As the attack surface widens, and the attacks become more sophisticated, the weight of the battle against cyberattackers falls on the security operation centers (SOC). SOCs can reinforce an organization's security posture by utilizing a security orchestration, automation and response (SOAR) platform. This collection of compatible security-focused software accelerates incident investigation and response. A SOAR platform increases visibility to all security data, streamlines IT processes, automates security-related manual tasks, reduces redundant and repetitive work, and improves collaboration between security tools.
Why choose ManageEngine Log360 for SOAR?
Security orchestration

Gather security data seamlessly from various sources in your network including Active Directory (AD) users, groups, organizational units; network devices such as firewalls, servers, endpoints; and applications such as vulnerability scanners, data loss prevention software, threat applications, and more. Log360 provides meaningful security context to the data to identify security events quickly and accurately.
Ensure accountability for incident resolution by utilizing ticketing tool integration to assign detected incidents to security administrators. Log360 allows configuration of external help desk solutions, such as ServiceNow, ManageEngine ServiceDesk Plus, Jira Service Desk, Zendesk, Kayako, and BMC Remedy Service Desk.
Security automation

With prebuilt workflows for common use cases, Log360 enables you to automate incident response across your security and IT processes.
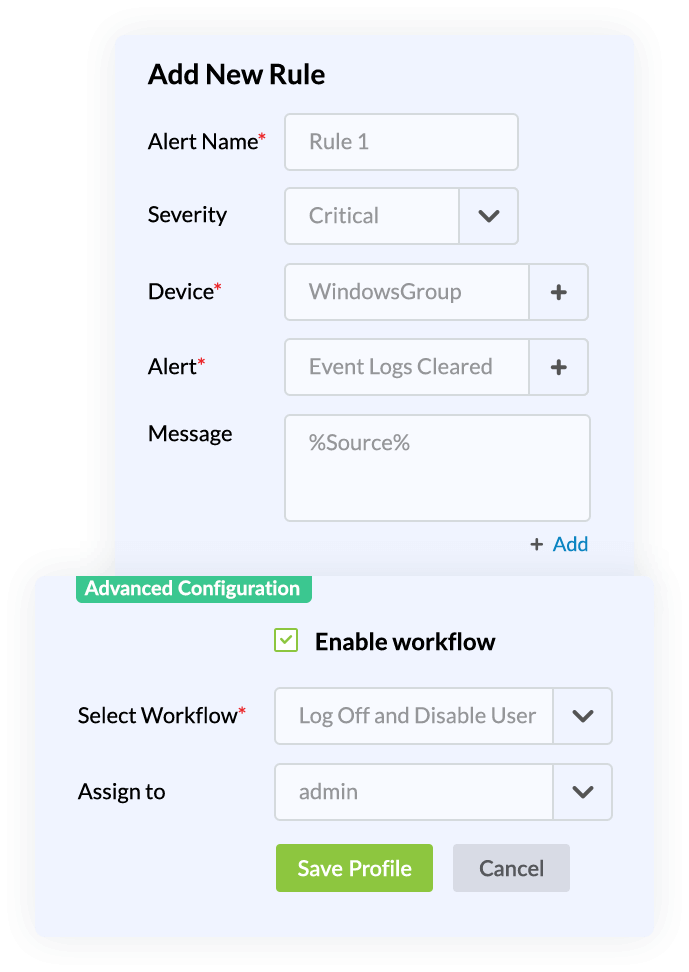
Ensure that no critical security incidents slip through the cracks by automating ticket assignment and workflow execution in Log360. For instance, you can enable a workflow related to event logs that triggers an alert and automatically assigns a ticket to a security admin.
Security remediation
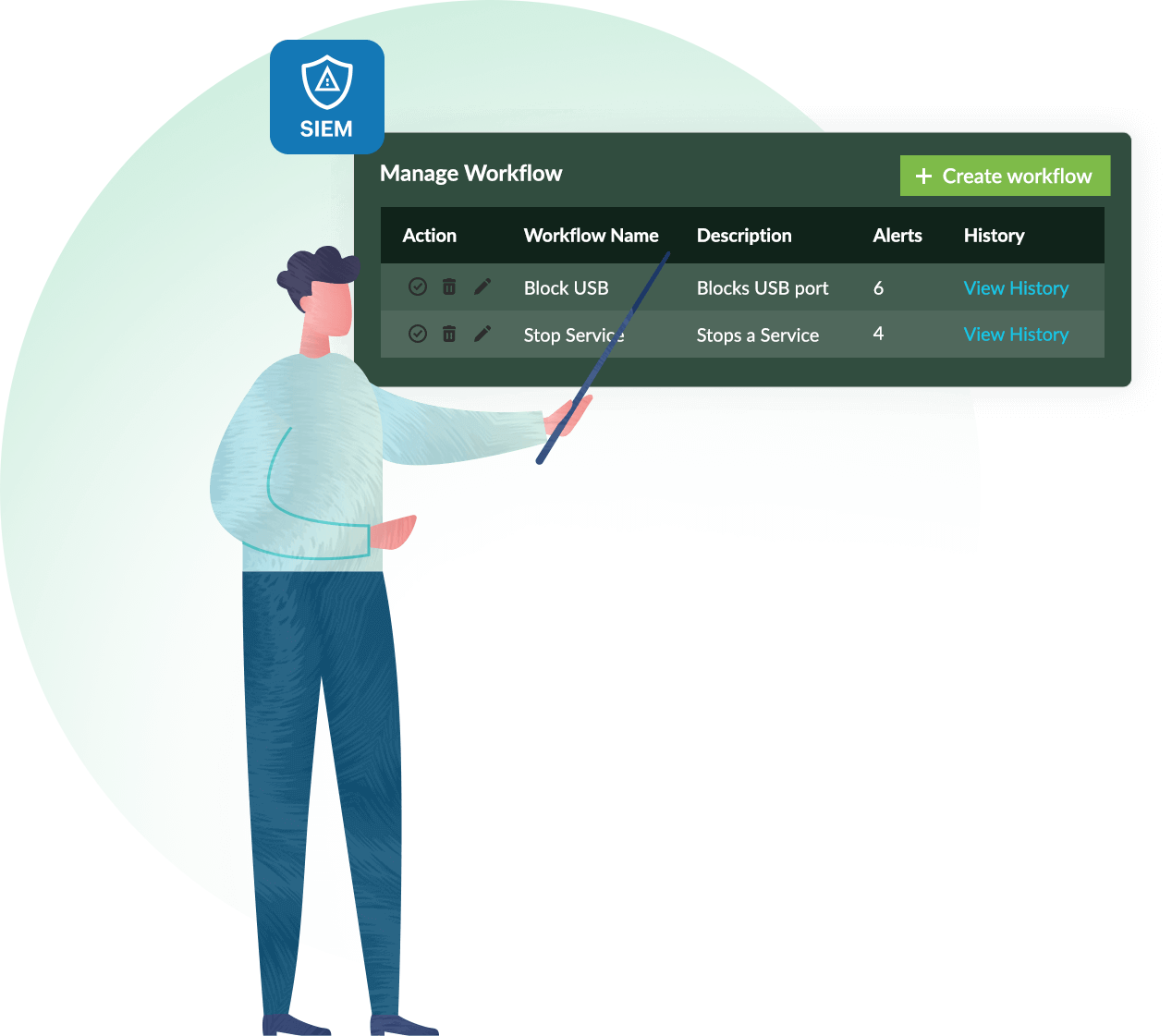
Log360's incident response management reduces the workload for your SOC by automatically executing a series of common remedial measures based on the type of security incident detected in your environment. Automating incident workflows helps contain potential long-lasting security damage to your network, reduces alert response times, and increases SOC efficiency so the team can tackle other challenges.
When alerts are triggered, automate response workflows to mitigate network security incidents before they cause any damage or result in a breach. Log360 provides prebuilt workflow profiles to initiate quick and accurate security responses. You can also associate workflows to alert profiles, correlation alerts, and other security alarms to automate threat remediation.
Automate incident workflows that stop critical security threats from exploiting your organization's assets. With Log360's incident response module, you can:
- Disable or delete a potentially compromised AD user or computer in your AD environment.
- Terminate a process on a potentially compromised Windows device.
- Log off and disable a potentially compromised Windows user account.
- Display a pop-up alert on the affected device.
- Stop a service on a potentially compromised device.
- Ping a device to check connectivity within your network.
- Run a trace route function to a device in your network to identify the path.
- Perform Cisco ASA firewall actions, such as adding inbound and outbound rules.
- Shut down or restart a potentially compromised Linux device.
- Execute a specified script file on a Linux device.
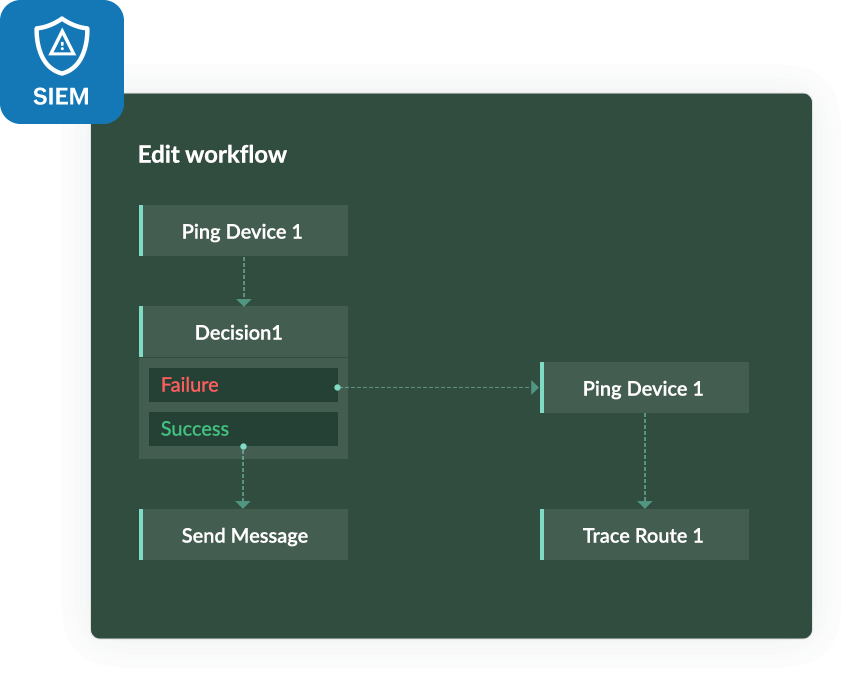
With Log360, you can build incident workflows based on your security requirements using the custom workflow builder. Utilize the simple drag-and-drop interface to link consecutive actions, construct the flow based on the success or failure of the previous action, execute time delays, and more.
Supported applications for workflow integration
Log360 supports seamless workflow integration with different applications and platforms including

Network
events
threats
threats
workflows
tickets
threats
5 reasons
Log360 is the best SIEM solution for your SOC
Attack mitigation
Mitigate security threats effectively by automating your incident response and creating incident workflows that sync with alerts. Speed up threat mitigation by integrating the process with ITIL solutions to ensure accountability for incident resolution.
Real-time security monitoring
Monitor all security events compiled from your Windows and Linux/Unix machines; IIS and Apache web servers; SQL and Oracle databases; and perimeter security devices such as routers, switches, firewalls, intrusion detection systems, and intrusion prevention systems in real time through interactive dashboards, out-of-the-box reports, and graphs.
Instant threat detection
Uncover security threats accurately with Log360's various techniques such as event log correlation, threat feed analysis to identify malicious IPs and URLs, and machine learning combined with user behavior analysis to identify insider threats.
Integrated compliance management
Monitor and analyze your log data for security breaches, and meet regulatory compliance requirements with compliance reports for PCI DSS, FISMA, GLBA, SOX, HIPAA, ISO 27001, and more.
Proactive threat hunting
Find malicious actors and potential hidden attacks that have slipped through your initial security defenses by leveraging insights into attackers’ tactics, techniques, and procedures (TTP) and advanced threat analytics.
Loved by critics and users alike
One of the best-rated log management solutionsAwards and recognitions
We strive for excellence to provide your organization with the best security. Our commitment to innovate constantly and ensure customer satisfaction has earned us some awards and recognitions. Here are a few of the accolades from 2023-2024.
Niche Player in the 2024 Gartner Magic Quadrant for Security Information and Event Management
Contender in Extended Detection and Response (XDR) in the ISG Provider Lens Cybersecurity - Solutions and Services, 2023
Challenger in KuppingerCole's Leadership Compass: Data Leakage Prevention, 2023t
Challenger and Outperformer in the GigaOm Radar for Autonomous SOC, 2023
Customer's Choice in the Peer Insights 'Voice of the Customer': Security Information and Event Management, 2023
Stay compliant with ManageEngine Log360
© 2022. Zoho Corporation Pvt. Ltd. All Rights Reserved.

