Failover is an application High Availability (HA) mode that facilitates automatic switching to a secondary/ backup server when the primary system breaks down, or is unavailable due to maintenance. Configuring failover support for Applications Manager not only helps achieve uninterrupted availability, but also ensure hassle-free monitoring of mission-critical servers that may be important to your business.
Applications Manager HA / Failover is available by default for Professional and Enterprise Editions.
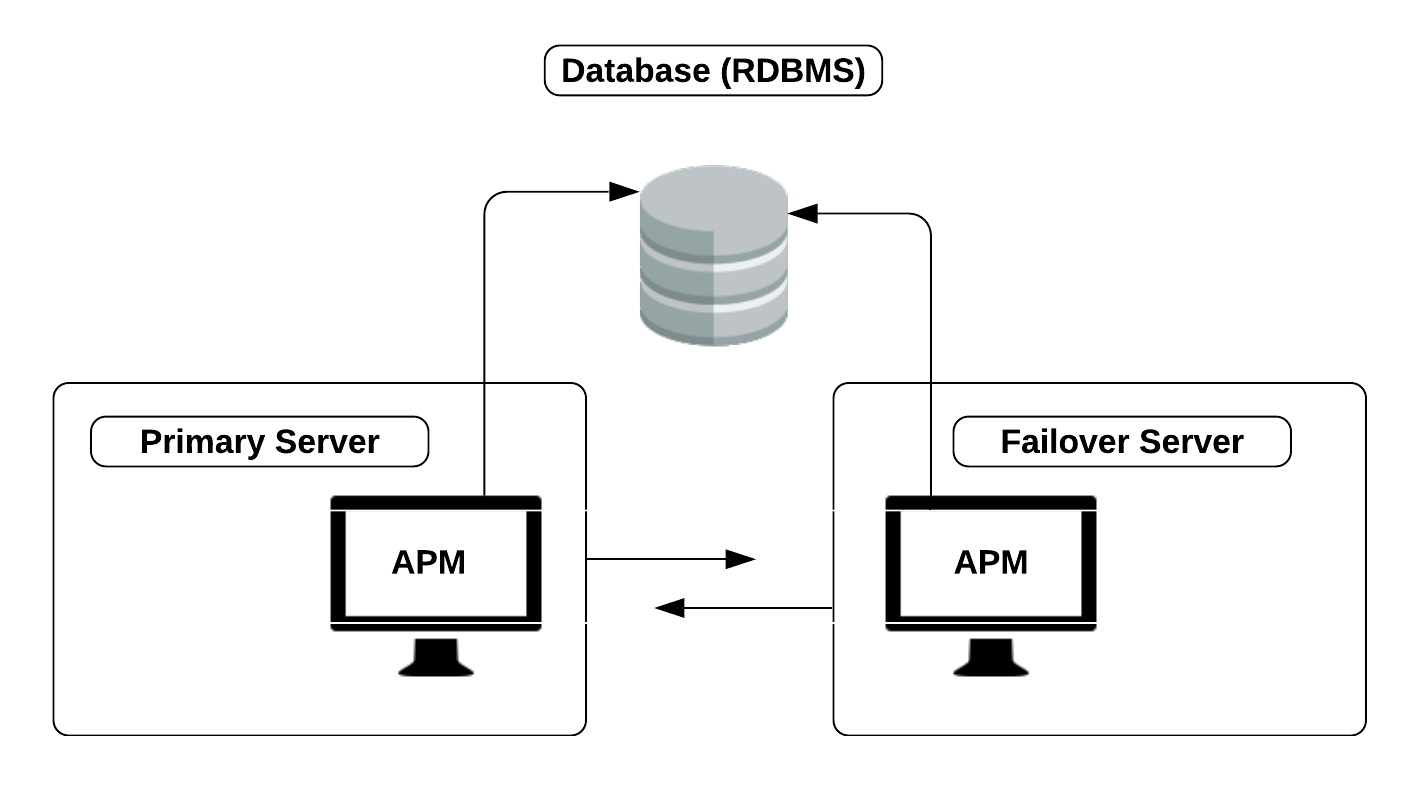
Applications Manager's failover is a dual server, single database system. There are two servers - a primary server and a secondary server along with a common database. Every time the primary server interacts with the database, the secondary server listens. If for some reason, there have been no interactions between the primary server and the database (and if an entry has not been added in the failover table in the last 60 seconds), the secondary server understands that there might be a problem and hence automatically starts acting as the primary server. Once the primary server has been restarted, it then starts acting as the secondary server.
When failover happens and the secondary server becomes active, the IP of the primary server might have changed and you will have to access the IP of the secondary server which will now act as the primary server.
Note: It is recommended that you enable replication for the backend database to avoid sudden database unavailability and minimize downtime as much as possible.
Following are the prerequisites that need to be implemented before configuring failover:
Browse through the following links to learn more about configuring failover in various environments:
Thank you for your feedback!