Direct Inward Dialing: +1 408 916 9892
Auditing activity on user account is a staple of security measures in all organizations. Since users have access to various resources on your network, the odds that your organization can face an insider threat is high. So it is important to monitor activity related to user accounts, such as a user being added to a privileged group, or a user account being created or disabled. You can track these changes by setting up an audit policy so you can view events related to user accounts.
This post is designed to quickly summarize everything you need to know about auditing user accounts. You can find information about events related to activity on user accounts on the Microsoft documents as well, but we're going ahead and bringing all the information together so you can properly configure your audit policy. We'll also tell you the benefit of using a premium tool like ADAudit Plus to track events related to user accounts.
Note: You could configure this from the 'Local Policy' settings in the window as well, but it is better that you configure user account management auditing from the 'Advanced Audit Policy' setting. Configuring 'Local Policy' generates a lot more irrelevant events and makes it difficult to track down events that you're actually looking for. Advanced Audit Policy settings, gives you more control over generating exactly the events that you're interested in.
As provided by the official Microsoft documentation, these are the events you can track when this audit policy is configured. This is applicable to Windows 10 and Windows Server 2016 versions.
While all these events are specific to user account management, you will find that some of them (Event IDs 4722, 4725, 4724, and 4781) are also generated for computer accounts.
We also suggest you audit these policies for both 'success' and 'failure', so you can track important "failed" attempts at changing or resetting passwords and logons, for both domain and local accounts.
Event Viewer is the default native AD tool to view all your events. Although Event Viewer is a great tool, it is hard to look through all the messages and events and find a particular suspicious incident. We suggest opting for a premium solution like ADAudit Plus.
ADAudit Plus is a comprehensive solution that simplifies AD auditing and reporting. It is a one-stop platform that brings together an intuitive user interface, pre-configured reports, and advanced filter options that make it easy for you to track changes to your network, and detect threats immediately. You get a fully equipped dashboard that gives you a holistic view of the various systems in your network. This way you can correlate events across the network and spot suspicious behavior.
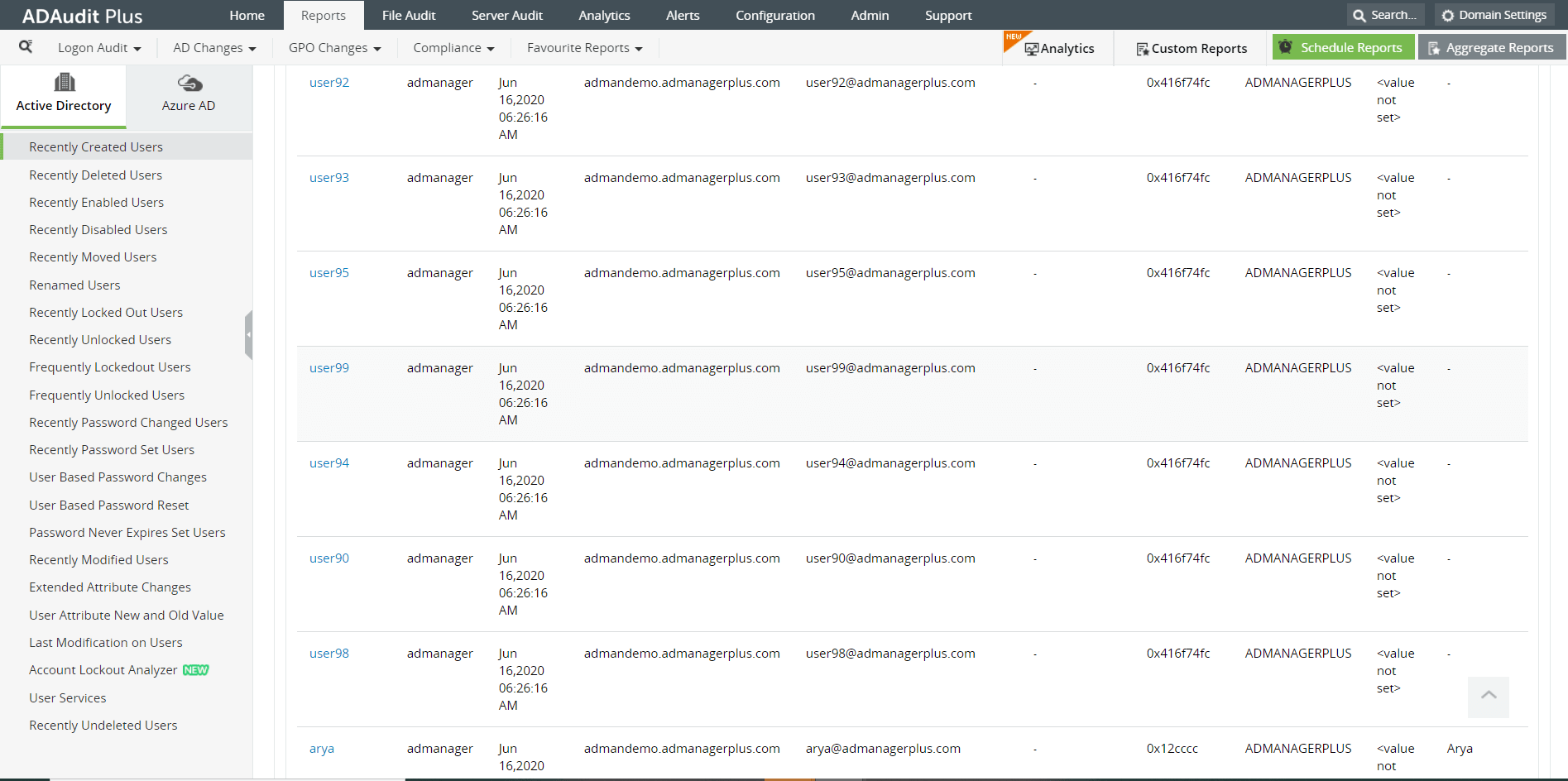
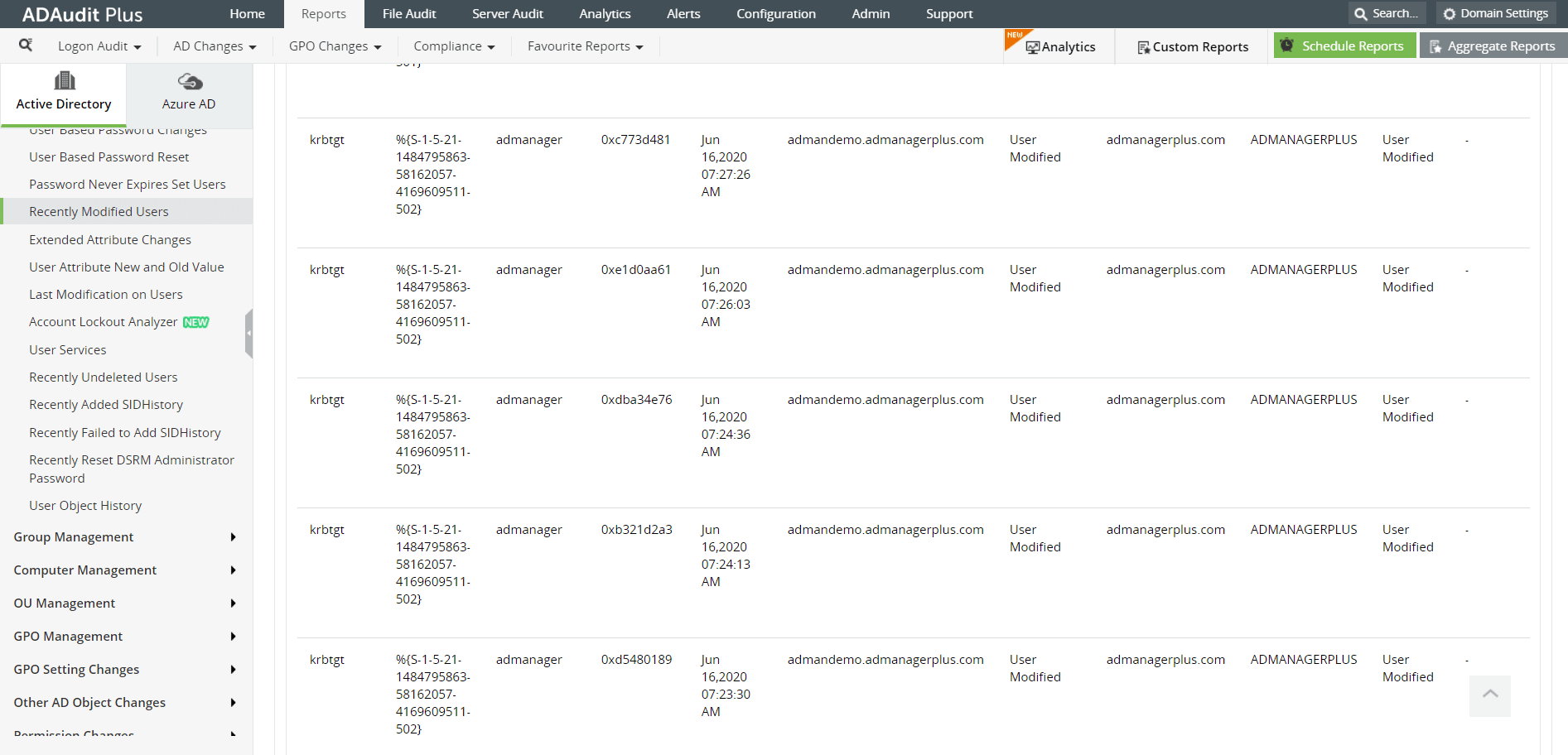
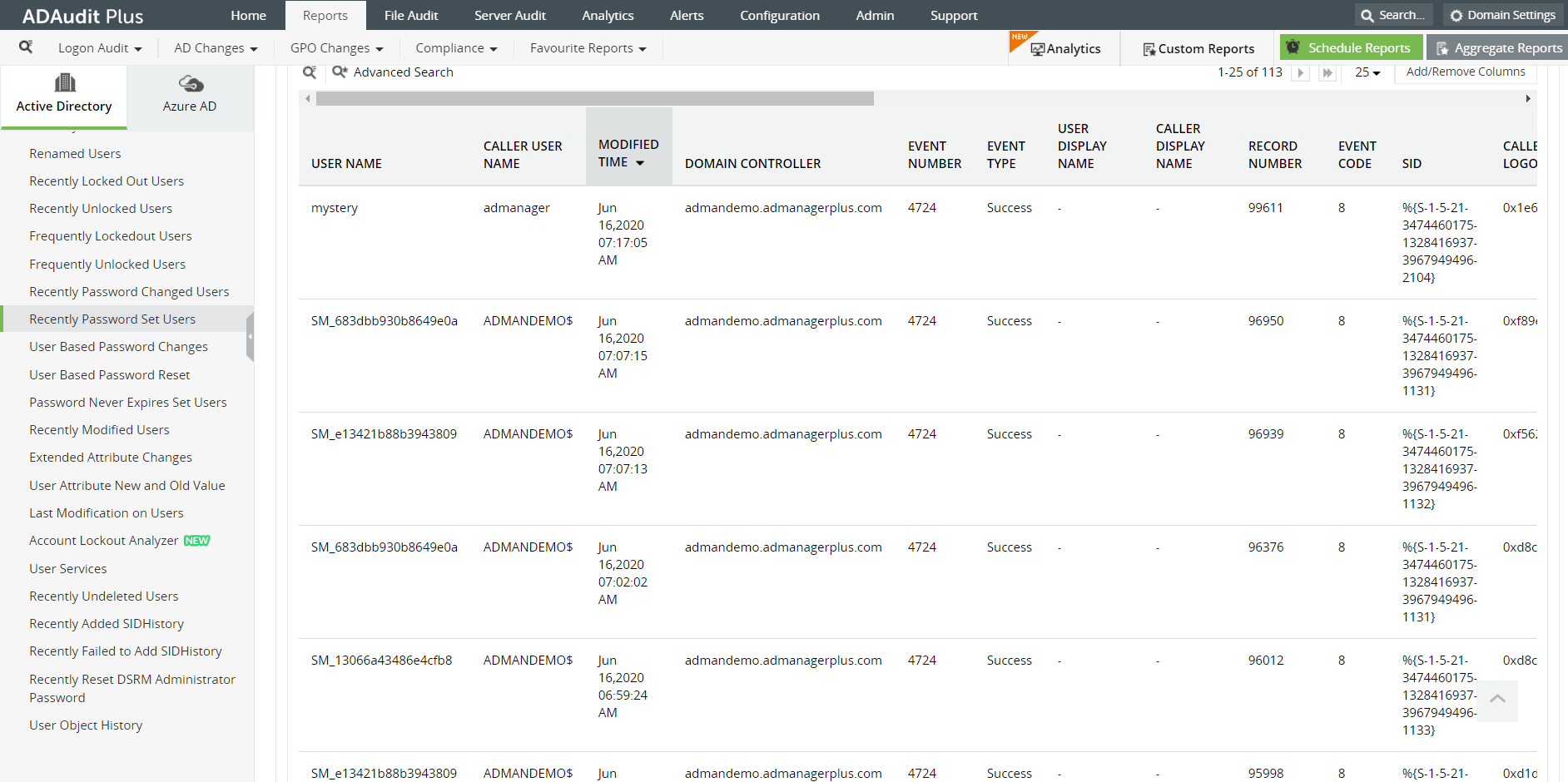
ADAudit Plus is a real-time, web-based Windows Active Directory (AD) change reporting software that audits, reports and alerts on Active Directory, Windows servers and workstations, and NAS storage devices to meet the demands of security, and compliance requirements. You can track AD management changes, processes, folder modifications, permissions changes, and more with 200+ reports and real-time alerts. You can also get out-of-the-box reports for compliance mandates such as the HIPAA. To learn more, visit https://www.manageengine.com/active-directory-audit/.
Try ADAudit Plus login monitoring tool to audit, track, and respond to malicious login and logoff actions instantaneously.
Try ADAudit Plus for free