Manual Microsoft 365 tenant configuration
If the automatic configuration was not successful due to permission issues, the tenant must configured manually. To do that, select Click here to configure with an already existing Azure AD application. Please note that you can also opt to configure manually and skip the automatic configuration altogether with the option provided.
Manual tenant configuration involves the following three steps:
- Create an Entra application
- Configure the Entra application in M365 Security Plus
Steps to create an Entra application
- Log in to the Microsoft Entra ID admin center using the credentials of a Global Administrator or any other user account with the permission to create an Entra applications.
- Navigate to Identity > Applications > App registration.
- Click New registration.
- Provide a Name for the M365 Security Plus application to be created.
- Select a supported account type based on your organizational needs.
- Leave Redirect URI (optional) blank; you will configure it in the next few steps.
- Click Register to complete the initial app registration.
- You will now see the Overview page of the registered application.
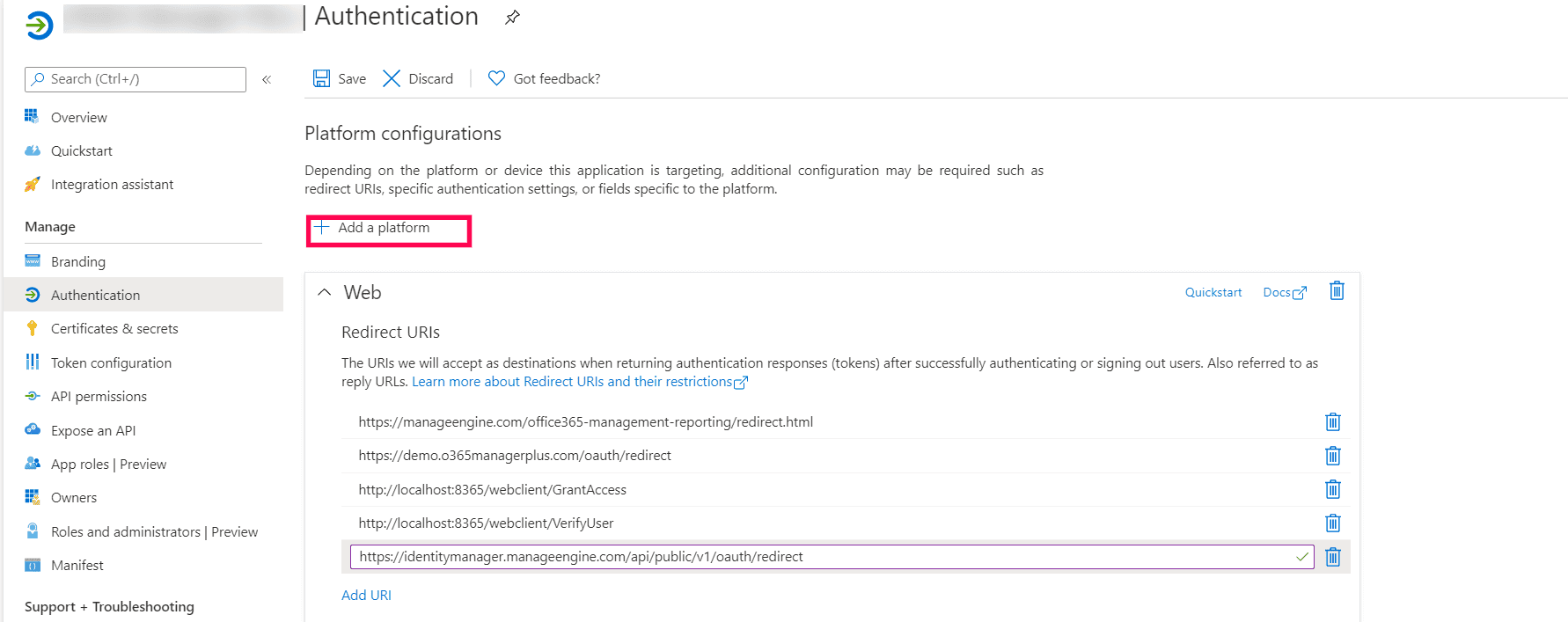
- Navigate to Authentication in the side pane..
- Click Add a platform under Platform configurations.
- In the Configure platforms pop-up, under Web applications, click Web.
- In the Redirect URI field, enter the following links . You can enter only one link at a time. After you enter a link, click Configure and repeat the steps until all of the links are configured.
- http://localhost:<port_number>/webclient/VerifyUser.
- http://localhost:<port_number>/webclient/grantacces
- http://localhost:<port_number>/AADAppGrantSuccess.do
- http://localhost:<port_number>/AADAuthCode.do
- https://identitymanager.manageengine.com/api/public/v1/oauth/redirect
- https://demom365securityplus.com/oauth/redirect
- https://manageengine.com/microsoft-365-security-protection/redirect.html where <port_number> refers to the port used by M365 Security Plus.
Note:
- The machine name or IP address can be used in place of <localhost> if the product is configured to use HTTPS. Open Command Prompt and enter ipconfig to find your machine's IP address.
- Please note that for users with M365 Security Plus build 4409 and above, Redirect URIs f and g are optional.
- You can leave the Logout URL and Implicit grant fields empty. Click Save.
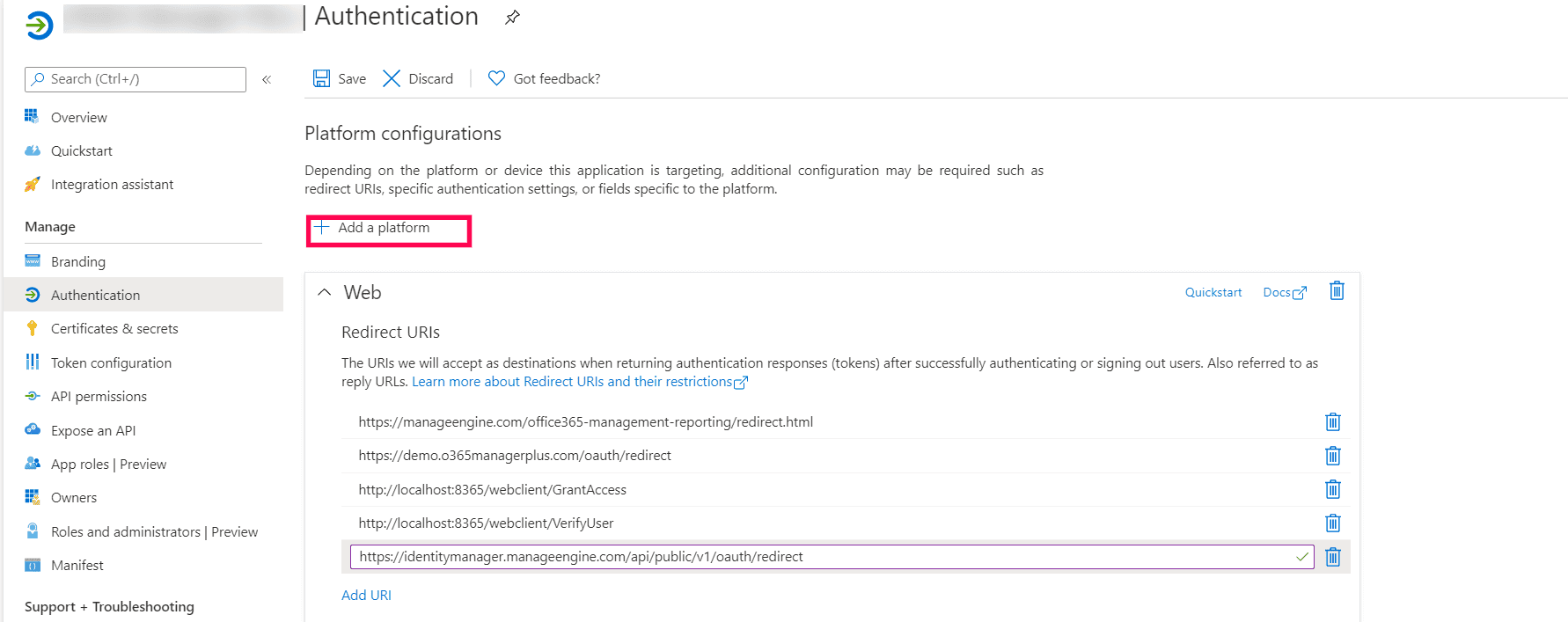
- Click Save.
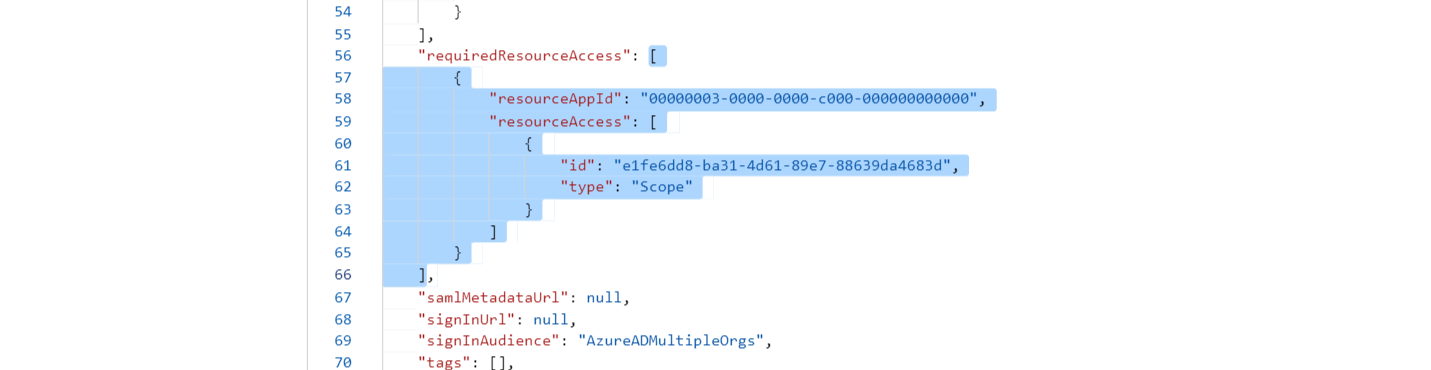
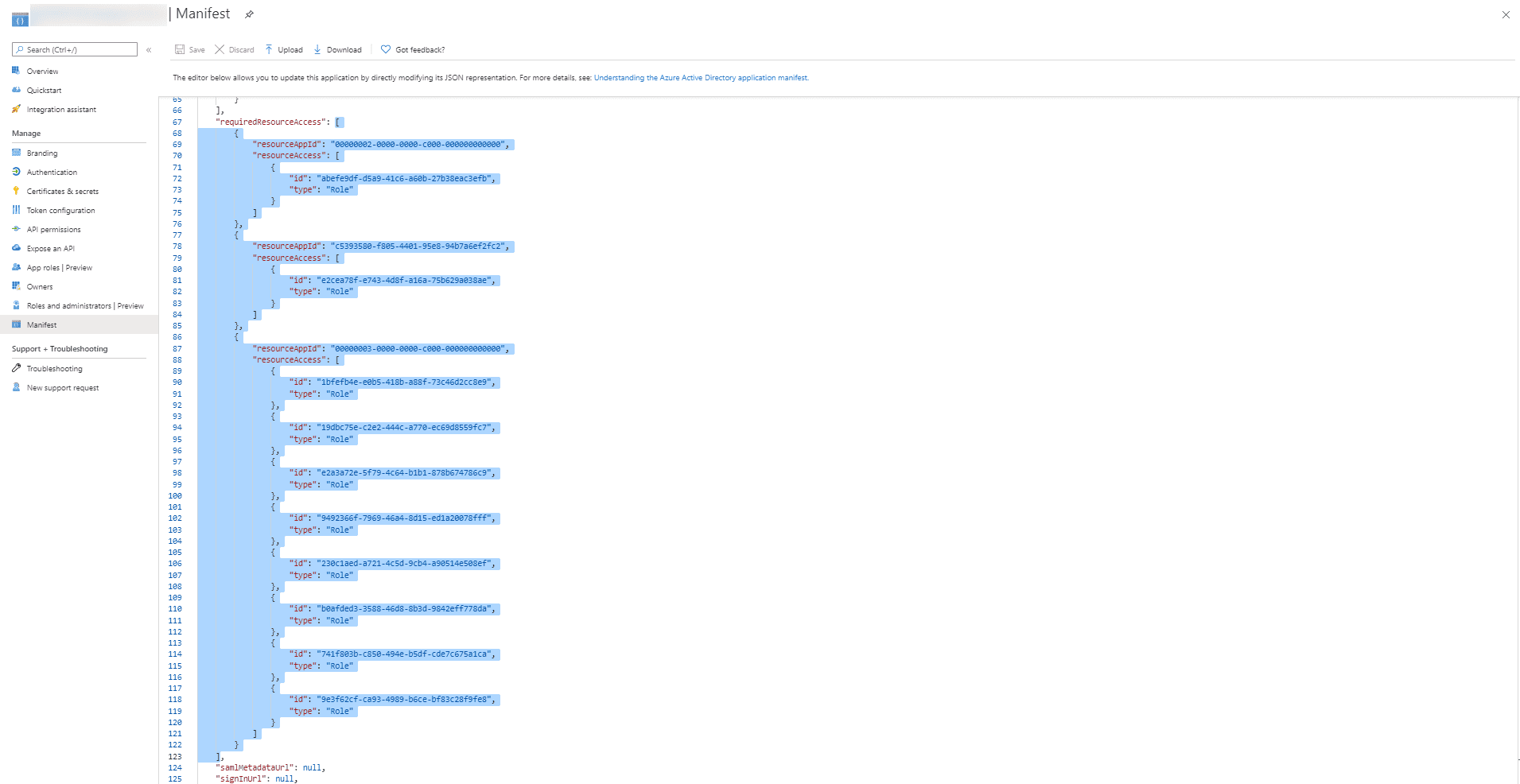
- Click Manifest from the left pane.
- Look for requiredResourceAccess array in the code.
- Copy the entire contents from this file and paste them into the section highlighted in the image below. If you want to modify the permissions to be provided, skip this step and follow the steps mentioned in this section.
Application scopes mentioned in the file
Microsoft Graph scopes
- Application.ReadWrite.All
- Directory.ReadWrite.All
- Mail.ReadWrite
- Sites.ReadWrite.All
- Reports.Read.All
- AuditLog.Read.All
- User.ReadWrite.All
- RoleManagement.ReadWrite.Directory
- ServiceHealth.Read.All
- Policy.Read.All
- Calendars.Read
- AdministrativeUnit.ReadWrite.All
- ChannelMember.Read.All
- Group.ReadWrite.All
- InformationProtectionPolicy.Read.All (Not available in Azure china tenants)
Office 365 management API scopes
- ActivityFeed.Read
- ActivityFeed.ReadDlp
Office 365 Exchange Online
- full_access_as_app
- Exchange.ManageAsApp
SharePoint Online API scopes
- Sites.Read.All
- Sites.FullControl.All
To know more about minimum scopes, click here.
Note:
- If your tenant is being created in Azure China, copy the entire contents from this file and paste them into the section highlighted in the image below.
Note: Copy-paste content only from the open square bracket to the closed square bracket. Ensure that all punctuation marks are retained correctly. Once you have pasted the file, it should look like the image below.
- Click Save.
- Click API permissions from the left pane.
- In the Configured permissions section, click ✓ Grant admin consent for <your_company_name>.
- Click Yes in the pop-up that appears.
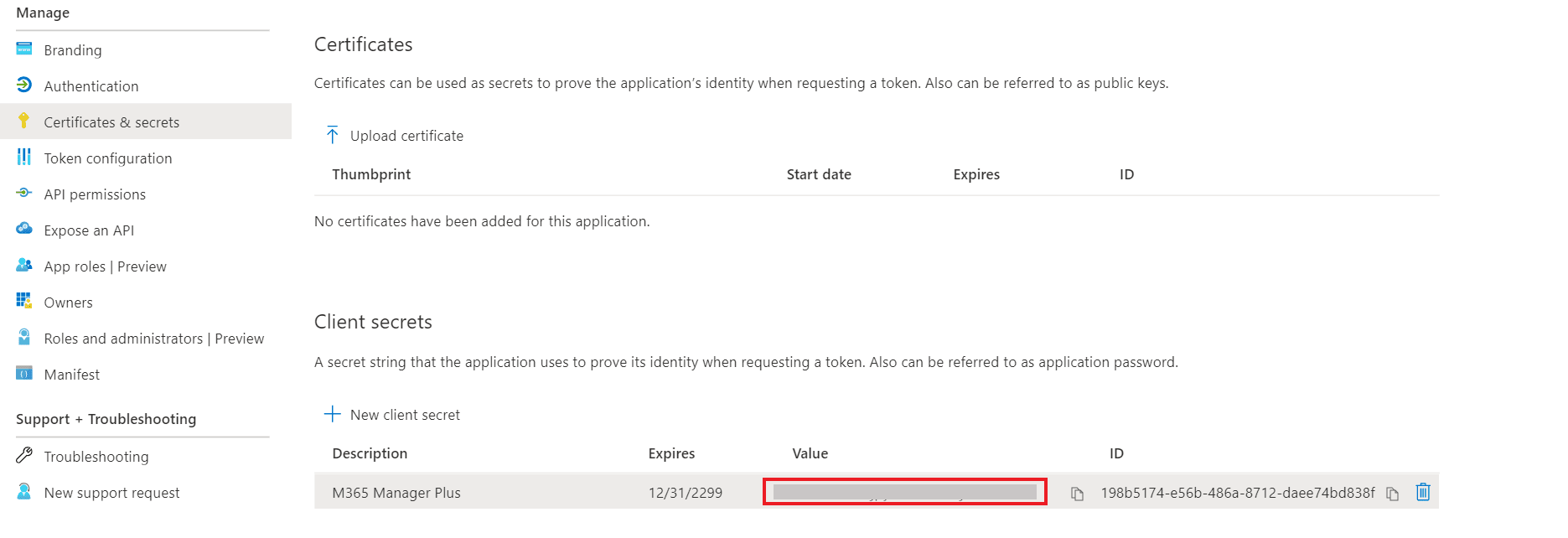
- Click Certificates & secrets from the left pane.
- Under the Client secrets section, click New client secret.
- This section generates an app password for M365 Security Plus. In the Description field of the pop-up, provide a name to identify the app to which the password belongs.
- Choose when the password should expire.
- Click Add.
- Copy the string under Value and save it. This is the Application Secret Key, which you will require later.
- Go to Certificates and click Upload certificate. Upload your application certificate as a CER file.
- If the user has an SSL certificate, the same can be used here. Otherwise, click here for steps to create a self-signed certificate.
Note: Certificate-based authentication is used to contact Microsoft 365 securely and fetch data. During manual configuration, you will be asked to enter your application secret and upload the Application Certificate.
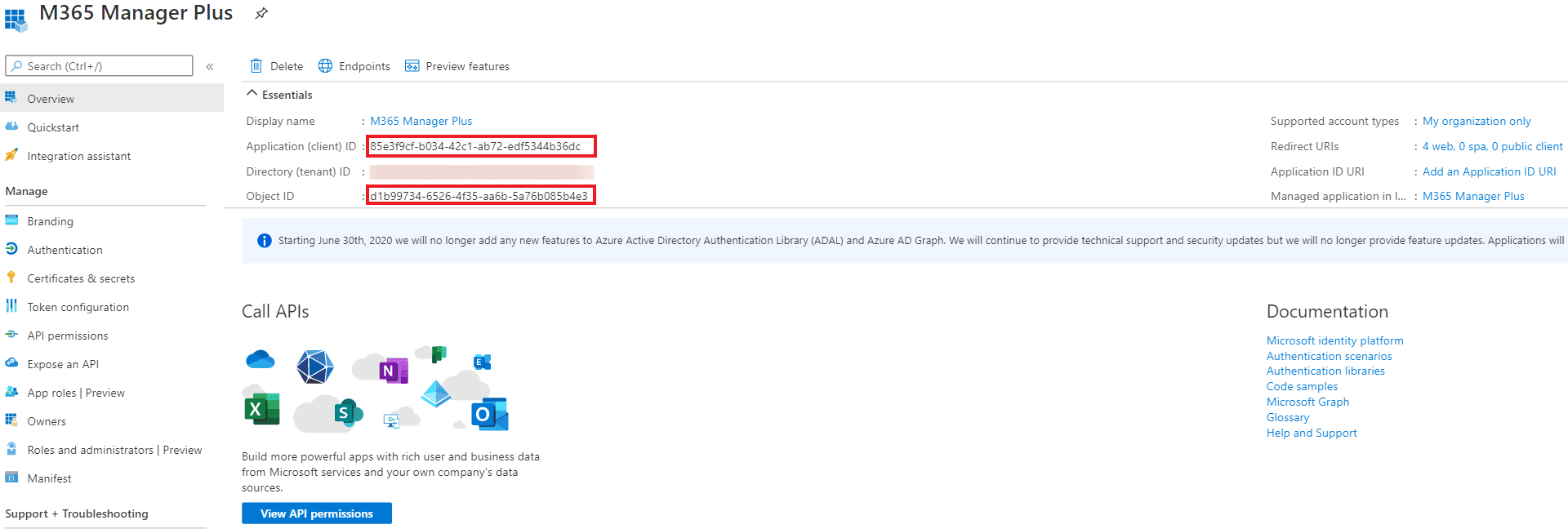
- Now go to the Overview section in the left pane.
- Copy the Application (client) ID and Object ID values and save them. You will need these values to configure your tenant in the M365 Security Plus portal.
- Refer to this table to learn about the roles that must be assigned to the application.
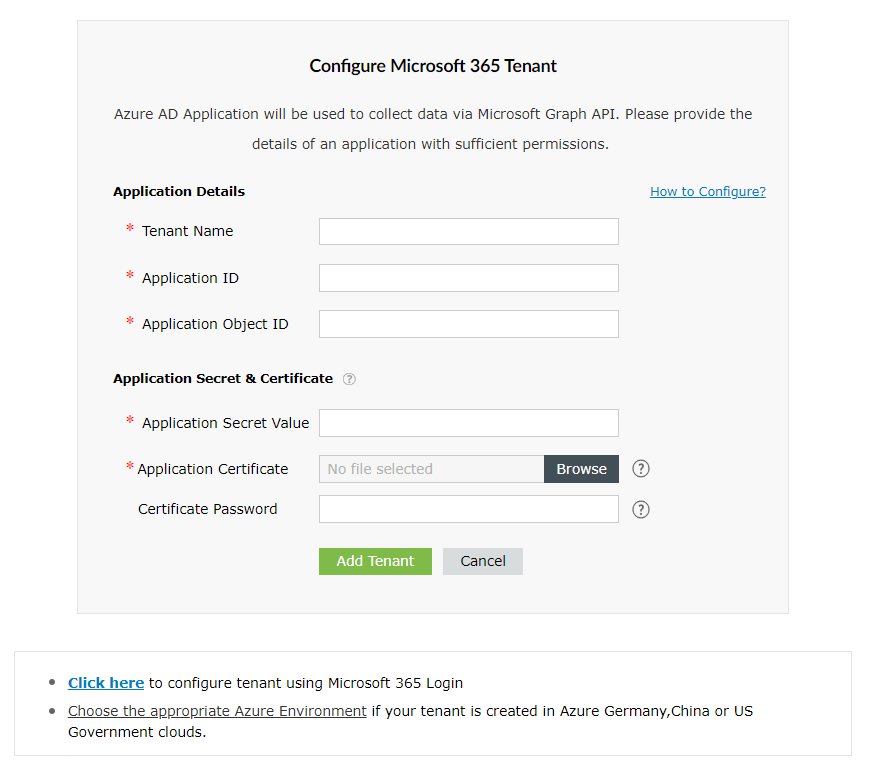
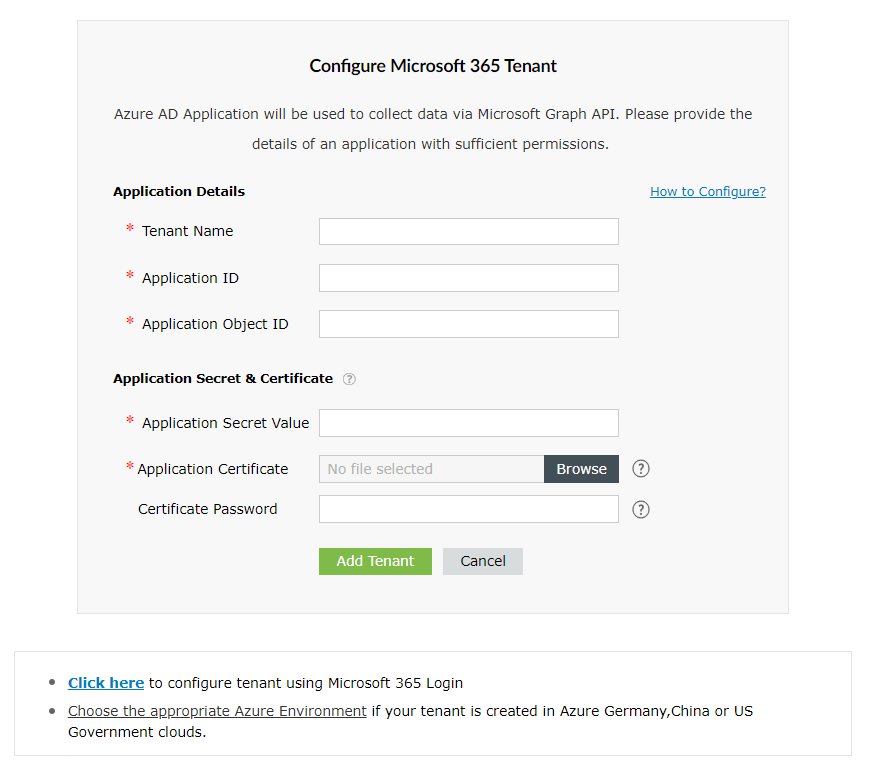
- Return to the M365 Security Plus console where you have the Configure Microsoft 365 Tenant pop-up.
- Enter your Tenant Name. For example, test.onmicrosoft.com.
- Paste the Application ID and Application Object ID values copied in Step 30 from the Steps to create an Entra application section into the respective fields.
- For the Application Secret Key, paste the value copied in Step 26 from the Steps to create an Entra application section.
- Upload a PFX file of the certificate that has been uploaded in the Microsoft Entra Admin Center. Refer to Step 27 in the Steps to create an Entra application section.
- Enter your certificate password.
- If you have an SSL certificate, you can upload the same in the appropriate field.
- Click Add Tenant.
- You should now see that REST API access is enabled for the account you configured.
Steps to create a self-signed certificate
- Run the following command in Windows PowerShell as an administrator:
Set-ExecutionPolicy -ExecutionPolicy RemoteSigned -Force -Scope process
- Navigate to the <Installation Directory>\bin folder and run the Create-selfsignedcertificate.ps1 script as an administrator.
- While running the script, you will be asked to add a common name for the certificate, start and end date (yyyy-MM-dd) for the certificate's validity, and a private key to protect it.
- Once you enter the values, the script will create a PFX file (contains both public and private key) in the bin folder.
- The PFX file needs to be uploaded in M365 Security Plus, while the CER file should be uploaded in the Application Overview page of your Microsoft Entra application.
Steps to modify a Microsoft 365 tenant
Once you have added a Microsoft 365 tenant, you can modify its details or delete it using the following options in the Actions column of the desired tenant:
- To set your preferred tenant as the default option for your actions in M365 Security Plus, click the default tenant
 icon.
icon.
- To refresh a tenant and fetch the most recent configurations, click the refresh
 icon.
icon.
- To edit an existing tenant, click the edit
 icon.
icon.
- To delete a Microsoft 365 tenant, click the delete
 icon.
icon.
- To troubleshoot a tenant for connectivity or configuration issues, click the troubleshoot
 icon.
icon.
Don't see what you're looking for?
-
Visit our community
Post your questions in the forum.
-
Request additional resources
Send us your requirements.
-
Need implementation assistance?
Try onboarding