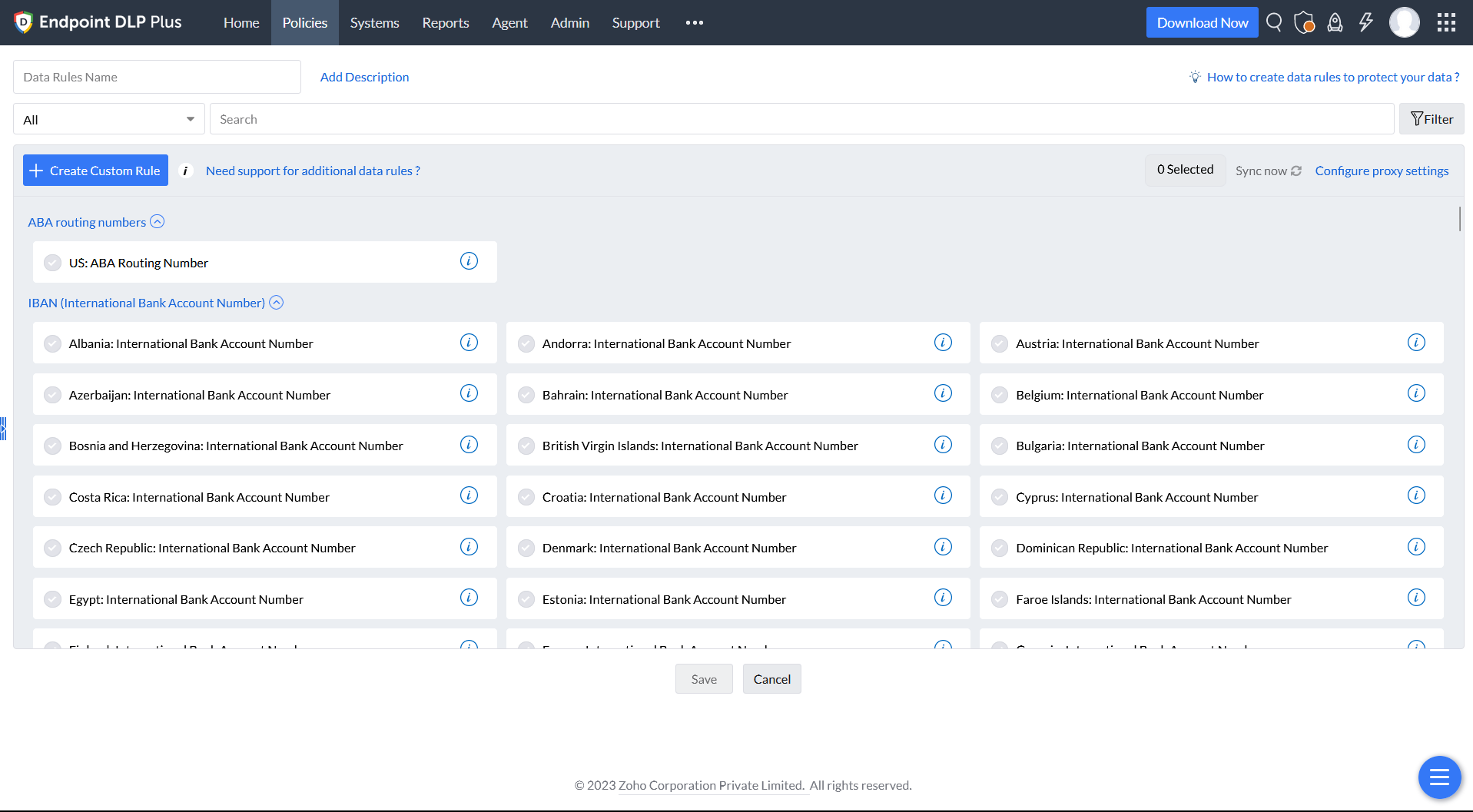
Enter a name for the Data Rule and provide a description.
Step 3
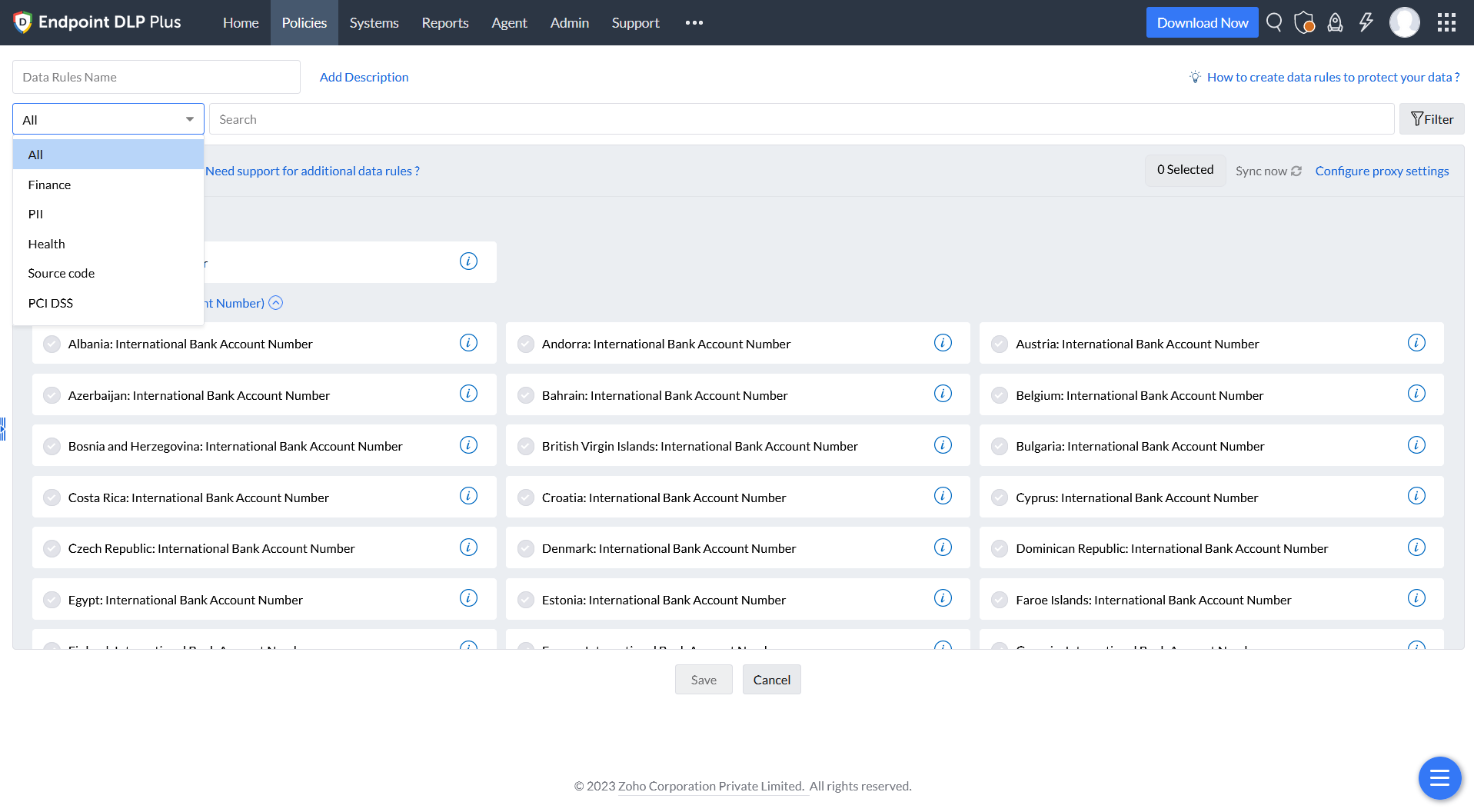
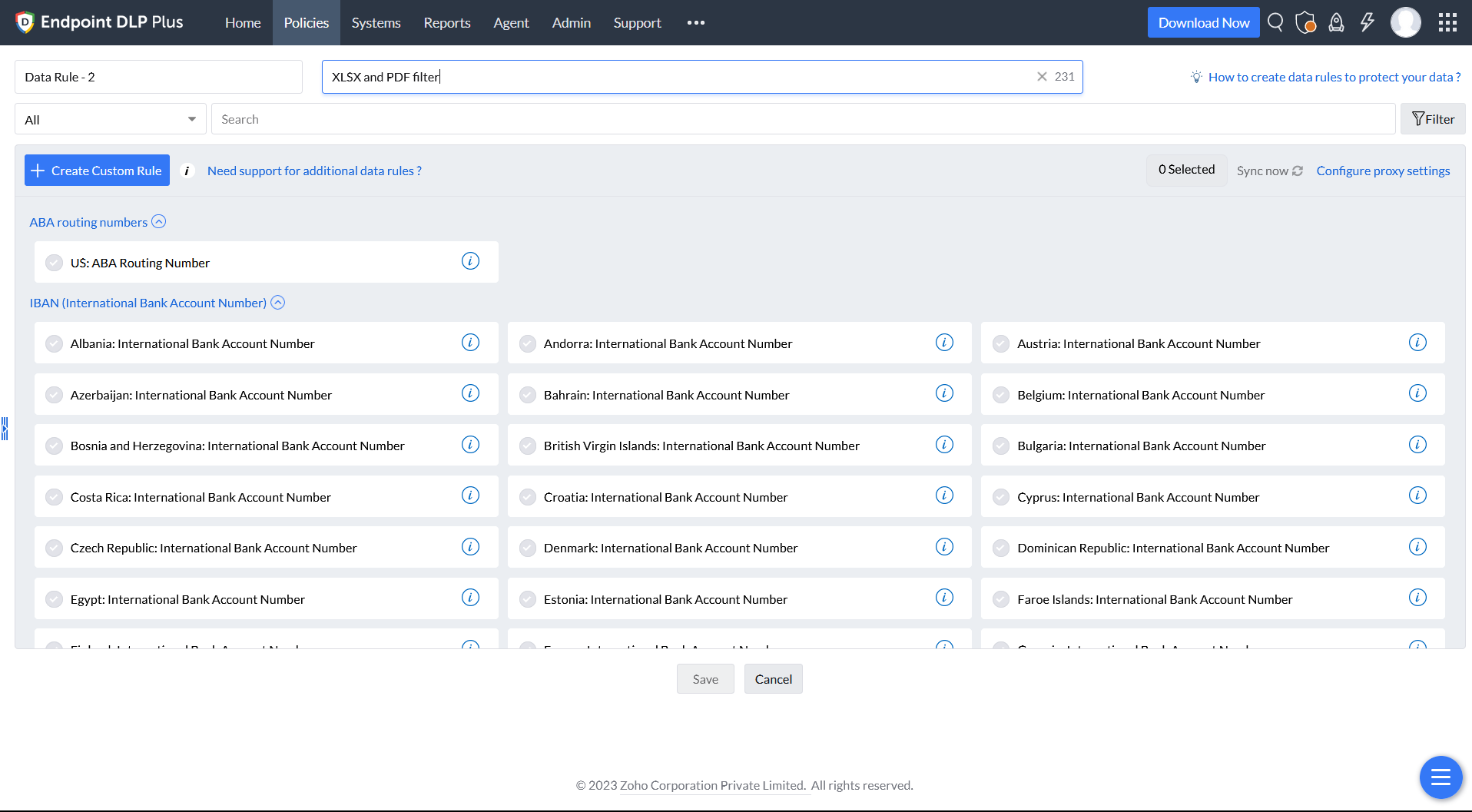
Create a Data Rule using predefined criteria The predefined criteria are listed under the field All, and can be searched in the field next to it.
Step 4
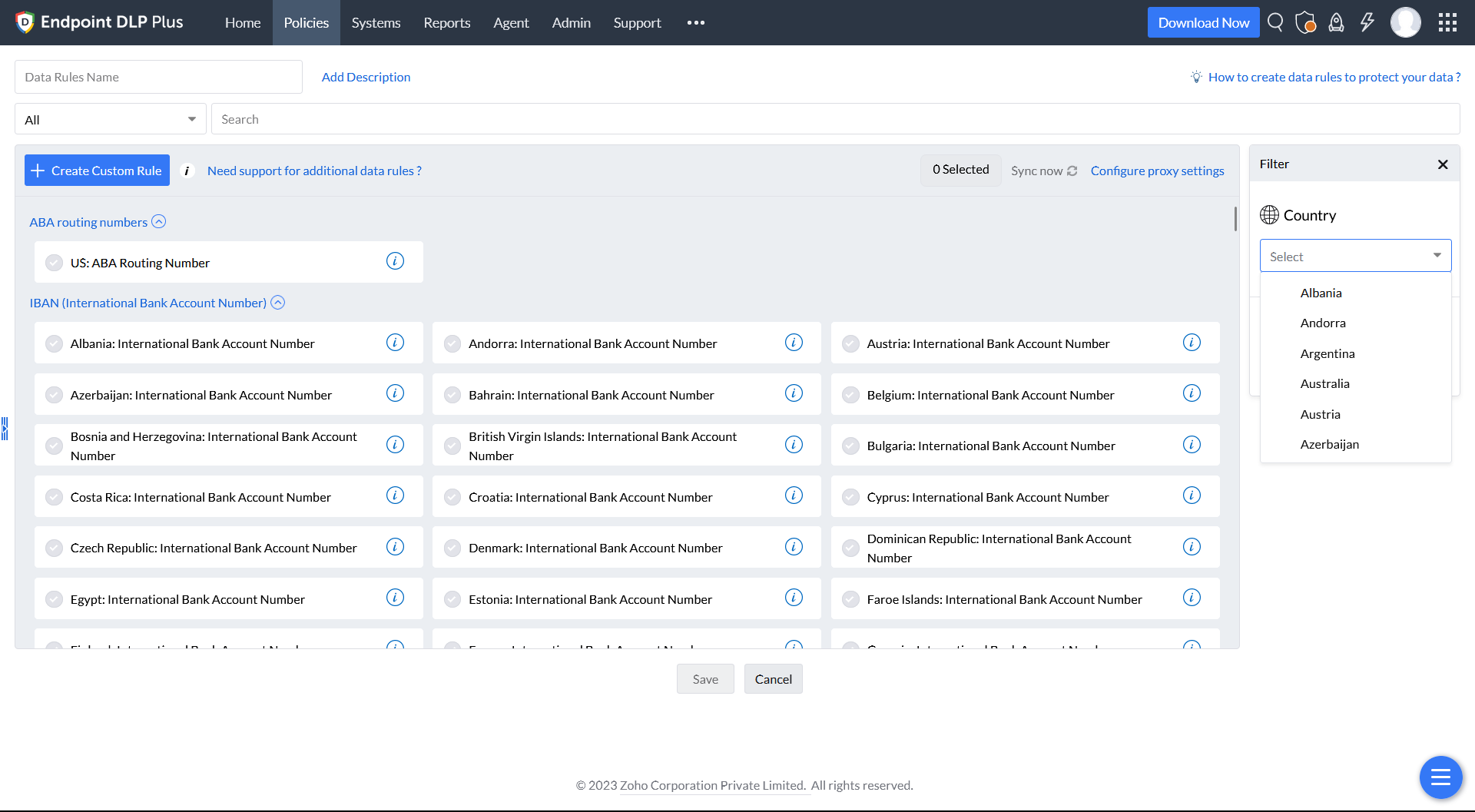
A country-wise Filter can also be selected, listing criteria that are specific only to the relevant/apposite countries for a refined search.
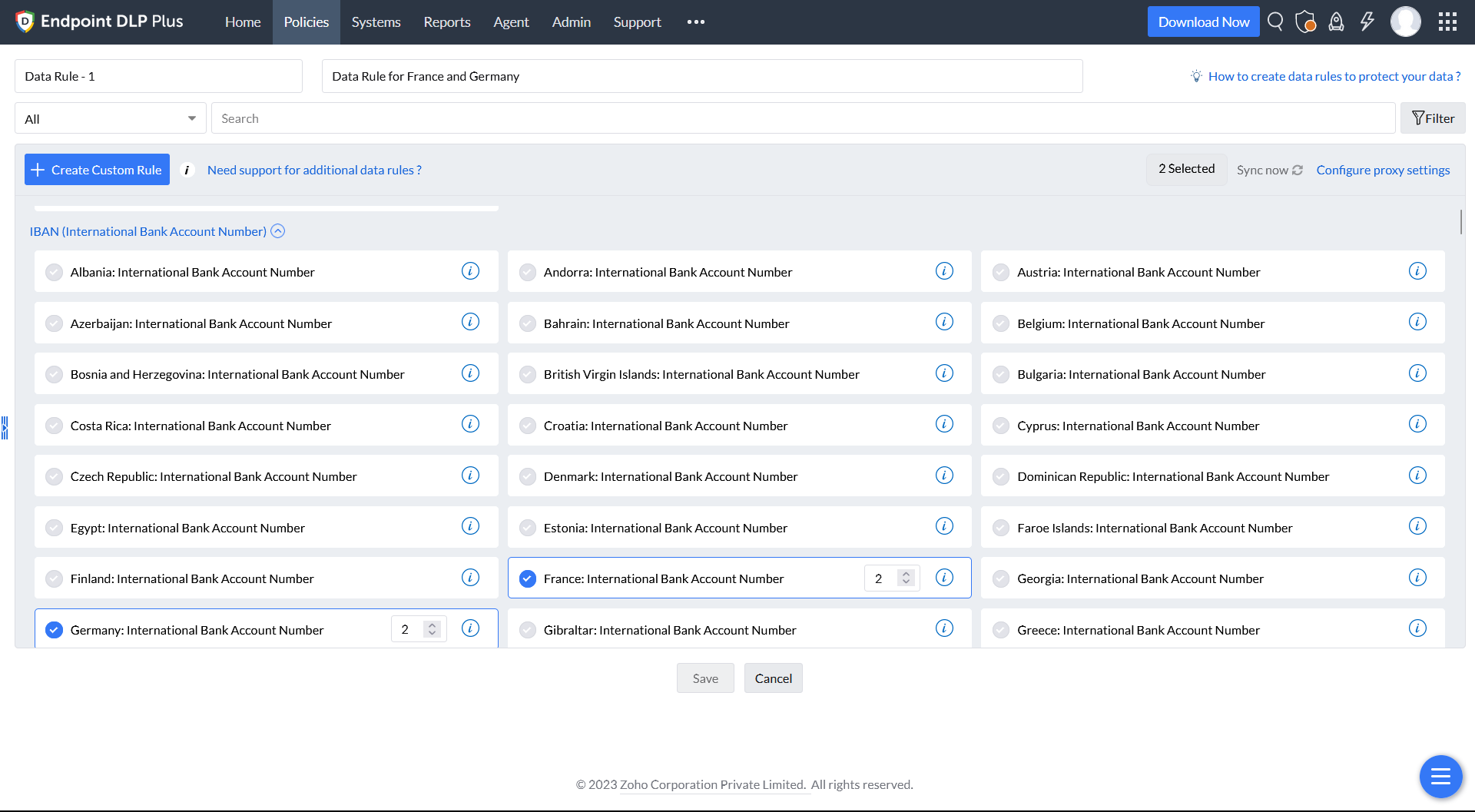
Step 5
Once appropriate criteria are selected, Save the Data Rule.
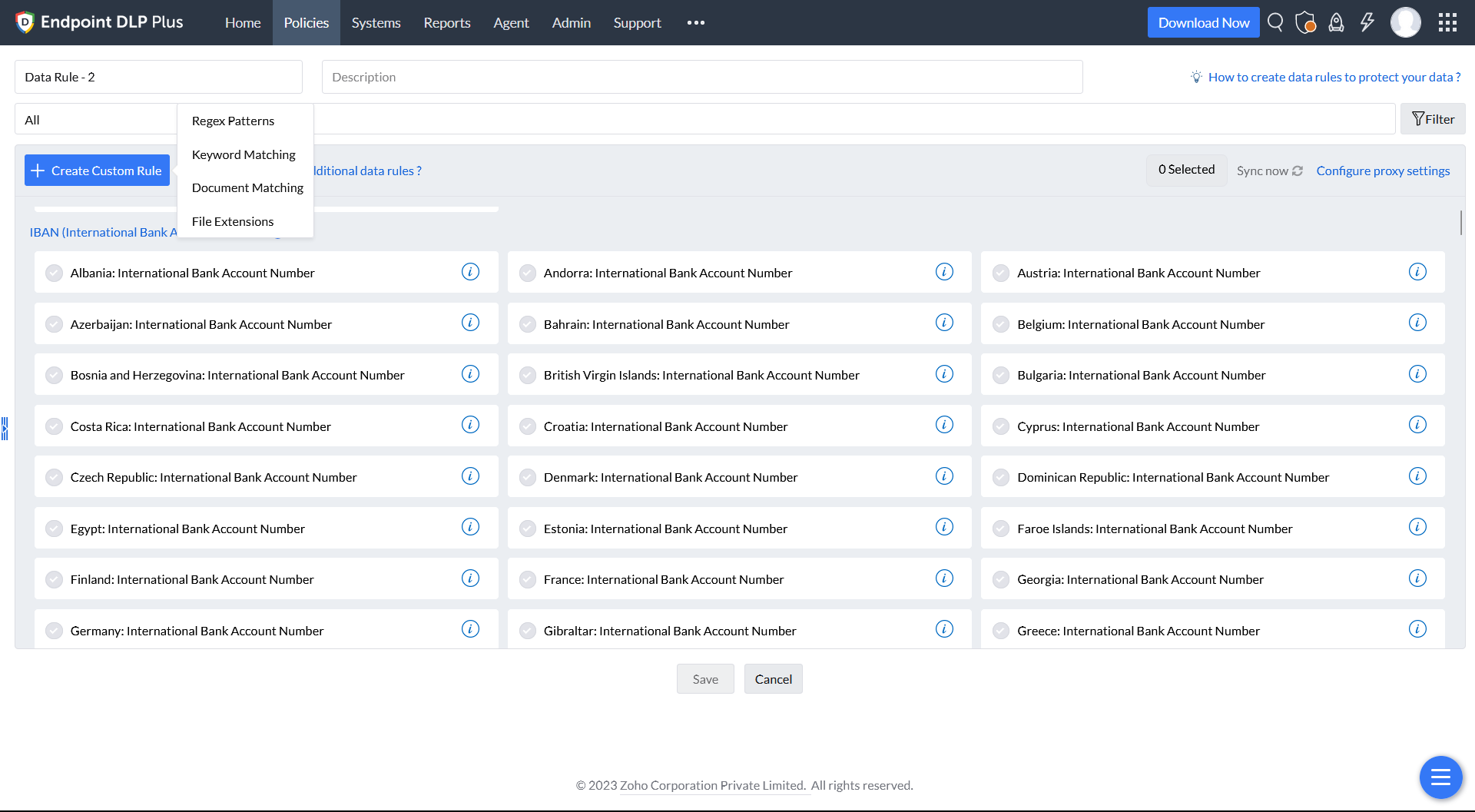
Step 6
Create a Data Rule using custom criteria Select the Create Custom Rule option and choose from Regex patterns, Keyword Matching, Document Matching, and File Extensions.
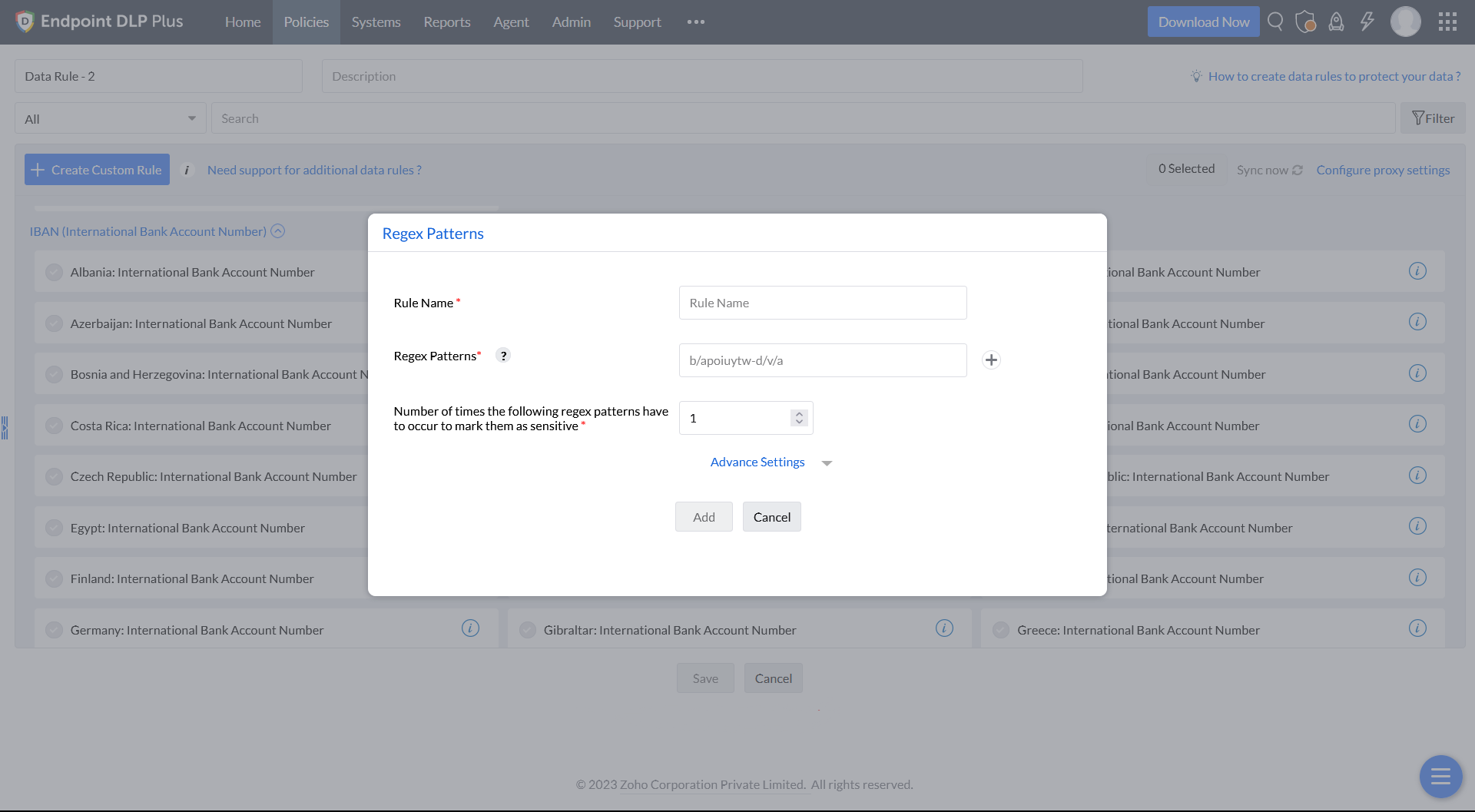
Step 7
In the Regex patterns, enter the Rule Name, Regex Patterns, and the Number of times the Regex pattern occurs.
Note: More than one Regex pattern can be included by adding the entries.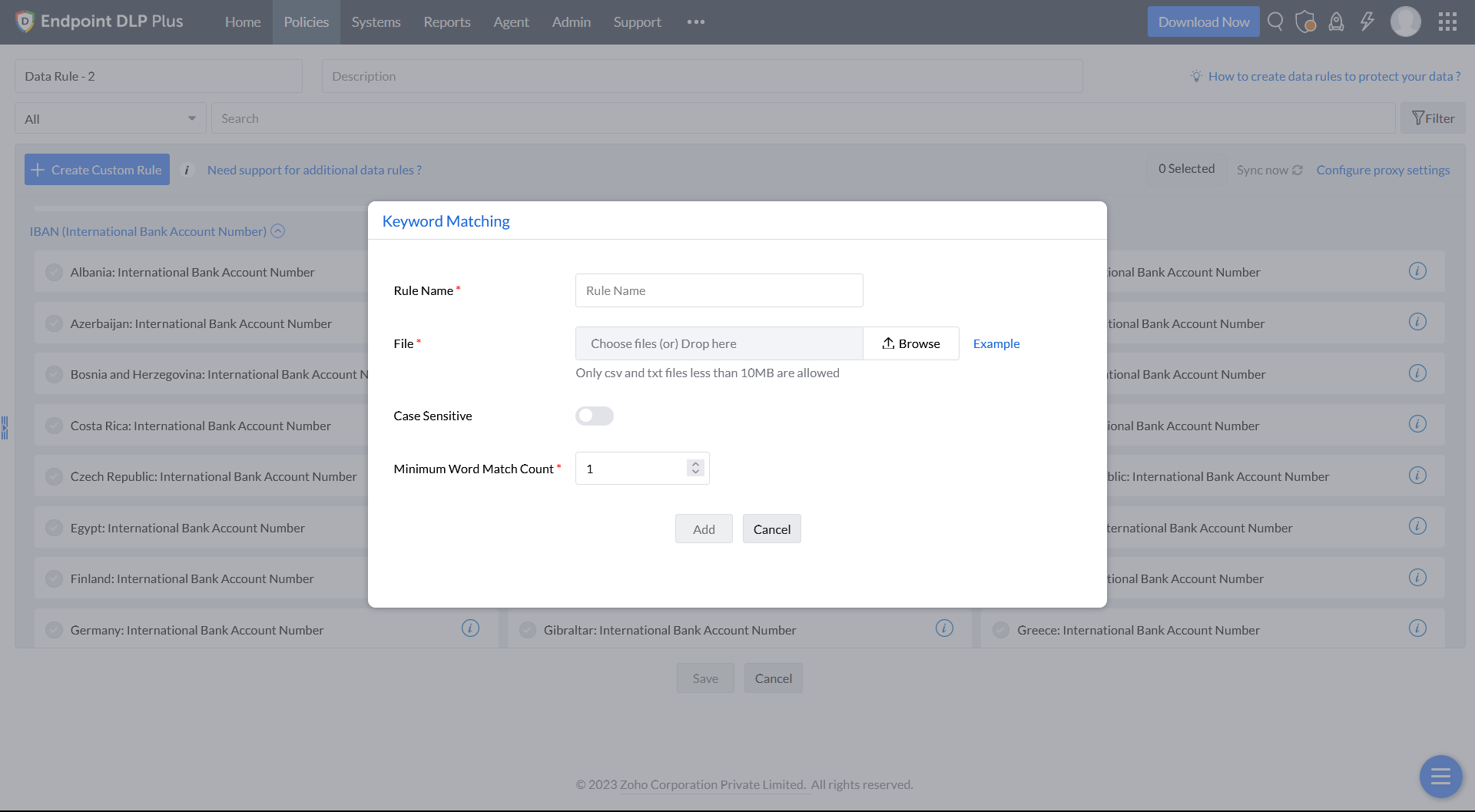
Step 8
In the Keyword Matching, enter the Rule Name, CSV/TXT file to be uploaded, and Minimum Word Match Count.
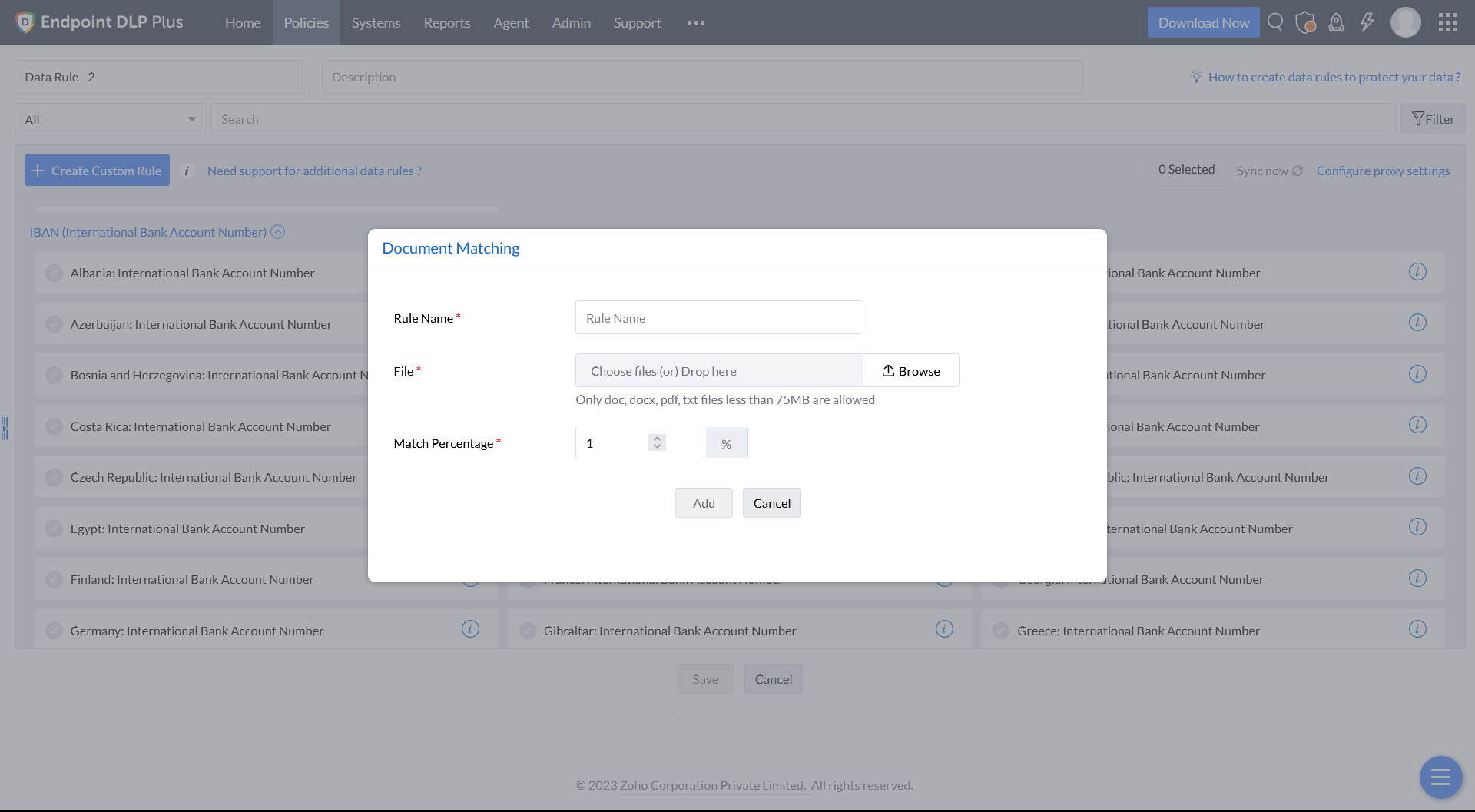
Step 9
In the Document Matching, enter the Rule Name, DOC/DOCX/PDF/TXT files to be uploaded, and Match Percentage.
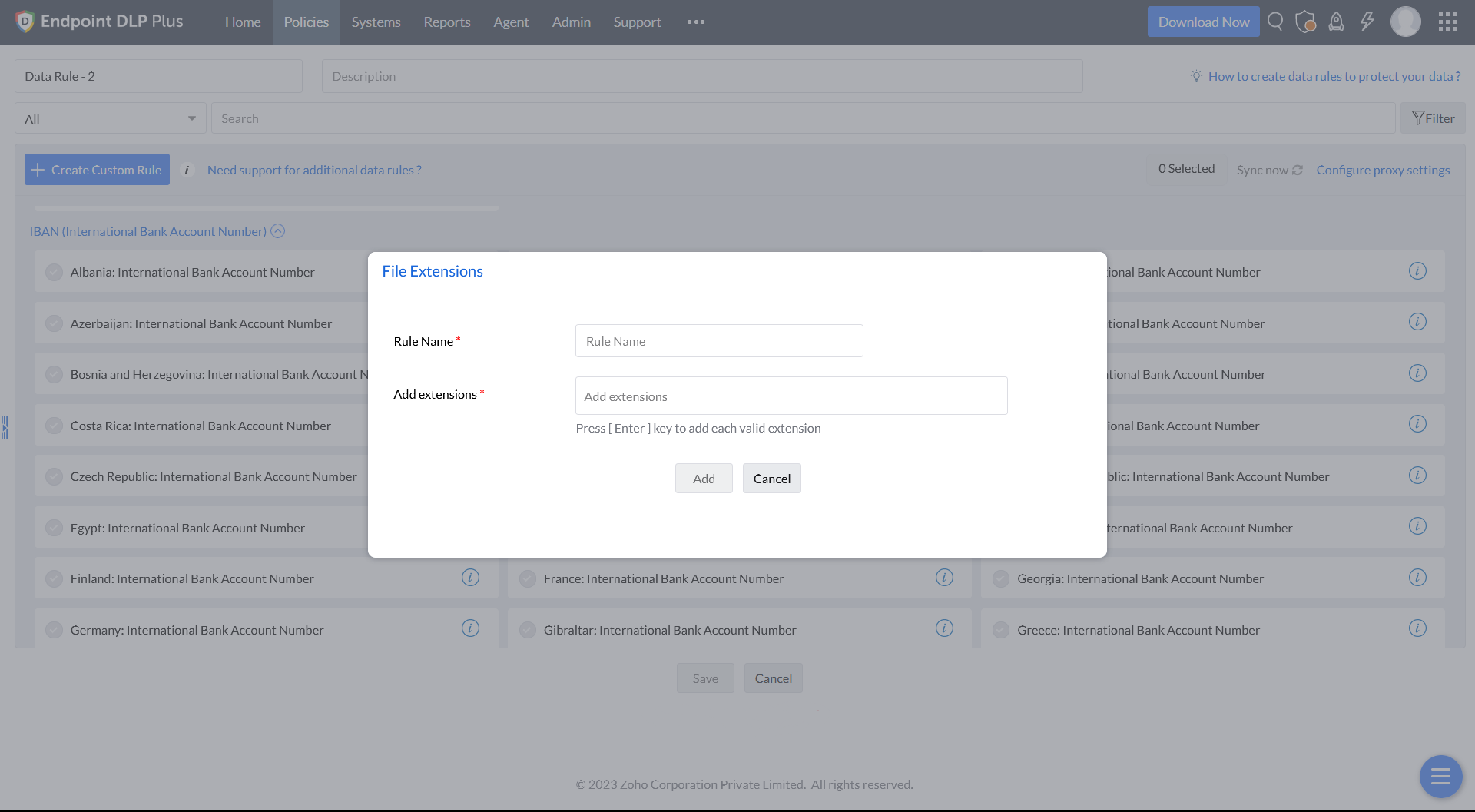
Step 10
In the File Extensions, enter the Rule Name, and Add extensions.
Step 11
Once criteria are selected, Save the rule to associate with a policy.