In today's digital landscape, cybercriminals increasingly leverage the dark web to plan attacks, trade stolen data, and launch malware campaigns.
To enable proactive monitoring of the deep and dark web for leaked credentials, ManageEngine Log360 integrates with Constella Intelligence to enable users to identify personal information, such as credit card numbers, email information, usernames, and other credentials, leaked on the dark web. This integration equips you with a critical first line of defense against supply chain risks.
Explore how Log360's powerful monitoring capabilities address the challenges of leaked credentials, empowering security teams with:
- PII exposure detection Uncover leaked PII like login credentials and financial data.
- Proactive security Detect sensitive data leaks early to mitigate risks sooner.
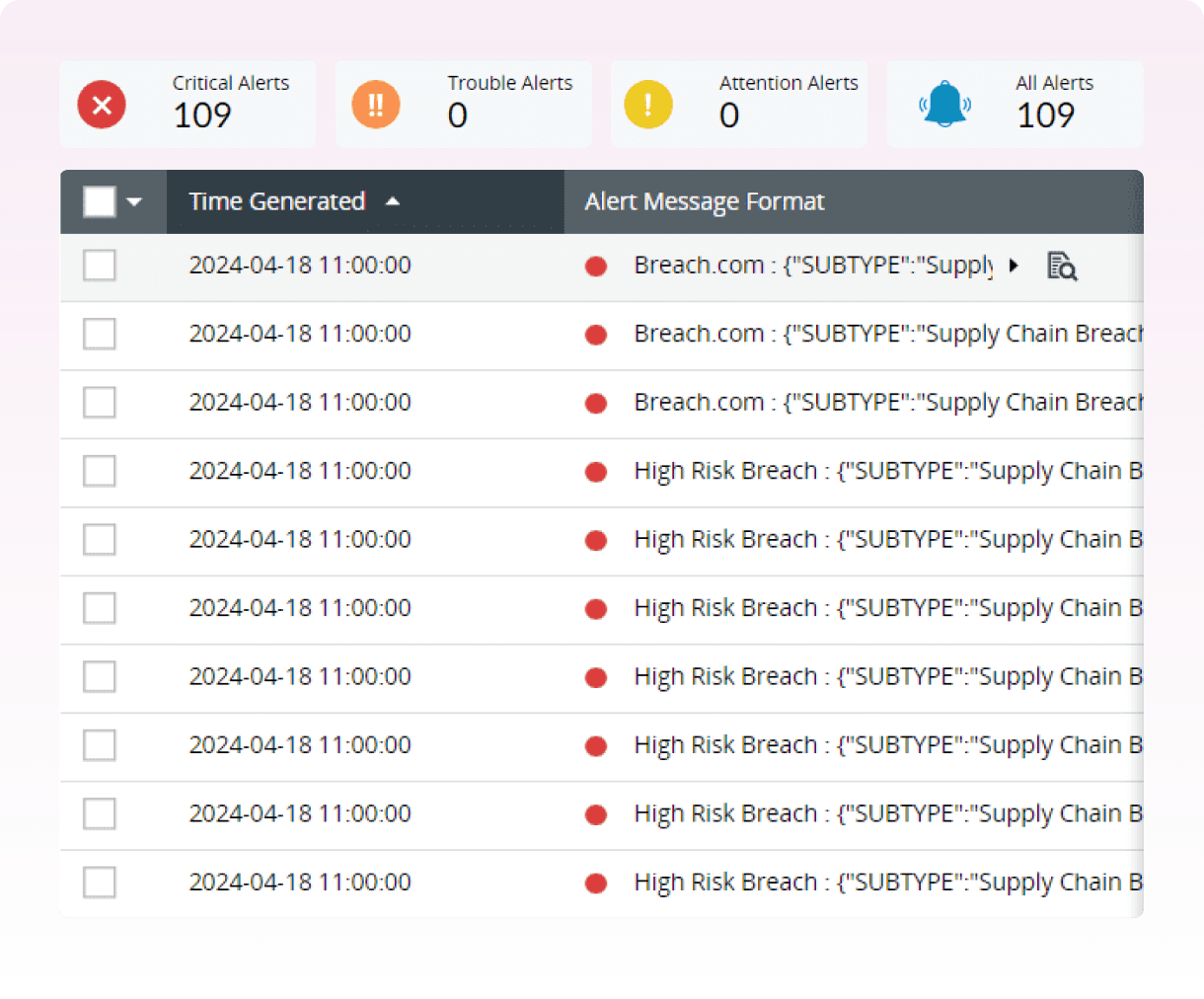
- Swift threat response Get instant alerts to investigate and resolve threats quickly.
Log360's dark web monitoring service
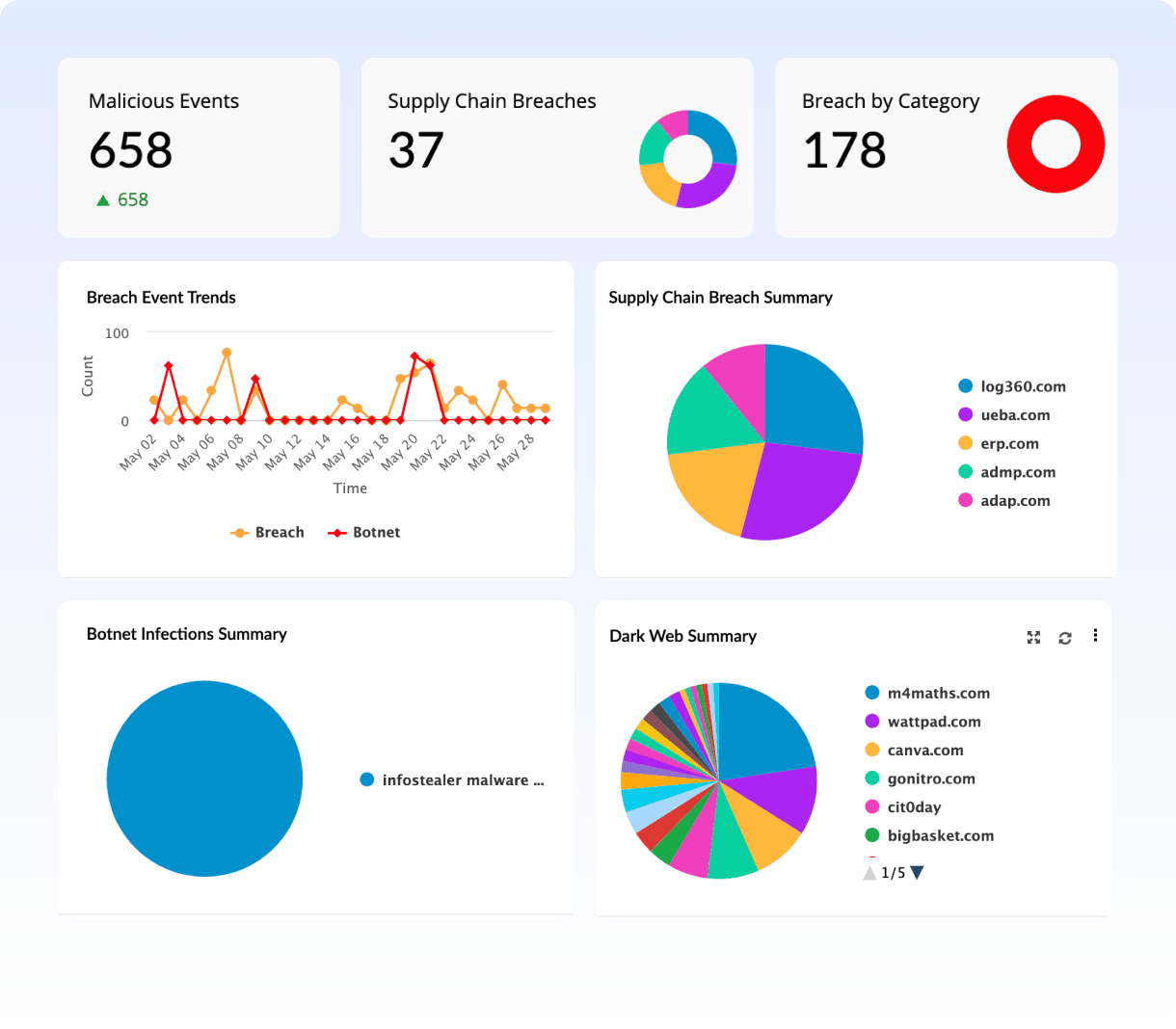
With Log360, you can monitor the dark web for any mention of an organization's sensitive information, including domain names, employee credentials, and financial information, such as credit card numbers. Detecting this information early empowers you to take swift action and mitigate potential breaches.
Credible dark web intelligence
The dark web facilitates the exchange of information and tools among cybercriminals, operating outside the reach of conventional cyber policing.
By leveraging credible dark web intelligence, you can gain visibility into the security threats that plague the dark web. Data is collected through specialized tools and techniques that are used to crawl the dark web for relevant information; the data is then verified for accuracy and enriched with additional context such as threat indicators, and that information is turned into actionable alerts for swift response.
Supply chain risk management: Proactive threat hunting and incident response
While malware injections, manipulator-in-the-middle attacks, and insider threats are common threats seen in supply chain attacks, attackers are increasingly targeting credentials through phishing and social engineering, bypassing traditional defenses.
Compromised employee credentials are a common entry point for attackers that is often overlooked. With its enhanced and global threat intelligence, Log360 can identify leaked credentials, enabling you to take action like enforcing password resets and implementing stricter access controls.
By automating incident response workflows, remediation can be performed by triggering password reset workflows on compromised accounts. This streamlines the response process and allows you to react swiftly to emerging threats.
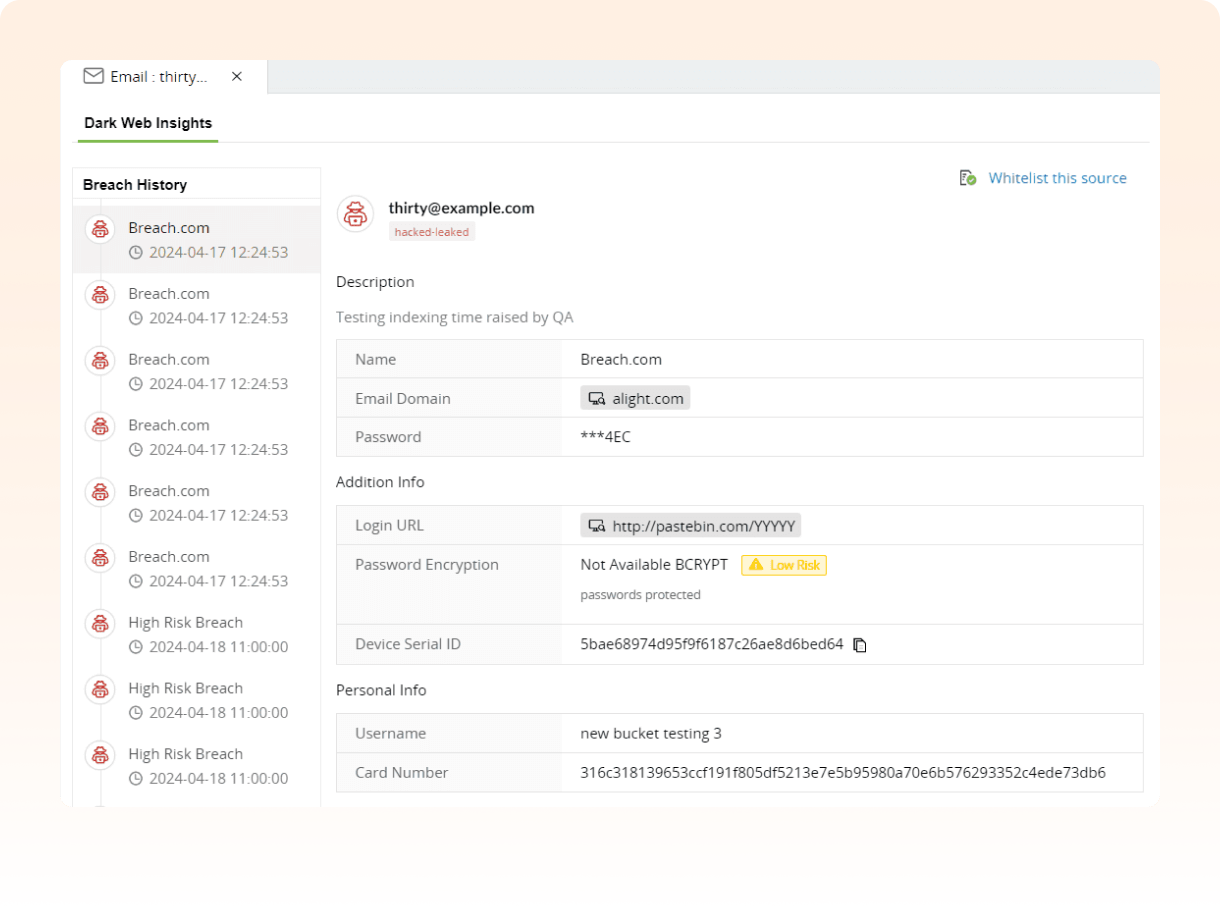
Utilize Log360's Incident Workbench to trace attacker movement and predict next steps
In the event of a compromised credential, by using the Incident Workbench to perform advanced analytics on the threat, you can track the attacker's next steps as they move laterally across the network or escalate their privileges. This enables you to effectively contain threats and minimize potential damage.
The Incident Workbench console adds contextual data, such as breach history, leaked data, usual login URL, password hash, and personal information, for effective threat hunting.
Log360's Dark Web Defense
-
24/7 dark web monitoring
Log360 scans the deep and dark web continuously for leaked credentials associated with organizations, their employees, and third-party vendors. This ensures that you are alerted about potential security risks before potential damage.
-
Detect PII exposure
Personally identifiable information (PII) leaks, such as credit card and Social Security numbers, are detected and notified on in real time.
-
Breach prevention
With Log360, you gain early visibility into potential supply chain vulnerabilities. This allows you to take action and prevent breaches before attackers can exploit these weaknesses.
-
Fraud detection and protection
Log360 tracks and immediately alerts on illegal credit card dumps and personal information leaks. This helps you to proactively approach unauthorized transactions and financial information leaks.
-
Faster threat analysis and resolution
Log360 provides instant alerts whenever leaked credentials or critical information are found on the deep and dark web.
-
Proactive security measures
Most regulatory mandates, such as the GDPR and the PCI DSS, mention implementing security measures to prevent data breaches. Dark web monitoring is one of the best security measures that you can adopt to identify the early signs of attacks and prevent them even before they occur.
Frequently asked questions
What is the dark web?
The dark web refers to a part of the internet that is intentionally hidden and inaccessible through standard web browsers and search engines. It consists of encrypted networks and websites that require specific software, such as the Tor (The Onion Router) browser, to access. This anonymity-focused technology allows users and websites to operate without revealing their identity or location, making it a haven for both illicit and legitimate activities that require privacy. The dark web is often associated with illegal marketplaces, forums for hackers, and other activities outside of mainstream online activities.
What is dark web monitoring?
Dark web monitoring involves actively tracking hidden online networks to detect and mitigate threats, including stolen data and illicit activities. It provides early detection of compromised information and helps organizations respond swiftly to potential cybersecurity risks before they escalate.
Why should you monitor the dark web?
- Gain early warnings of data breaches: Sensitive personal information like login credentials, Social Security numbers, and financial details often appear for sale on the dark web after data breaches. Monitoring this realm allows you to swiftly mitigate potential threats by identifying exposed data.
- Proactively enhance security: Even if you haven't experienced a data breach, your personal information could still circulate on the dark web. Monitoring enables you to detect leaked credentials before they are exploited, empowering you to prevent potential attacks.
Dark web threat intelligence partner
ManageEngine partners with Constella Intelligence for this integration. Constella Intelligence is a leading global digital risk protection business that works in partnership with some of the world's largest organizations to safeguard what matters most and defeat digital risk. Its solutions are broad, collaborative, and scalable, powered by a unique combination of proprietary data, technology, and human expertise—including the largest breach data collection on the planet, with over 100 billion attributes and 45 billion curated identity records spanning 125 countries and 53 languages.


