- Free Edition
- What's New?
- Key Highlights
- Suggested Reading
- All Capabilities
-
Log Management
- Event Log Management
- Syslog Management
- Log Collection
- Agent-less Log Collection
- Agent Based Log collection
- Windows Log Analysis
- Event Log Auditing
- Remote Log Management
- Cloud Log Management
- Security Log Management
- Server Log Management
- Linux Auditing and Reporting
- Auditing Syslog Devices
- Windows Registry Auditing
- Privileged User Activity Auditing
-
Application Log Management
- Application Log Monitoring
- Web Server Auditing
- Database Activity Monitoring
- Database Auditing
- IIS Log Analyzer
- Apache Log Analyzer
- SQL Database Auditing
- VMware Log Analyzer
- Hyper V Event Log Auditing
- MySQL Log Analyzer
- DHCP Server Auditing
- Oracle Database Auditing
- SQL Database Auditing
- IIS FTP Log Analyzer
- IIS Web Log Analyzer
- IIS Viewer
- IIS Log Parser
- Apache Log Viewer
- Apache Log Parser
- Oracle Database Auditing
-
IT Compliance Auditing
- ISO 27001 Compliance
- HIPAA Compliance
- PCI DSS Compliance
- SOX Compliance
- GDPR Compliance
- FISMA Compliance Audit
- GLBA Compliance Audit
- CCPA Compliance Audit
- Cyber Essentials Compliance Audit
- GPG Compliance Audit
- ISLP Compliance Audit
- FERPA Compliance Audit
- NERC Compliance Audit Reports
- PDPA Compliance Audit reports
- CMMC Compliance Audit
- Reports for New Regulatory Compliance
- Customizing Compliance Reports
-
Security Monitoring
- Threat Intelligence
- STIX/TAXII Feed Processor
- Threat Whitelisting
- Real-Time Event Correlation
- Log Forensics
- Incident Management System
- Automated Incident Response
- Linux File Integrity Monitoring
- Detecting Threats in Windows
- External Threat Mitigation
- Malwarebytes Threat Reports
- FireEye Threat Intelligence
- Application Log Management
- Security Information and Event Management (SIEM)
- Real-Time Event Alerts
- Privileged User Activity Auditing
-
Network Device Monitoring
- Network Device Monitoring
- Router Log Auditing
- Switch Log Monitoring
- Firewall Log Analyzer
- Cisco Logs Analyzer
- VPN Log Analyzer
- IDS/IPS Log Monitoring
- Solaris Device Auditing
- Monitoring User Activity in Routers
- Monitoring Router Traffic
- Arista Switch Log Monitoring
- Firewall Traffic Monitoring
- Windows Firewall Auditing
- SonicWall Log Analyzer
- H3C Firewall Auditing
- Barracuda Device Auditing
- Palo Alto Networks Firewall Auditing
- Juniper Device Auditing
- Fortinet Device Auditing
- pfSense Firewall Log Analyzer
- NetScreen Log Analysis
- WatchGuard Traffic Monitoring
- Check Point Device Auditing
- Sophos Log Monitoring
- Huawei Device Monitoring
- HP Log Analysis
- F5 Logs Monitoring
- Fortinet Log Analyzer
- Endpoint Log Management
- System and User Monitoring Reports
-
Log Management
- Product Resources
- Related Products
- Log360 (On-Premise | Cloud) Comprehensive SIEM and UEBA
- ADManager Plus Active Directory Management & Reporting
- ADAudit Plus Real-time Active Directory Auditing and UBA
- ADSelfService Plus Identity security with MFA, SSO, and SSPR
- DataSecurity Plus File server auditing & data discovery
- Exchange Reporter Plus Exchange Server Auditing & Reporting
- M365 Manager Plus Microsoft 365 Management & Reporting Tool
- RecoveryManager Plus Enterprise backup and recovery tool
- SharePoint Manager Plus SharePoint Reporting and Auditing
- AD360 Integrated Identity & Access Management
- AD Free Tools Active Directory FREE Tools
To protect from security attacks, it is essential for a company to deploy various security solutions such as vulnerability scanners, endpoint security protection tools, perimeter security devices and so forth. This leaves security administrators overwhelmed with the number of security alerts they get each day. The sheer volume of false positives clouds the judgment of the security administrators, forcing them to go on a wild-goose chase or to miss major indicators of compromise.
Despite deploying a slew of security solutions, businesses still come under malware attacks. It's not uncommon to see big and small enterprises alike to suffer data breaches despite their defense-in-depth systems firing away at the right time. The problem here is the lack of contextual understanding of security information required to distinguish an actual threat from the false positives. A smart way of solving this problem is to deploy a security solution that can consolidate information from all the security tools to provide the contextual view of what’s happening on the network.
Comprehending security data with EventLog Analyzer to enrich contextual information
Hackers often try to intrude a network by exploiting vulnerabilities in the systems. However, the first step of every security attack is breaking the perimeter defense system. Hence to combat the external security breaches effectively, it becomes essential for security administrators to improve their vulnerability and endpoint security data analytics.
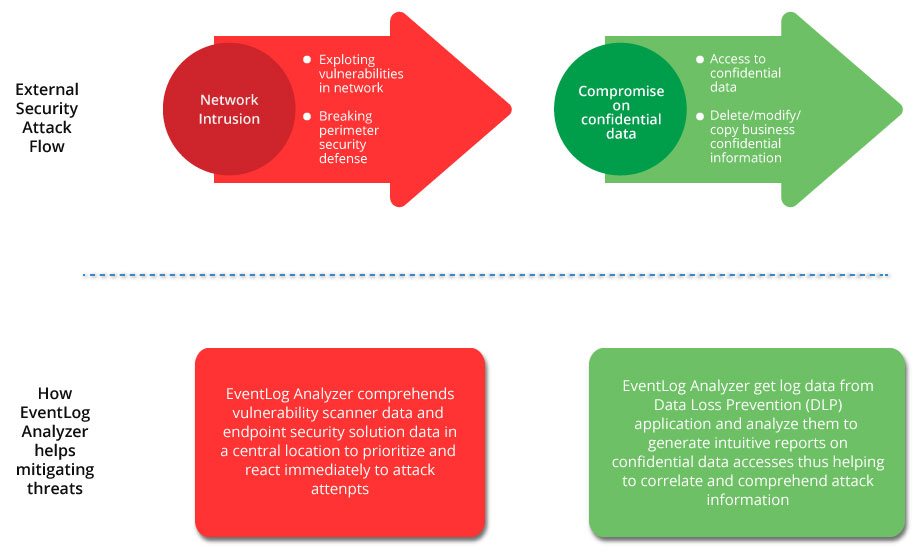
EventLog Analyzer helps security administrators to get a comprehensive view of all security information in a single dashboard by aggregating data from security tools such as vulnerability scanners, Data Loss Prevention (DLP) application and endpoint security solution
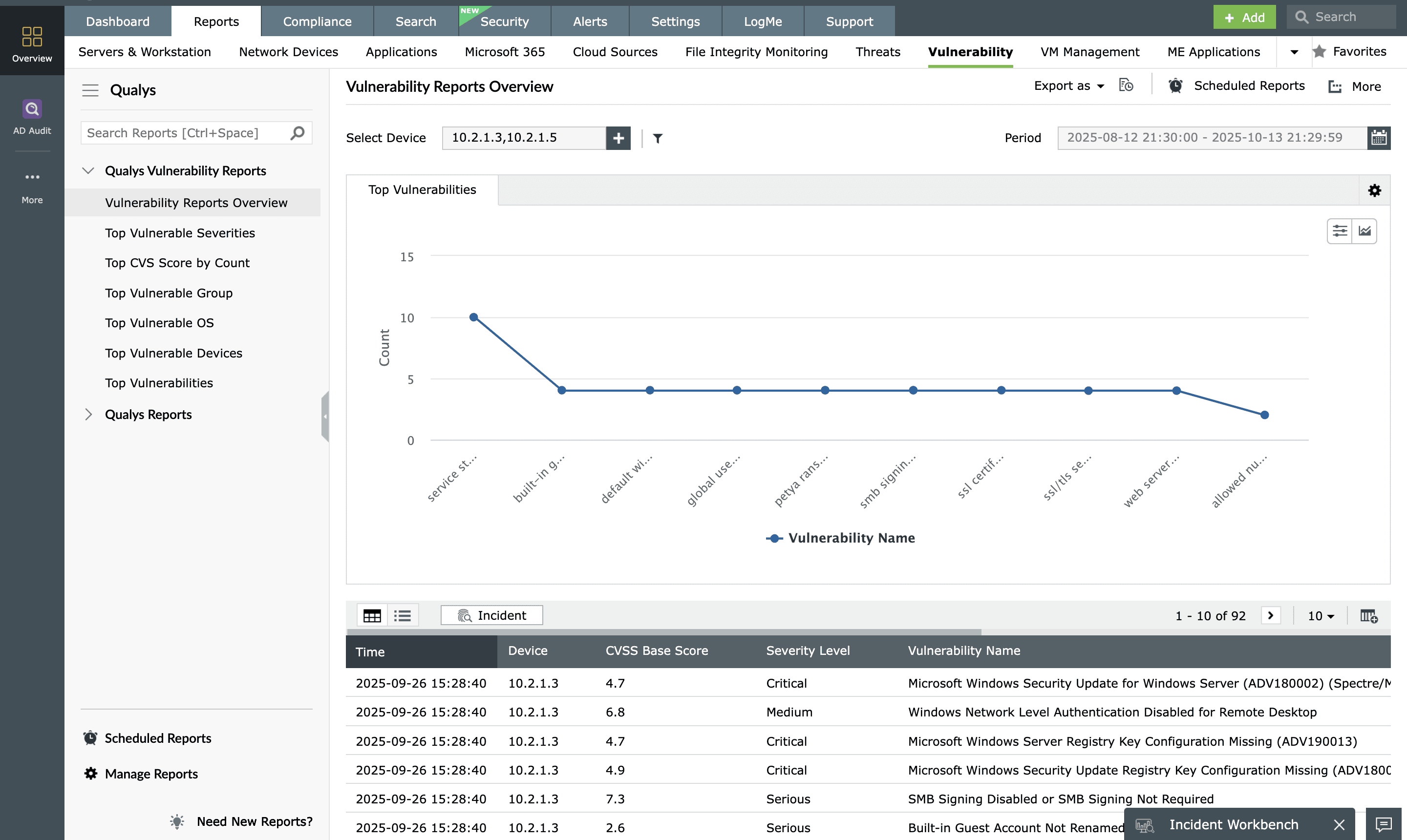
Support to vulnerability scanners
EventLog Analyzer supports log data from vulnerability scanners such as Nessus, Qualys, OpenVas, and NMAP.
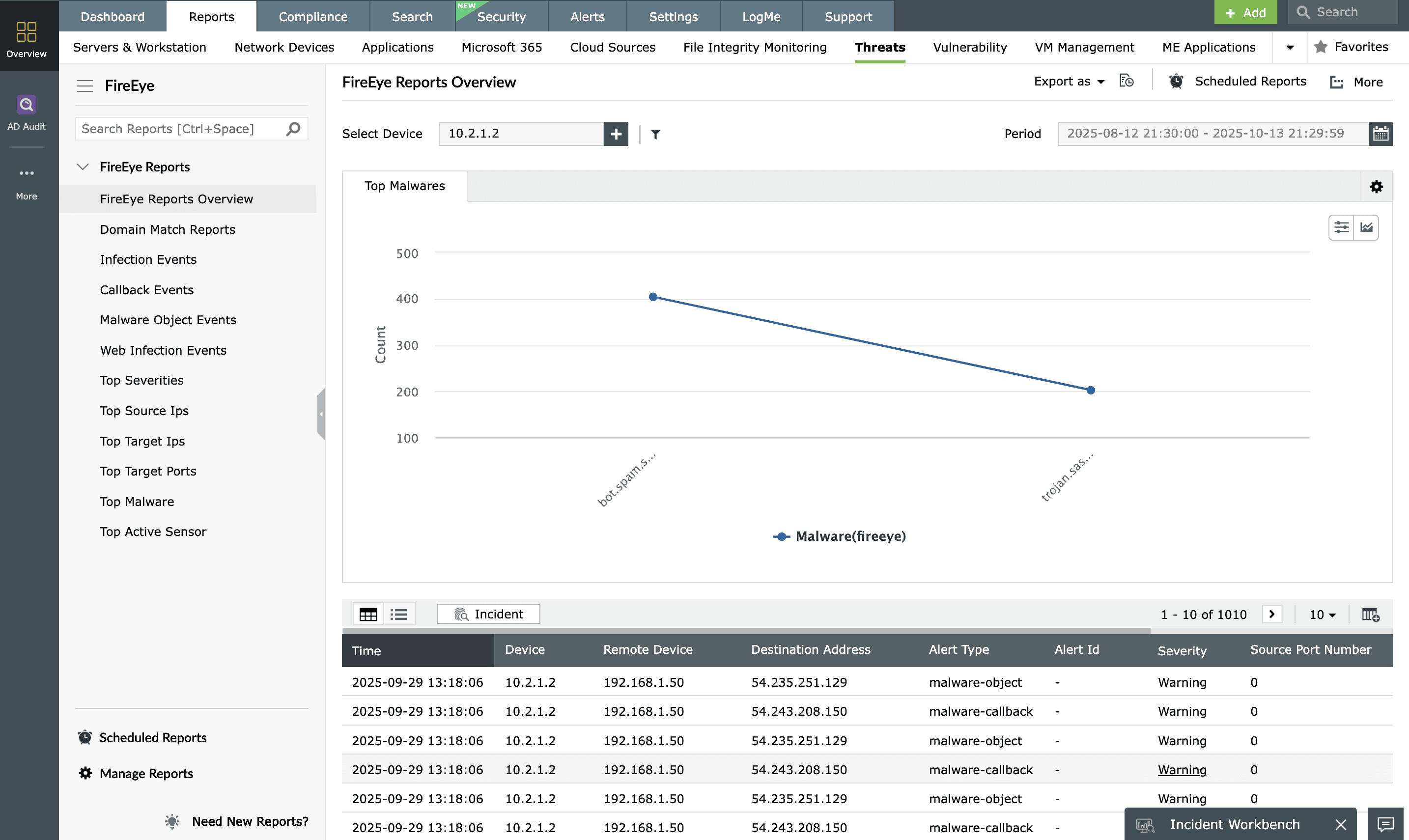
Support to threat intelligence applications
EventLog Analyzer consolidates security information from threat intelligence applications such as FireEye and Symantec Endpoint Protection in a central location.
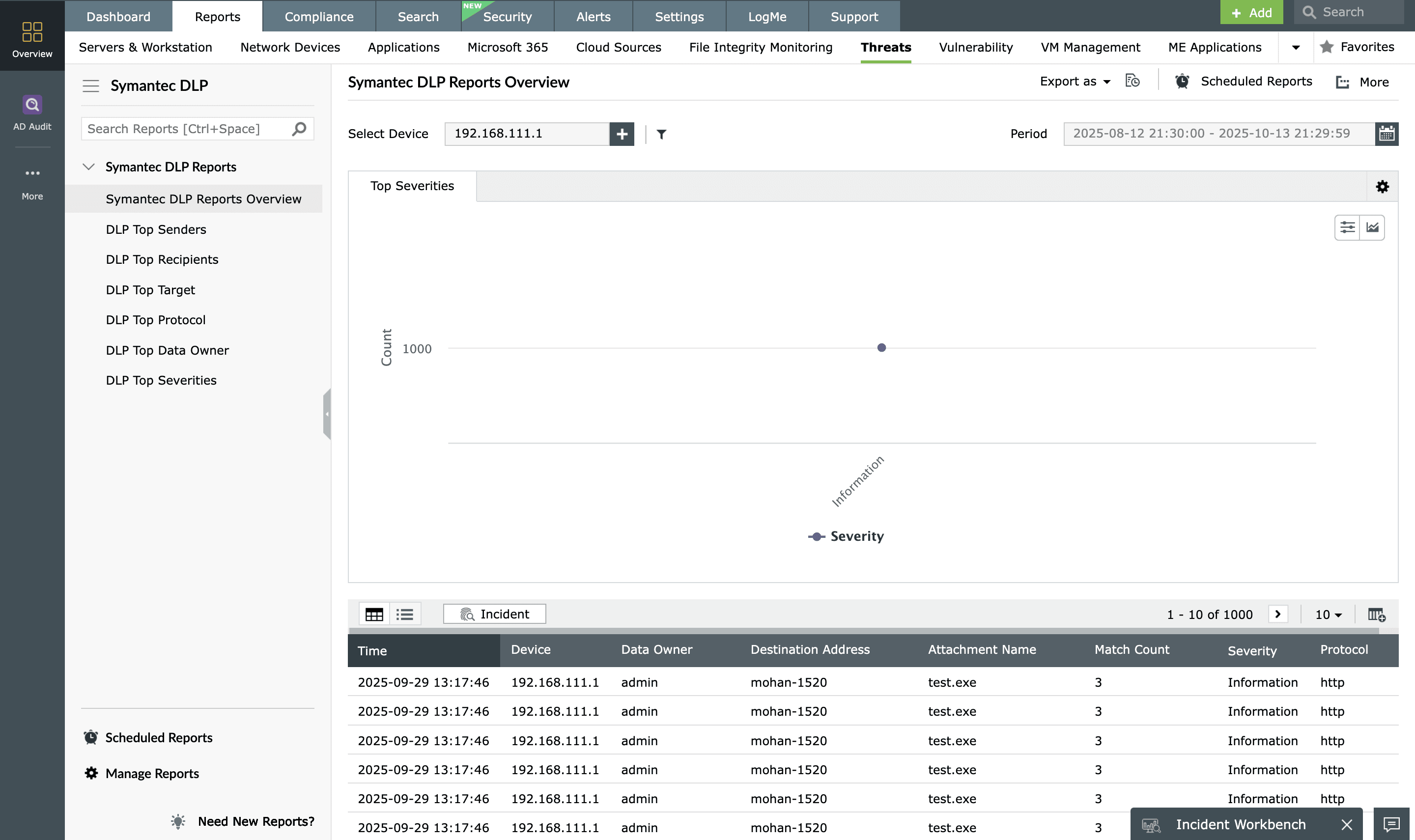
Support to Data Loss Prevention (DLP) application
EventLog Analyzer now supports log data from Symantec DLP application to ensure the integrity of confidential business information. The solution interprets the log data from Symantec DLP application and provides detailed information on top senders, recipients, protocol used, target data, data owners and more in an intuitive graphical format that helps comprehending information better.