Just-In-Time Access
Table of contents
Just-In-Time Access Explained
Just-in-Time (JIT) access in Endpoint Central allows administrators to grant temporary, limited privileges to devices for specific tasks. This reduces security risks associated with providing continuous administrative rights and allows for granular control over application access and elevation policies. With JIT access, users are granted access only when they need it and for the specific tasks they require for a limited period of time. It can also be configured to be applied only to specific applications based on a wide range of criteria.
The Importance of Just-In-Time Access
JIT access enhances security by granting limited, temporary privileges. It effectively minimizes the potential for unauthorized access and reduces the risk of insider threats. This approach ensures that endpoints have the required access to perform their tasks without compromising overall security by granting continuous administrative rights. Implementing JIT access is a strategic decision that can strengthen the organization's security posture and minimizes the potential for data breaches.
Configuring Just-In-Time Access
The temporary access can be provided to specific computers through the following steps:
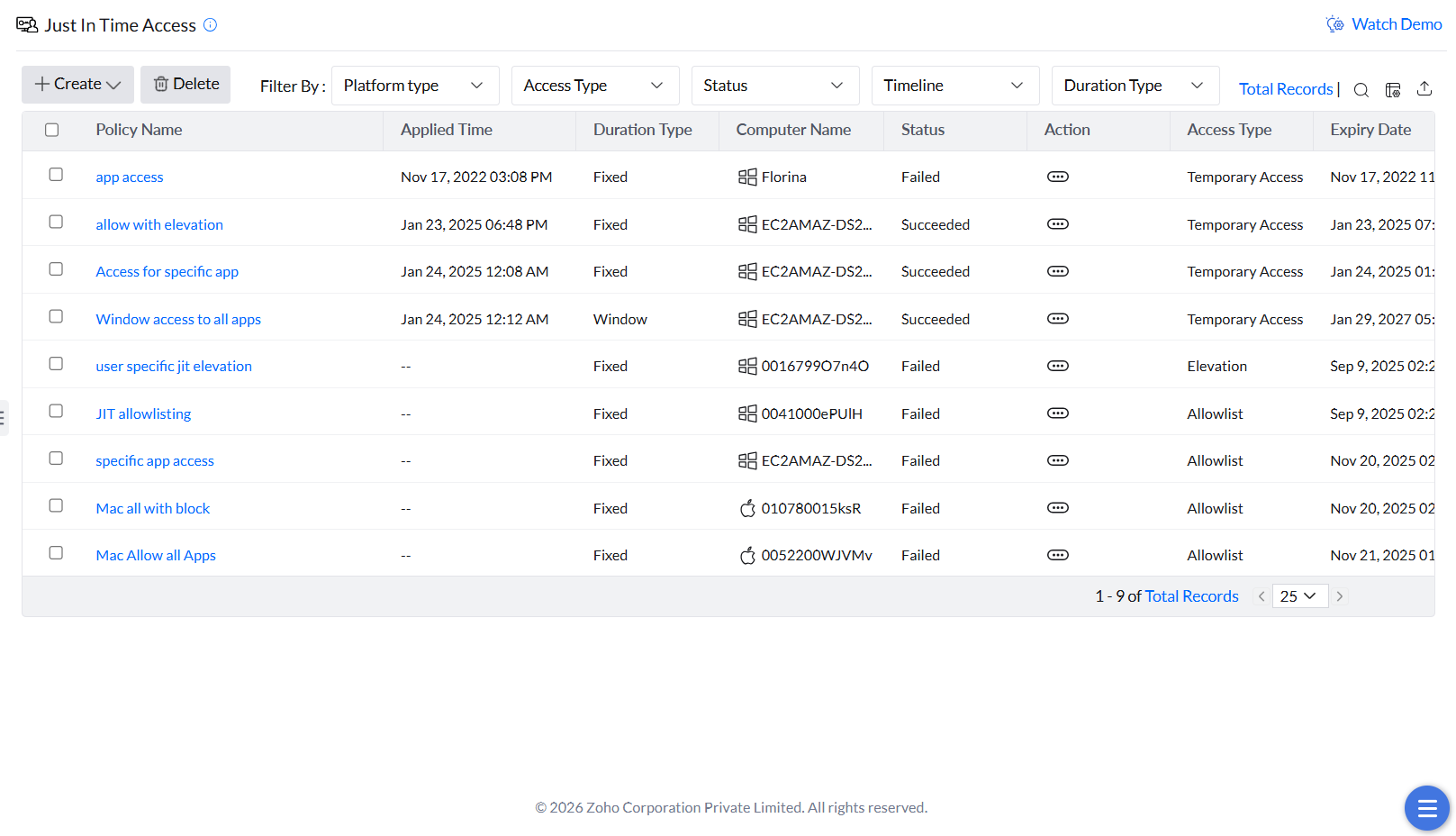
- Navigate to Application Control -> Just in Time Access.
- Click Create to delegate a new JIT access policy and select Application Allowlisting.
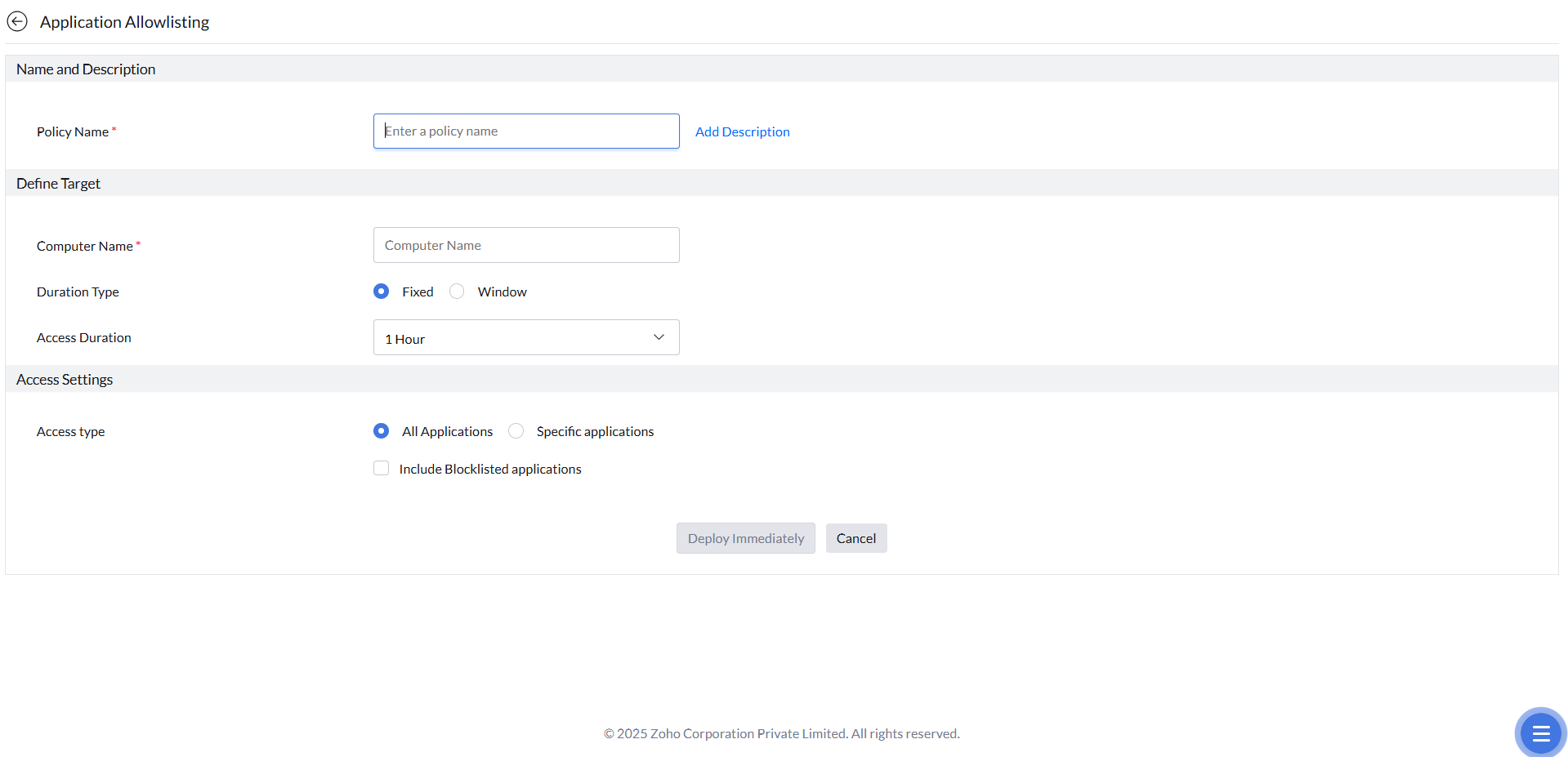
- Provide the Name and Description for the policy.
- Provide the Computer Name for which you want to provide JIT access.
Select the duration type: Fixed or Window. If the duration type is fixed, provide the duration of access and if it's a window, provide a window time frame for which you want to provide the JIT Access.
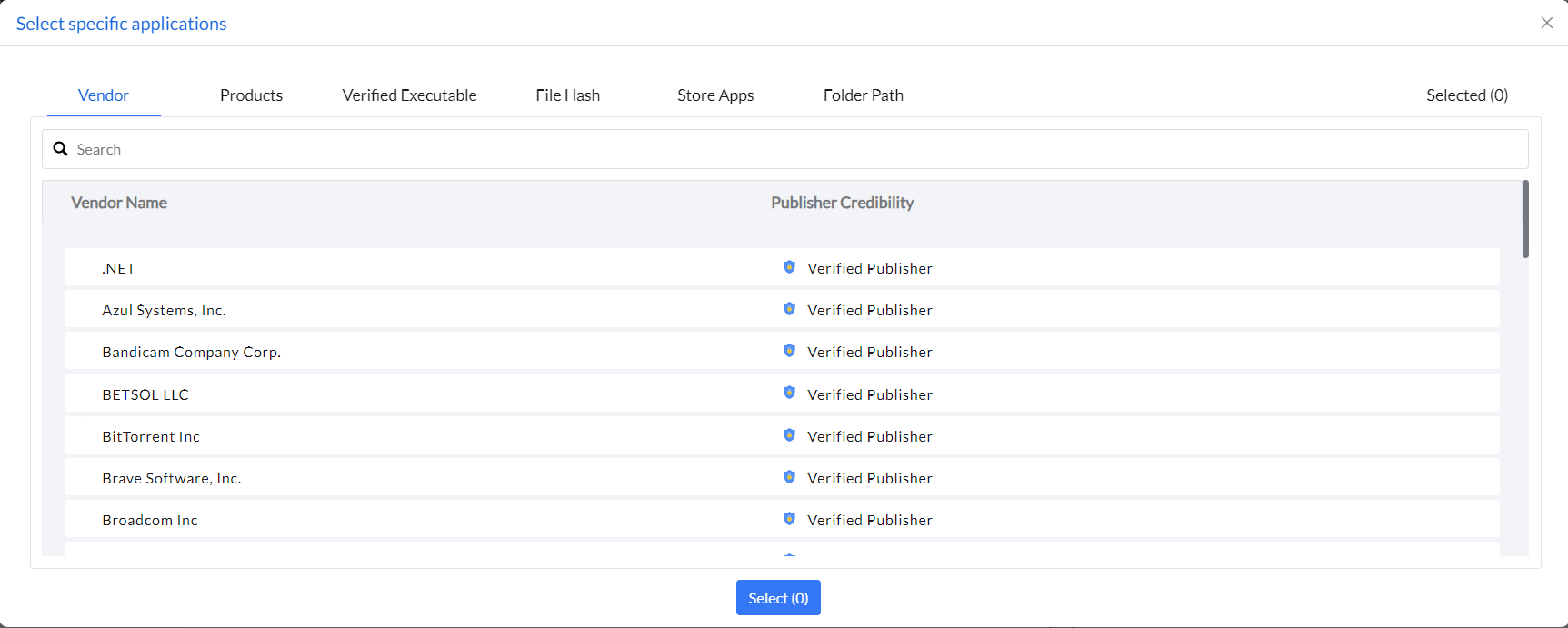
In the Access Settings, select the required option which lets users run unmanaged applications, even in Strict Mode. If you choose All Applications, the user can access any unmanaged application. Selecting Include Blocklisted Applications allows them to use apps that are blocked. If you choose Specific applications, the user can access only the applications selected. The specific applications for application allowlisting and elevation can be added using the rule types such as Vendor, Products, Verified Executable, File Hash, Store Apps, and Folder Path.
Note: The Specific applications option is currently supported on Windows only.- Click Deploy Immediately.
Just-In-Time Events Report
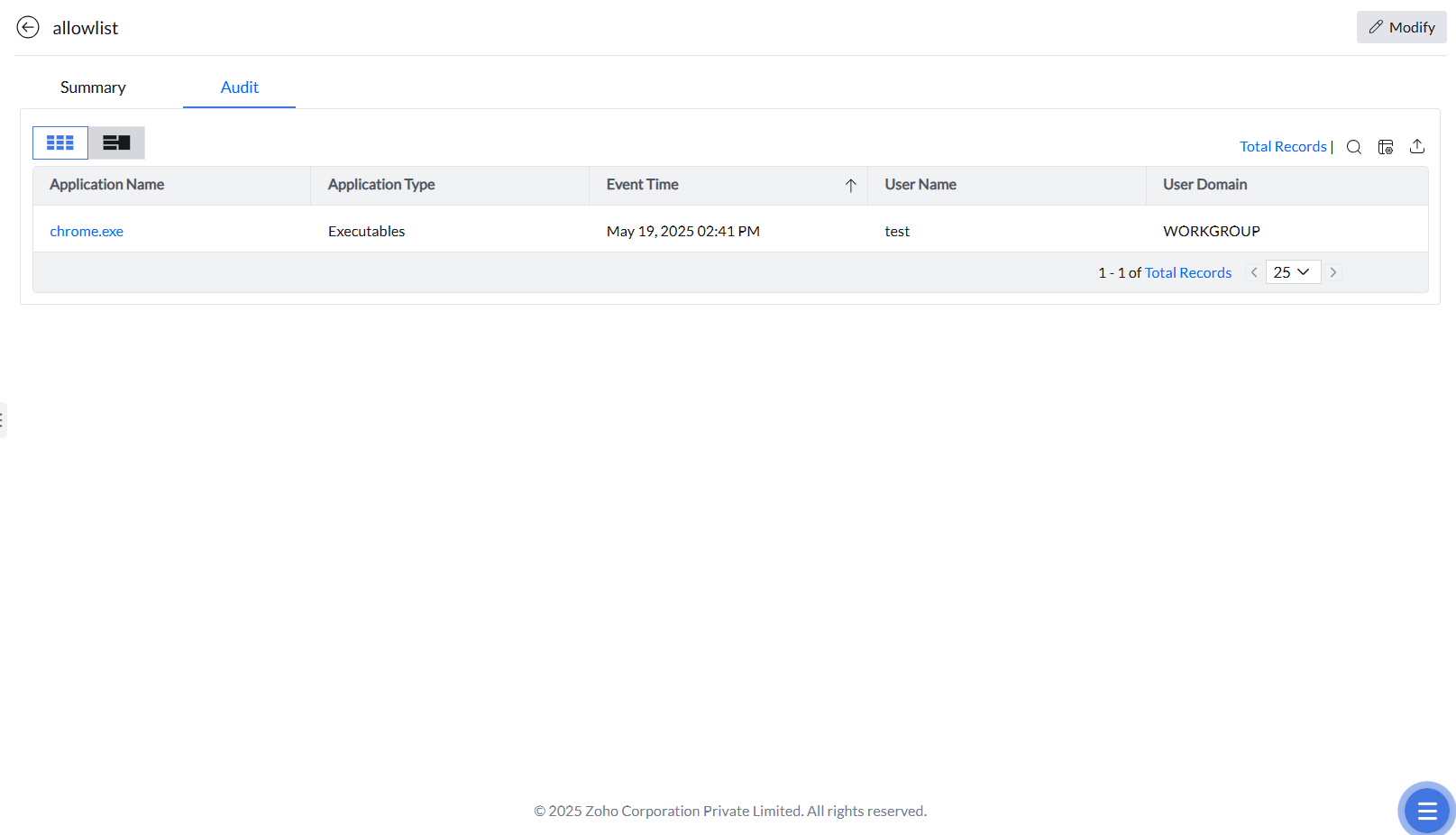
The events occurring under each JIT policy are accessible by clicking the desired policy and selecting the Audit tab.