Asset discovery and inventory
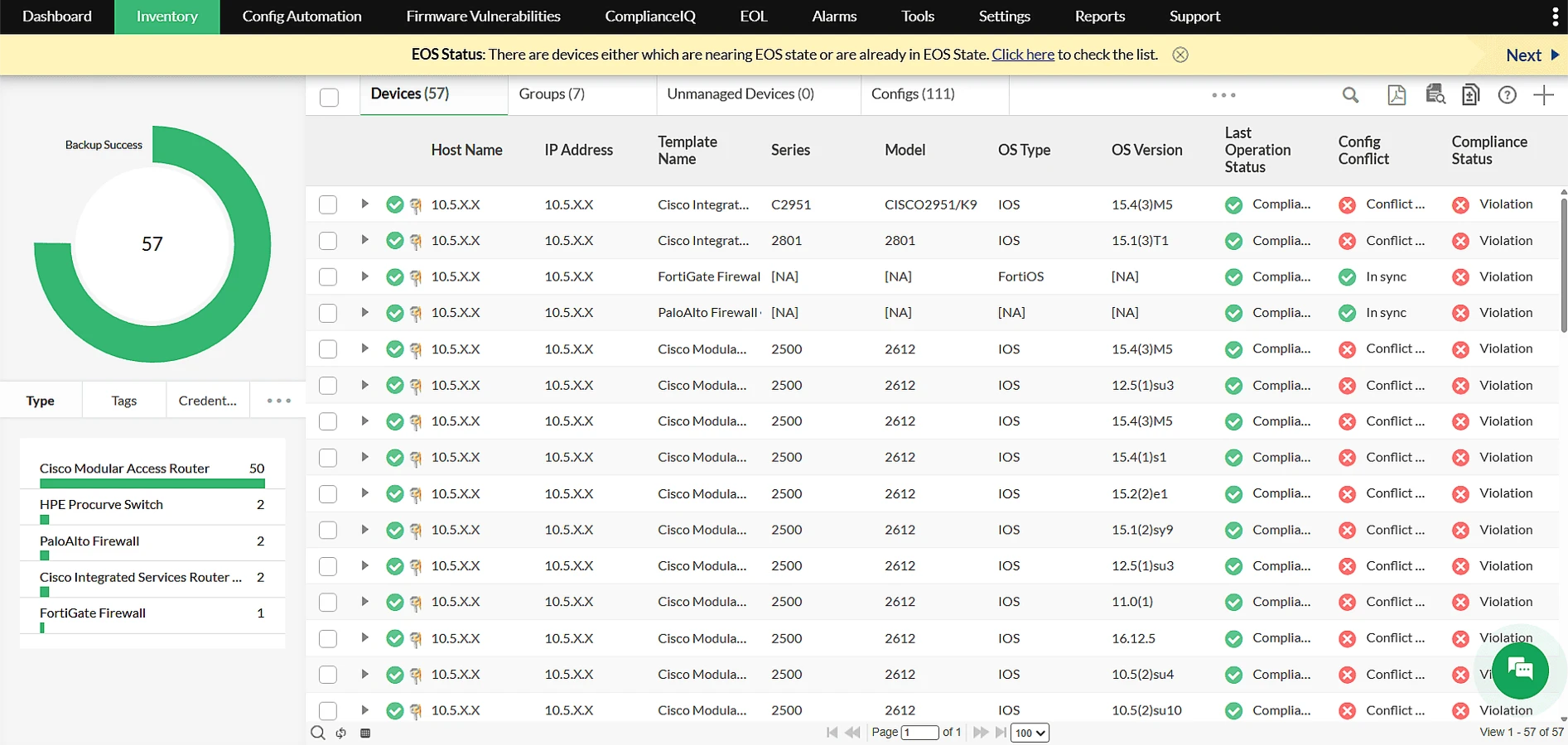
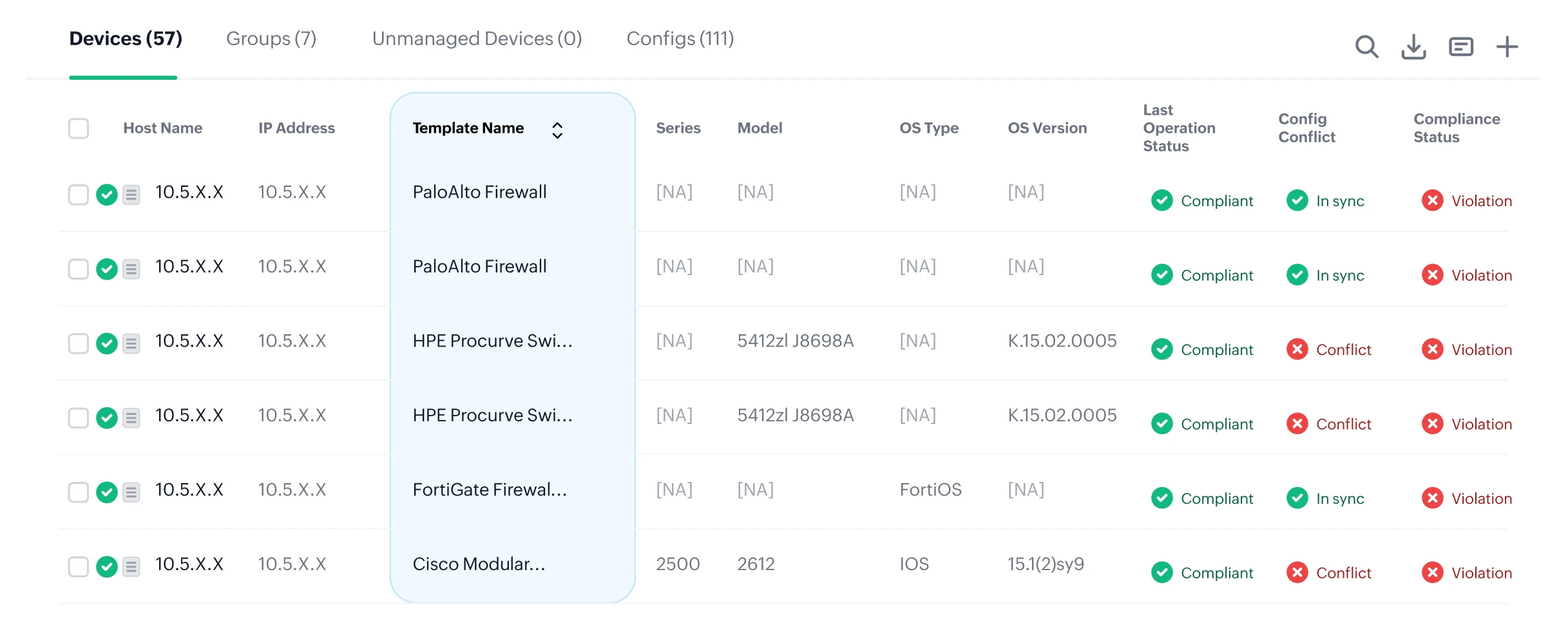
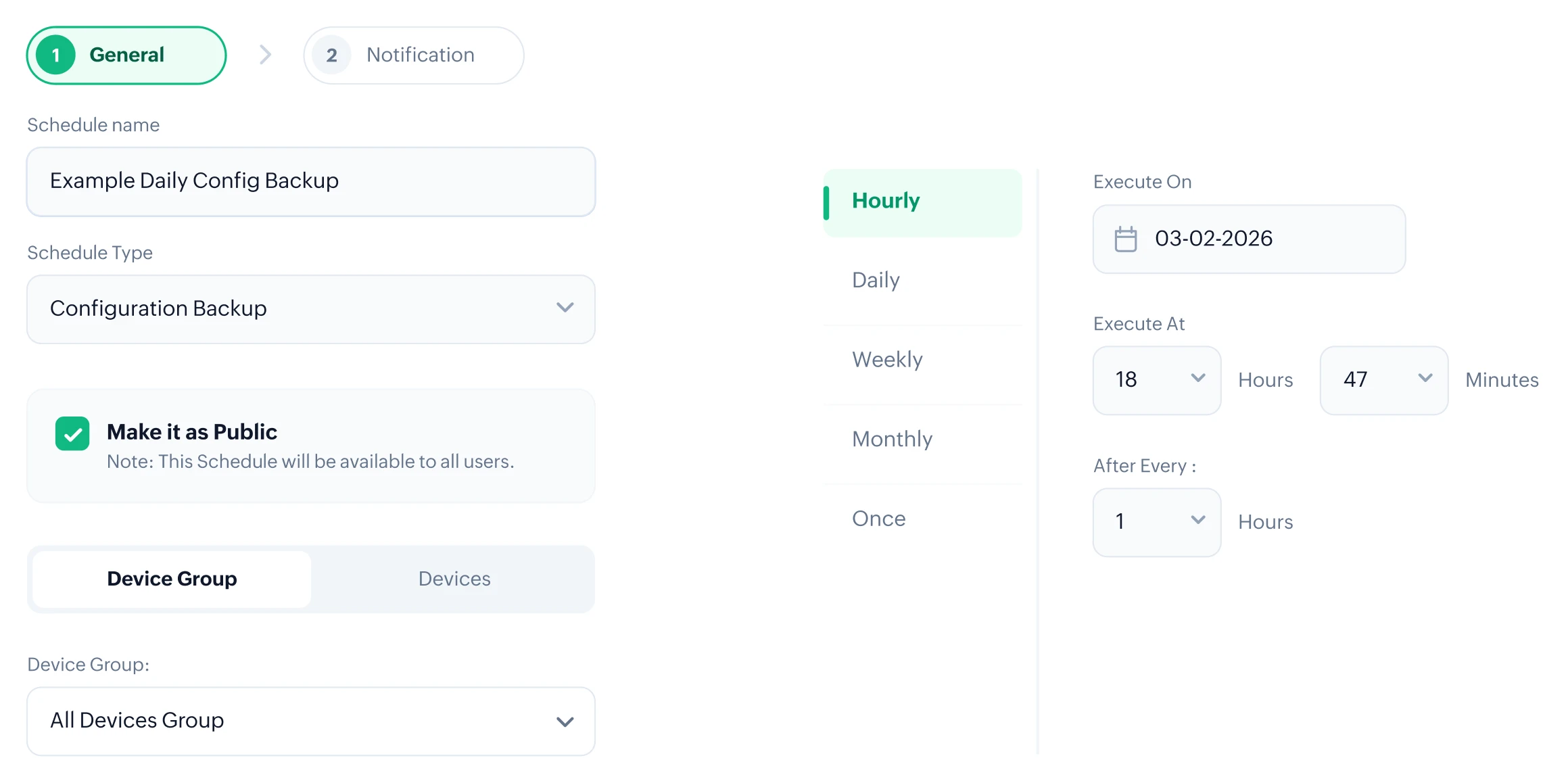
Centralize real-time device inventory
Auto-discover devices and view complete audit data like IP, firmware, compliance, configuration, and backup status in a single unified platform.
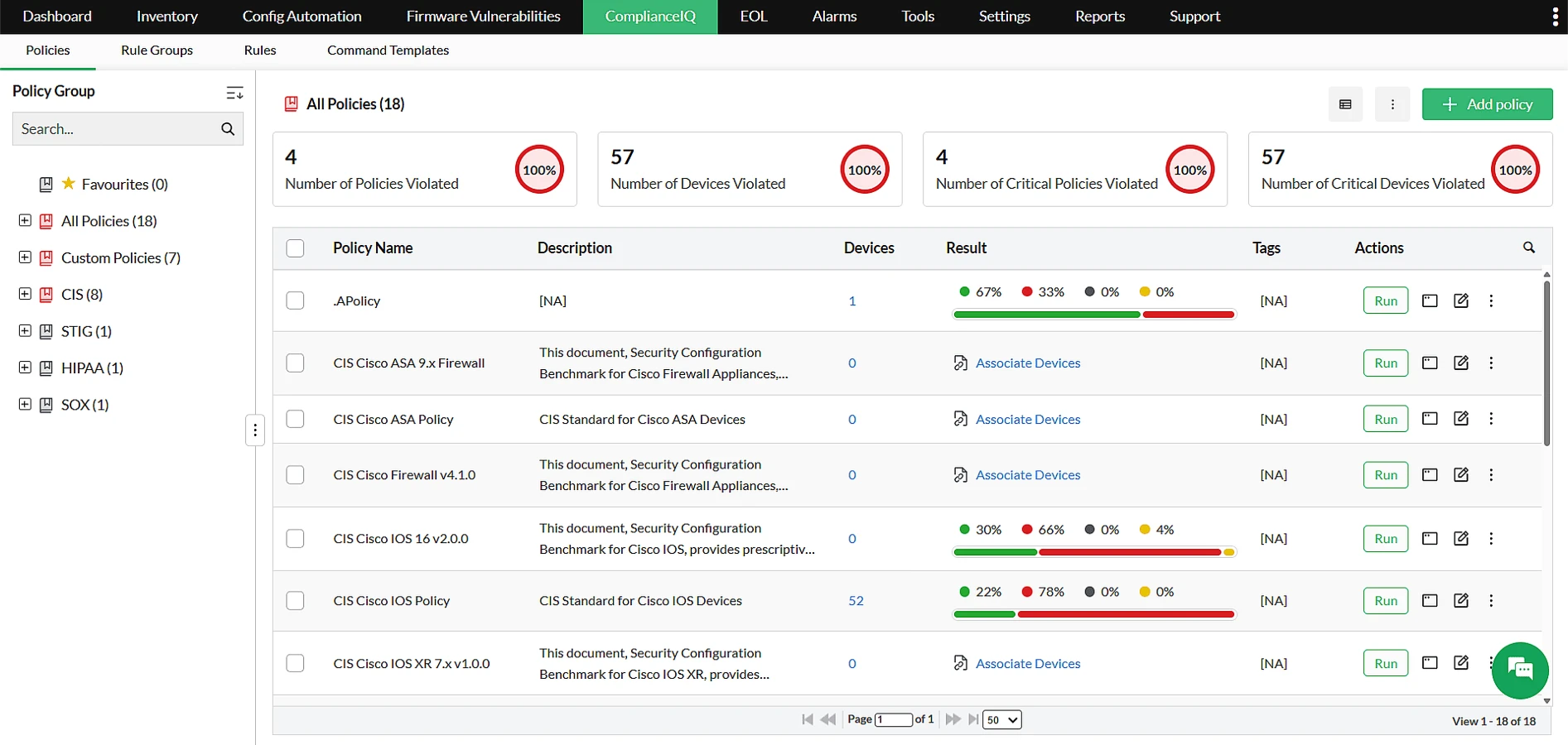
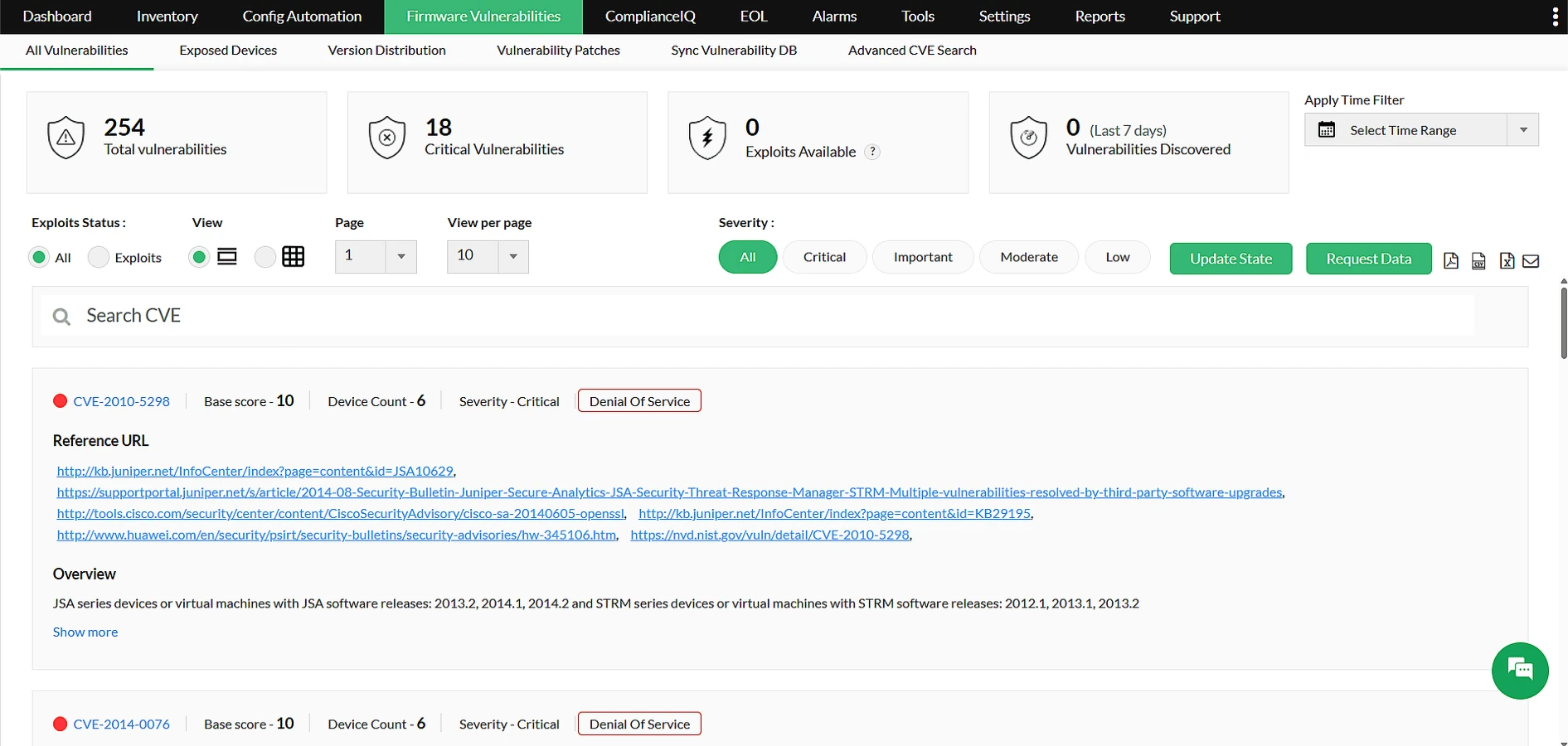
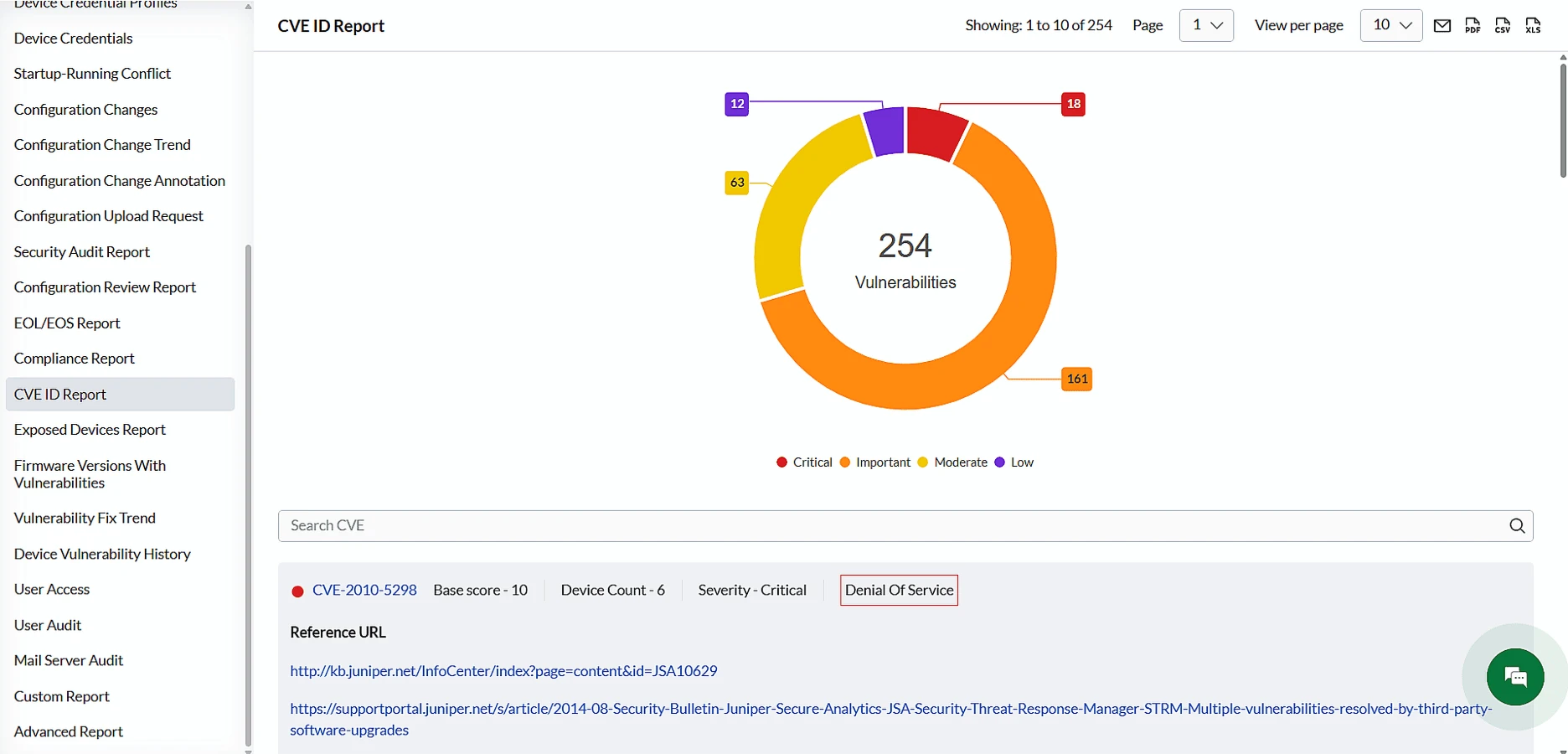
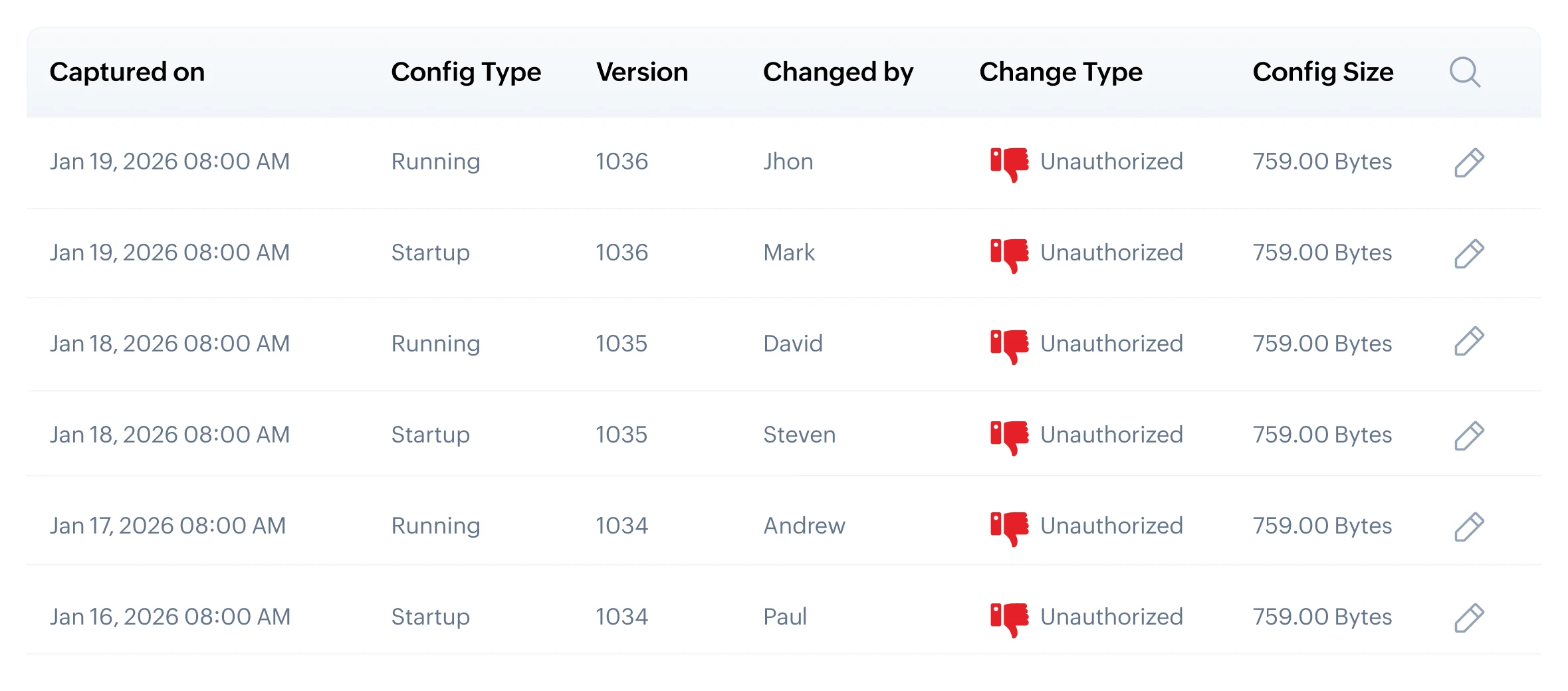
Expose risks and unmanaged changes early
Identify new, unmanaged, or misconfigured devices, along with configuration conflicts and backup failures before they impact operations.
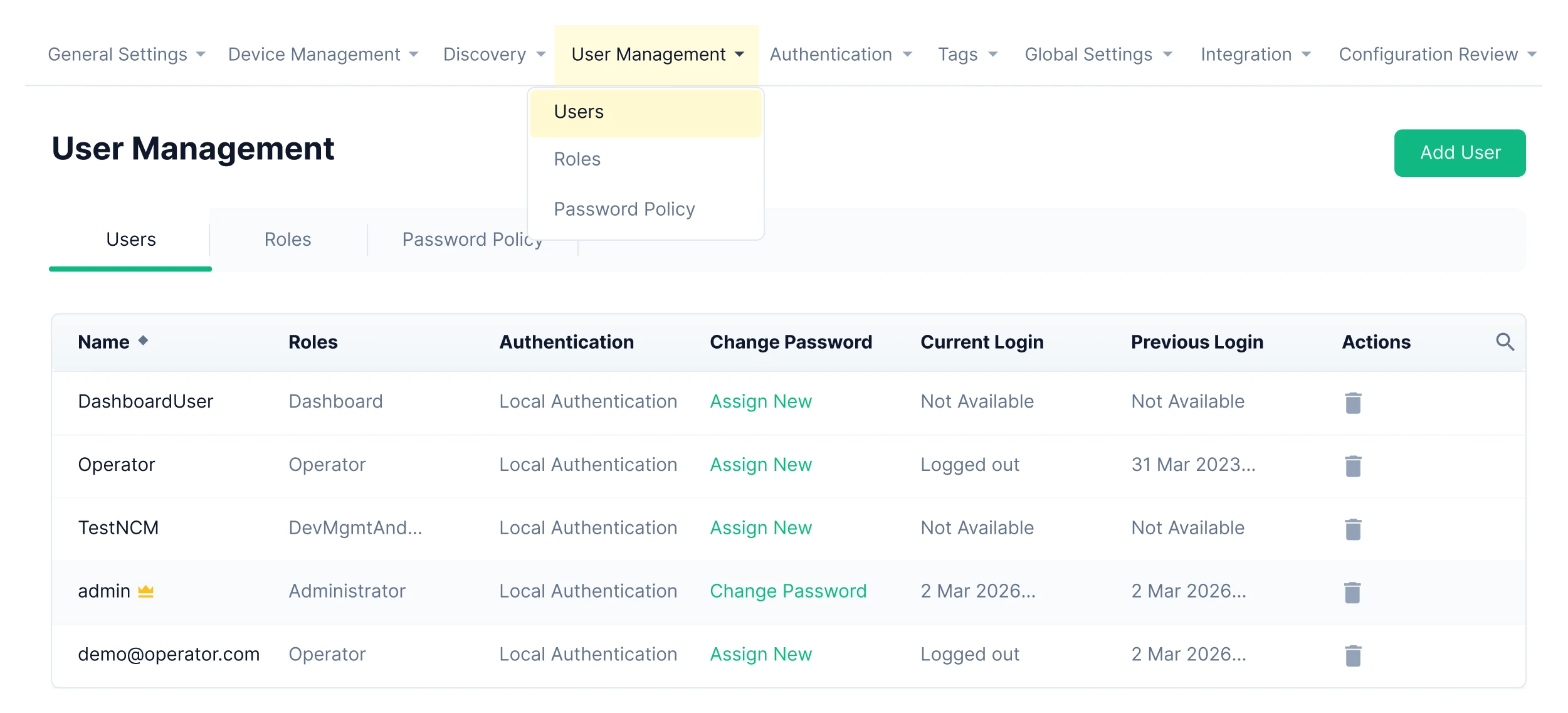
Maintain audit-ready infrastructure visibility
Keep accurate, up-to-date device metadata for audits, lifecycle tracking, and complete infrastructure awareness without fragmented visibility.